[SCTF2019]babyre
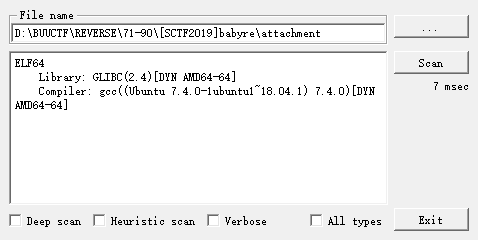
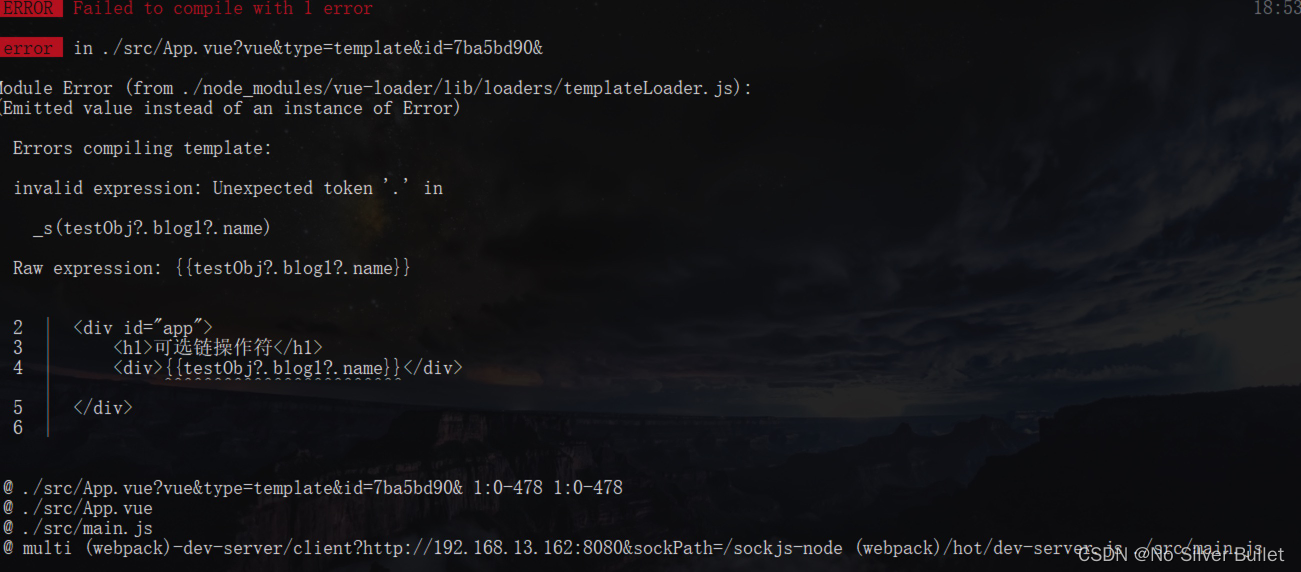
反编译失败, 有花指令
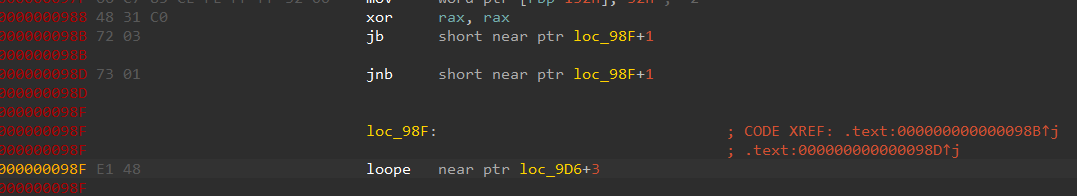
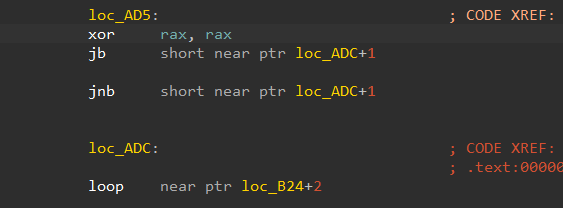
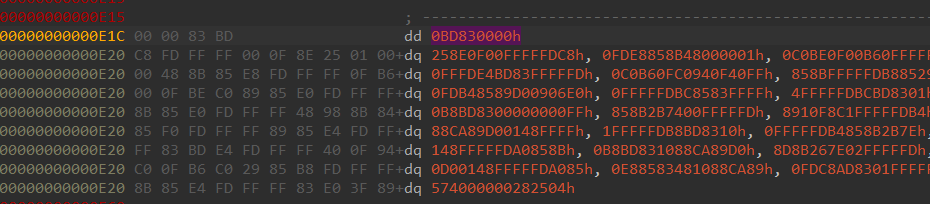
有一个无用字节, 阻止反编译, patch成0x90
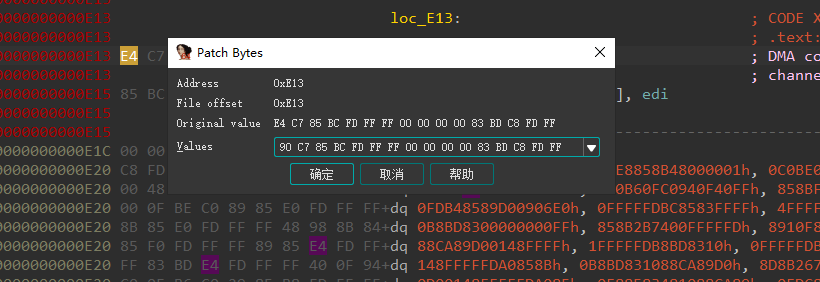
所有标红的地方nop掉之后按p重申函数main和loc_C22, F5成功
int __cdecl main(int argc, const char **argv, const char **envp)
{
char v4; // [rsp+Fh] [rbp-151h]
int v5; // [rsp+10h] [rbp-150h]
int v6; // [rsp+14h] [rbp-14Ch]
char *v7; // [rsp+18h] [rbp-148h]
char v8[10]; // [rsp+26h] [rbp-13Ah] BYREF
_QWORD v9[2]; // [rsp+30h] [rbp-130h] BYREF
int v10; // [rsp+40h] [rbp-120h]
__int64 v11[3]; // [rsp+50h] [rbp-110h] BYREF
char v12; // [rsp+68h] [rbp-F8h]
__int64 v13[3]; // [rsp+70h] [rbp-F0h] BYREF
char v14; // [rsp+88h] [rbp-D8h]
__int64 v15[6]; // [rsp+90h] [rbp-D0h] BYREF
__int16 v16; // [rsp+C0h] [rbp-A0h]
char v17[136]; // [rsp+D0h] [rbp-90h] BYREF
unsigned __int64 v18; // [rsp+158h] [rbp-8h]
v18 = __readfsqword(0x28u);
v5 = 0;
memset(v11, 0, sizeof(v11));
v12 = 0;
memset(v13, 0, sizeof(v13));
v14 = 0;
memset(v15, 0, sizeof(v15));
v16 = 0;
strcpy(
v17,
"**************.****.**s..*..******.****.***********..***..**..#*..***..***.********************.**..*******..**...*..*.*.**.*");
v9[0] = 0LL;
v9[1] = 0LL;
v10 = 0;
v7 = &v17[22];
strcpy(v8, "sctf_9102");
puts((const char *)(unsigned int)"plz tell me the shortest password1:");
scanf("%s", v15);
v6 = 1;
while ( v6 )
{
v4 = *((_BYTE *)v15 + v5);
switch ( v4 )
{
case 'w':
v7 -= 5;
break;
case 's':
v7 += 5;
break;
case 'd':
++v7;
break;
case 'a':
--v7;
break;
case 'x':
v7 += 25;
break;
case 'y':
v7 -= 25;
break;
default:
v6 = 0;
break;
}
++v5;
if ( *v7 != 46 && *v7 != 35 )
v6 = 0;
if ( *v7 == 35 )
{
puts("good!you find the right way!\nBut there is another challenge!");
break;
}
}
if ( v6 )
{
puts((const char *)(unsigned int)"plz tell me the password2:");
scanf("%s", v11);
sub_C22(v11, v13);
if ( (unsigned int)sub_F67(v13, v8) == 1 )
{
puts("Congratulation!");
puts((const char *)(unsigned int)"Now,this is the last!");
puts("plz tell me the password3:");
scanf("%s", v9);
if ( (unsigned int)sub_FFA(v9) == 1 )
{
puts("Congratulation!Here is your flag!:");
printf("sctf{%s-%s(%s)}", (const char *)v15, (const char *)v11, (const char *)v9);
}
else
{
printf("something srong...");
}
return 0;
}
else
{
printf("sorry,somthing wrong...");
return 0;
}
}
else
{
printf("sorry,is't not a right way...");
return 0;
}
}
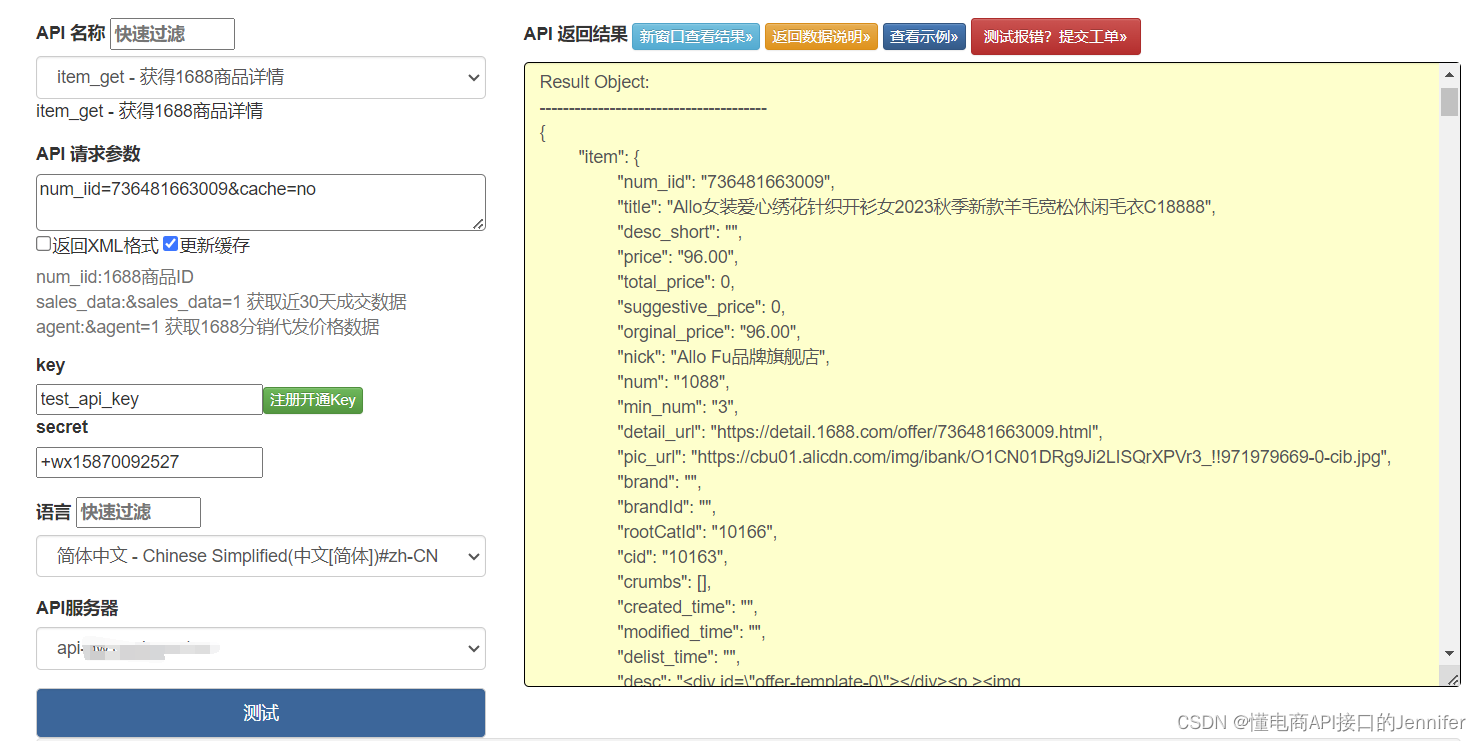
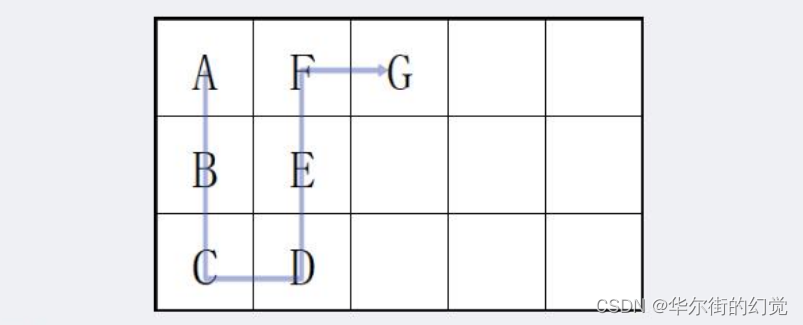
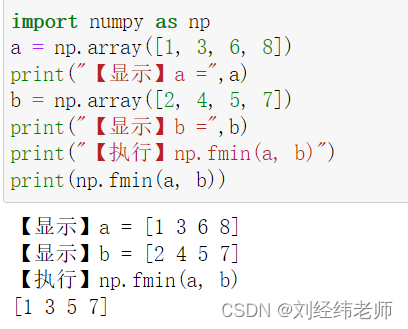
分成三个阶段分别验证, 第一个阶段是走迷宫, 根据地图从s到#
wasd分别是上左下右, xy分别是上下一层
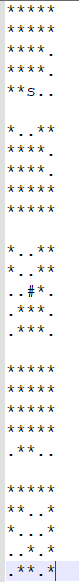
ddwwxxssxaxwwaasasyywwdd
二阶段
unsigned __int64 __fastcall sub_C22(const char *passwd2, __int64 tmp_str)
{
int v2; // eax
int v3; // eax
int v4; // eax
int v6; // [rsp+14h] [rbp-24Ch]
int v7; // [rsp+18h] [rbp-248h]
int v8; // [rsp+1Ch] [rbp-244h]
int v9; // [rsp+20h] [rbp-240h]
int v10; // [rsp+24h] [rbp-23Ch]
int v11; // [rsp+28h] [rbp-238h]
int v12; // [rsp+2Ch] [rbp-234h]
const char *v13; // [rsp+48h] [rbp-218h]
int v14[130]; // [rsp+50h] [rbp-210h] BYREF
unsigned __int64 v15; // [rsp+258h] [rbp-8h]
v15 = __readfsqword(0x28u);
qmemcpy(v14, &unk_1740, 0x200uLL);
v7 = 3;
v6 = 0;
v9 = 0;
v10 = 0;
v11 = strlen(passwd2);
v13 = passwd2;
while ( 1 )
{
v12 = 0;
if ( v9 < v11 )
break;
LABEL_7:
if ( v9 >= v11 )
goto LABEL_8;
}
do
{
if ( passwd2[v9] != 25 )
break;
++v9;
++v12;
}
while ( v9 < v11 );
if ( v9 != v11 )
{
++v9;
goto LABEL_7;
}
LABEL_8:
v8 = 0;
while ( v11 > 0 )
{
v7 -= v14[*v13] == '@';
v6 = v14[*v13] & '?' | (v6 << 6);
if ( ++v8 == 4 )
{
v8 = 0;
if ( v7 )
{
v2 = v10++;
*(_BYTE *)(v2 + tmp_str) = BYTE2(v6);
}
if ( v7 > 1 )
{
v3 = v10++;
*(_BYTE *)(v3 + tmp_str) = BYTE1(v6);
}
if ( v7 > 2 )
{
v4 = v10++;
*(_BYTE *)(v4 + tmp_str) = v6;
}
}
++v13;
--v11;
}
return __readfsqword(0x28u) ^ v15;
}
直接爆破
#include <stdio.h>
unsigned int data[128] = {
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x7F, 0x7F, 0x3E, 0x7F, 0x7F, 0x7F, 0x3F,
0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3A, 0x3B,
0x3C, 0x3D, 0x7F, 0x7F, 0x7F, 0x40, 0x7F, 0x7F,
0x7F, 0x00, 0x01, 0x02, 0x03, 0x04, 0x05, 0x06,
0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E,
0x0F, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16,
0x17, 0x18, 0x19, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F,
0x7F, 0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F, 0x20,
0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27, 0x28,
0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30,
0x31, 0x32, 0x33, 0x7F, 0x7F, 0x7F, 0x7F, 0x7F
};
int main()
{
int shuju[3] = { 0x736374,0x665f39,0x313032 };
int i0, i1, i2, i3, i4, i5;
for (i0 = 0; i0 < 3; i0++)
{
for(i1=32;i1<128;i1++)
for (i2 = 32; i2 < 128; i2++)
for (i3 = 32; i3 < 128; i3++)
for (i4 = 32; i4 < 128; i4++)
{
i5 = (((((data[i1] << 6) | data[i2]) << 6) | data[i3]) << 6) | data[i4];
if (i5 == shuju[i0])
printf("%d: %c%c%c%c\n", i0+1,i1, i2, i3, i4);
}
}
return 0;
}
/*
1: c2N0
2: Zl85
3: MS=y
3: MT=y
3: MTAy
c2N0Zl85MTAy
*/
三阶段是各种xor处理
__int64 __fastcall check_passwd3(char *passwd3)
{
int idx_4; // [rsp+18h] [rbp-158h]
int i; // [rsp+18h] [rbp-158h]
int v4; // [rsp+1Ch] [rbp-154h]
unsigned int v5; // [rsp+24h] [rbp-14Ch]
unsigned int v6; // [rsp+28h] [rbp-148h]
unsigned int v7; // [rsp+2Ch] [rbp-144h]
int v8[16]; // [rsp+30h] [rbp-140h]
int v9[16]; // [rsp+70h] [rbp-100h]
int v10[26]; // [rsp+B0h] [rbp-C0h]
unsigned int v11[4]; // [rsp+118h] [rbp-58h]
unsigned __int64 v12; // [rsp+168h] [rbp-8h]
v12 = __readfsqword(0x28u);
v8[0] = 190;
v8[1] = 4;
v8[2] = 6;
v8[3] = 128;
v8[4] = 197;
v8[5] = 175;
v8[6] = 118;
v8[7] = 71;
v8[8] = 159;
v8[9] = 204;
v8[10] = 64;
v8[11] = 31;
v8[12] = 216;
v8[13] = 191;
v8[14] = 146;
v8[15] = 239;
v5 = (passwd3[6] << 8) | (passwd3[5] << 16) | (passwd3[4] << 24) | passwd3[7];
v6 = (passwd3[10] << 8) | (passwd3[9] << 16) | (passwd3[8] << 24) | passwd3[11];
v7 = (passwd3[14] << 8) | (passwd3[13] << 16) | (passwd3[12] << 24) | passwd3[15];
v4 = 0;
idx_4 = 4;
v10[0] = ((__int64 (__fastcall *)(_QWORD))func_byte_swap)((passwd3[2] << 8) | (passwd3[1] << 16) | (*passwd3 << 24) | (unsigned int)passwd3[3]);
v10[1] = ((__int64 (__fastcall *)(_QWORD))func_byte_swap)(v5);
v10[2] = ((__int64 (__fastcall *)(_QWORD))func_byte_swap)(v6);
v10[3] = ((__int64 (__fastcall *)(_QWORD))func_byte_swap)(v7);
do
{
v10[idx_4] = xor_proce(v10[v4], v10[v4 + 1], v10[v4 + 2], v10[v4 + 3]);
++v4;
++idx_4;
}
while ( idx_4 <= 29 );
v9[0] = HIBYTE(v11[0]);
v9[1] = BYTE2(v11[0]);
v9[2] = BYTE1(v11[0]);
v9[3] = LOBYTE(v11[0]);
v9[4] = HIBYTE(v11[1]);
v9[5] = BYTE2(v11[1]);
v9[6] = BYTE1(v11[1]);
v9[7] = LOBYTE(v11[1]);
v9[8] = HIBYTE(v11[2]);
v9[9] = BYTE2(v11[2]);
v9[10] = BYTE1(v11[2]);
v9[11] = LOBYTE(v11[2]);
v9[12] = HIBYTE(v11[3]);
v9[13] = BYTE2(v11[3]);
v9[14] = BYTE1(v11[3]);
v9[15] = LOBYTE(v11[3]);
for ( i = 0; i <= 15; ++i )
{
if ( v9[i] != v8[i] )
return 0xFFFFFFFFLL;
}
return 1LL;
}
__int64 __fastcall sub_143B(int a1, int a2, int a3, unsigned int a4)
{
return a1 ^ (unsigned int)sub_1464(a2 ^ a3 ^ a4);
}
__int64 __fastcall sub_1464(unsigned int a1)
{
int v2; // [rsp+18h] [rbp-498h]
int v3[290]; // [rsp+20h] [rbp-490h] BYREF
unsigned __int64 v4; // [rsp+4A8h] [rbp-8h]
v4 = __readfsqword(0x28u);
qmemcpy(v3, &unk_1940, 0x480uLL);
v2 = (v3[BYTE2(a1)] << 16) | v3[(unsigned __int8)a1] | (v3[BYTE1(a1)] << 8) | (v3[HIBYTE(a1)] << 24);
return __ROL4__(v2, 12) ^ (unsigned int)(__ROL4__(v2, 8) ^ __ROR4__(v2, 2)) ^ __ROR4__(v2, 6);
}
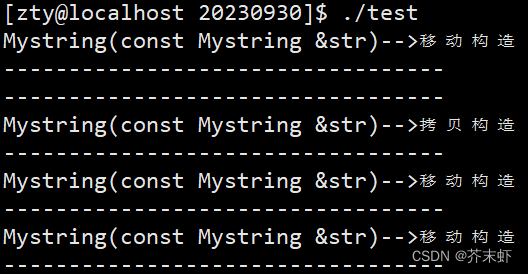
func_byte_swap是大小端序调换, 写逆的时候v8按大端序来储存, 这样逆回去正好对上
可以直接逆回去, 需要用到IDA的宏, 这个defs.h头文件可以在ida安装目录下plugins/hexrays_sdk/include文件夹下找到
#include <stdio.h>
#include "defs.h"
unsigned int ROR4(unsigned int x, int y)
{
return (x << (32 - y) | x >> y) & 0xffffffff;
}
unsigned int ROL4(unsigned int x, int y)
{
return (x >> (32 - y) | x << y) & 0xffffffff;
}
unsigned int v3[288] = {
0xD6, 0x90, 0xE9, 0xFE, 0xCC, 0xE1, 0x3D, 0xB7,
0x16, 0xB6, 0x14, 0xC2, 0x28, 0xFB, 0x2C, 0x05,
0x2B, 0x67, 0x9A, 0x76, 0x2A, 0xBE, 0x04, 0xC3,
0xAA, 0x44, 0x13, 0x26, 0x49, 0x86, 0x06, 0x99,
0x9C, 0x42, 0x50, 0xF4, 0x91, 0xEF, 0x98, 0x7A,
0x33, 0x54, 0x0B, 0x43, 0xED, 0xCF, 0xAC, 0x62,
0xE4, 0xB3, 0x1C, 0xA9, 0xC9, 0x08, 0xE8, 0x95,
0x80, 0xDF, 0x94, 0xFA, 0x75, 0x8F, 0x3F, 0xA6,
0x47, 0x07, 0xA7, 0xFC, 0xF3, 0x73, 0x17, 0xBA,
0x83, 0x59, 0x3C, 0x19, 0xE6, 0x85, 0x4F, 0xA8,
0x68, 0x6B, 0x81, 0xB2, 0x71, 0x64, 0xDA, 0x8B,
0xF8, 0xEB, 0x0F, 0x4B, 0x70, 0x56, 0x9D, 0x35,
0x1E, 0x24, 0x0E, 0x5E, 0x63, 0x58, 0xD1, 0xA2,
0x25, 0x22, 0x7C, 0x3B, 0x01, 0x21, 0x78, 0x87,
0xD4, 0x00, 0x46, 0x57, 0x9F, 0xD3, 0x27, 0x52,
0x4C, 0x36, 0x02, 0xE7, 0xA0, 0xC4, 0xC8, 0x9E,
0xEA, 0xBF, 0x8A, 0xD2, 0x40, 0xC7, 0x38, 0xB5,
0xA3, 0xF7, 0xF2, 0xCE, 0xF9, 0x61, 0x15, 0xA1,
0xE0, 0xAE, 0x5D, 0xA4, 0x9B, 0x34, 0x1A, 0x55,
0xAD, 0x93, 0x32, 0x30, 0xF5, 0x8C, 0xB1, 0xE3,
0x1D, 0xF6, 0xE2, 0x2E, 0x82, 0x66, 0xCA, 0x60,
0xC0, 0x29, 0x23, 0xAB, 0x0D, 0x53, 0x4E, 0x6F,
0xD5, 0xDB, 0x37, 0x45, 0xDE, 0xFD, 0x8E, 0x2F,
0x03, 0xFF, 0x6A, 0x72, 0x6D, 0x6C, 0x5B, 0x51,
0x8D, 0x1B, 0xAF, 0x92, 0xBB, 0xDD, 0xBC, 0x7F,
0x11, 0xD9, 0x5C, 0x41, 0x1F, 0x10, 0x5A, 0xD8,
0x0A, 0xC1, 0x31, 0x88, 0xA5, 0xCD, 0x7B, 0xBD,
0x2D, 0x74, 0xD0, 0x12, 0xB8, 0xE5, 0xB4, 0xB0,
0x89, 0x69, 0x97, 0x4A, 0x0C, 0x96, 0x77, 0x7E,
0x65, 0xB9, 0xF1, 0x09, 0xC5, 0x6E, 0xC6, 0x84,
0x18, 0xF0, 0x7D, 0xEC, 0x3A, 0xDC, 0x4D, 0x20,
0x79, 0xEE, 0x5F, 0x3E, 0xD7, 0xCB, 0x39, 0x48,
0xC6, 0xBA, 0xB1, 0xA3, 0x50, 0x33, 0xAA, 0x56,
0x97, 0x91, 0x7D, 0x67, 0xDC, 0x22, 0x70, 0xB2,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00
};
__int64 sub_1464(unsigned int a1)
{
int v2;
v2 = (v3[BYTE2(a1)] << 16) | v3[(unsigned __int8)a1] | (v3[BYTE1(a1)] << 8) | (v3[HIBYTE(a1) ] << 24);
return ROL4(v2, 12) ^ (unsigned int)(ROL4(v2, 8) ^ ROR4(v2, 2)) ^ ROR4(v2, 6);
}
int main()
{
int n = 25;
unsigned int v10[30] = { 0 };
v10[26] = 0xBE040680;
v10[27] = 0xC5AF7647;
v10[28] = 0x9FCC401F;
v10[29] = 0xD8BF92EF;
do {
v10[n] =v10[n + 4] ^ sub_1464(v10[n + 1] ^ v10[n + 2] ^ v10[n + 3]);
--n;
} while (n >= 0);
for (int i = 0; i < 4; i++)
printf("%c%c%c%c", ((char*)&v10[i])[0], ((char*)&v10[i])[1], ((char*)&v10[i])[2], ((char*)&v10[i])[3]);
return 0;
}
/*
fl4g_is_s0_ug1y!
*/
运行程序, 把三个阶段对应的password输入, 就得flag
[FlareOn2]very_success
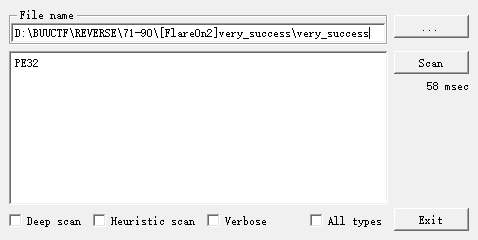
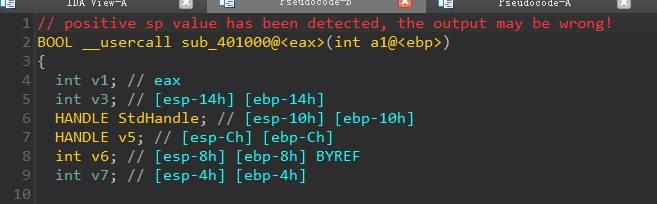
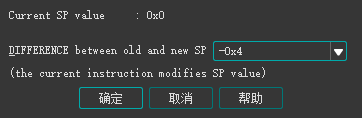
栈帧不平衡, alt+k调整, 再F5就行
BOOL __usercall sub_401000@<eax>(int a1@<ebp>)
{
HANDLE StdHandle; // [esp-14h] [ebp-14h]
HANDLE v3; // [esp-10h] [ebp-10h]
int v4[3]; // [esp-Ch] [ebp-Ch] BYREF
int retaddr; // [esp+0h] [ebp+0h]
v4[1] = a1;
StdHandle = GetStdHandle(0xFFFFFFF6);
v3 = GetStdHandle(0xFFFFFFF5);
WriteFile(v3, aYouCrushedThat, 0x43u, (LPDWORD)v4, 0);
ReadFile(StdHandle, Buffer, 0x32u, (LPDWORD)v4, 0);
if ( sub_401084((int)v4, retaddr, Buffer, v4[0]) )
return WriteFile(v3, aYouAreSuccess, 0x11u, (LPDWORD)v4, 0);
else
return WriteFile(v3, aYouAreFailure, 0x11u, (LPDWORD)v4, 0);
}
int __usercall sub_401084@<eax>(int result@<eax>, int a2, char *a3, int a4)
{
__int16 v4; // bx
int length; // ecx
_BYTE *v7; // edi
char v8; // al
unsigned int v9; // kr00_4
char v10; // al
char v11; // cf
__int16 process_val; // ax
bool check_valid; // zf
_BYTE *v14; // edi
int v15; // [esp+0h] [ebp-Ch]
v4 = 0;
length = 37;
if ( a4 >= 37 )
{
v7 = (_BYTE *)(a2 + 36); // reversed arr
while ( 1 )
{
LOWORD(result) = 455;
v15 = result;
v8 = *a3++;
v9 = __readeflags();
v10 = v15 ^ v8;
__writeeflags(v9);
process_val = (unsigned __int8)(__ROL1__(1, v4 & 3) + v11 + v10);
v4 += process_val;
check_valid = *v7 == (unsigned __int8)process_val;
v14 = v7 + 1;
if ( !check_valid )
LOWORD(length) = 0;
result = v15;
if ( !length ) // invalid then break
break;
v7 = v14 - 2; // v7 = v7 - 1
if ( !--length )
return result;
}
}
return 0;
}
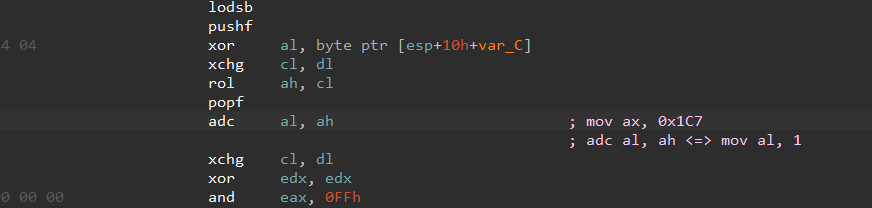
动调拿到v7数组, 逆回去就行
def rol(value, count):
temp=((value >> (8-count)) & 0xFF)|((value << count) & 0xFF)
return temp
v7 = [
0xAA, 0xEC, 0xA4, 0xBA, 0xAF, 0xAE, 0xAA, 0x8A, 0xC0, 0xA7,
0xB0, 0xBC, 0x9A, 0xBA, 0xA5, 0xA5, 0xBA, 0xAF, 0xB8, 0x9D,
0xB8, 0xF9, 0xAE, 0x9D, 0xAB, 0xB4, 0xBC, 0xB6, 0xB3, 0x90,
0x9A, 0xA8
]
v7 = v7[::-1]
v4 = 0
flag = ''
for i in range(len(v7)):
tmp = rol(1, v4 & 3)
char = (v7[i] - tmp - 1) ^ 0xC7
flag += chr(char)
v4 += v7[i]
print('flag{{{}{}}}'.format(flag, 'n.com'))
[2019红帽杯]Snake
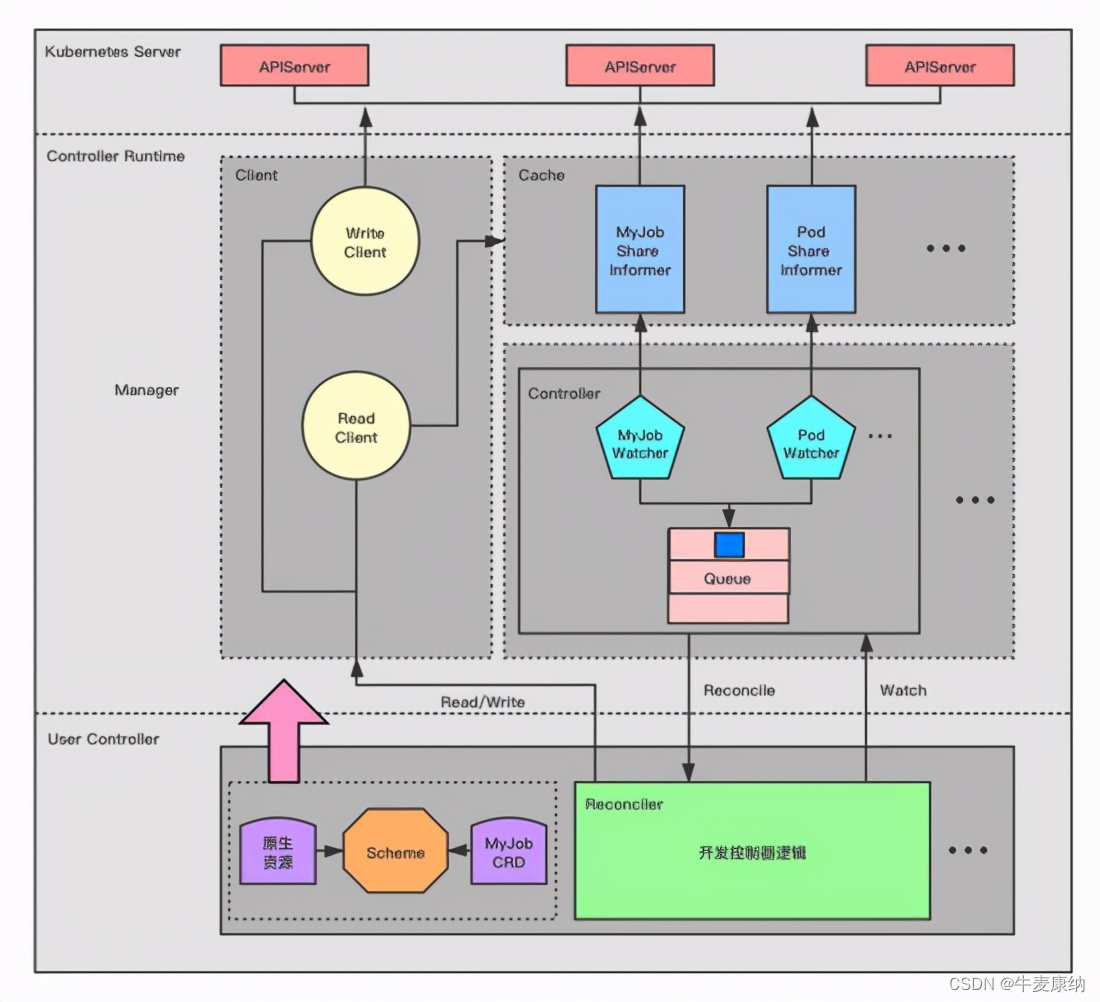
Unity逆向, Unity3D编译后有两种运行模式:C#字节码模式和AOT预编译模式, 这里的游戏代码是字节码存储, 在.\Snake_Data\Managed\Assembly-CSharp.dll, 用dnSpy64位进行反编译, 发现调用外部的Interface.dll, 用IDA逆向这个dll文件
__int64 __fastcall GameObject(int a1)
{
char v1; // di
__int64 *v2; // rbx
__int64 *v3; // rax
int v4; // r8d
int v5; // r9d
__int64 v6; // rax
_BYTE *v7; // rcx
__int64 v8; // rax
__int64 v9; // rax
__int64 *v10; // rdx
__int64 v11; // rax
__int64 *v12; // rcx
_BYTE *v13; // rcx
__int64 v15; // rax
int v16; // r8d
int v17; // r9d
__int64 v18; // rax
__int64 v19; // rax
__int64 *v20; // rdx
__int64 v21; // rax
__int64 *v22; // rcx
_BYTE *v23; // rcx
void *v24; // rcx
void *v25; // rcx
void *v26; // rcx
_BYTE *v27; // rcx
_BYTE *v28; // rcx
__int64 v29; // rax
_BYTE *v30; // rcx
__int64 v31; // rax
const void *v32; // rdx
bool v33; // bl
_BYTE *v34; // rcx
_BYTE *v35; // rcx
__int64 v36; // rax
const char *v37; // rdx
__int64 v38; // rax
__int64 v39; // rax
void *v40; // rcx
_BYTE *v41; // rcx
void *v42; // rcx
void *v43; // rcx
void *Block; // [rsp+20h] [rbp-E0h] BYREF
_BYTE *v45; // [rsp+28h] [rbp-D8h] BYREF
__m128i si128; // [rsp+30h] [rbp-D0h]
int v47; // [rsp+40h] [rbp-C0h]
int v48; // [rsp+48h] [rbp-B8h]
int v49; // [rsp+50h] [rbp-B0h] BYREF
int v50; // [rsp+58h] [rbp-A8h] BYREF
int v51; // [rsp+60h] [rbp-A0h]
int v52; // [rsp+68h] [rbp-98h]
int v53; // [rsp+70h] [rbp-90h]
__int64 *v54; // [rsp+78h] [rbp-88h] BYREF
void *Buf1[2]; // [rsp+80h] [rbp-80h]
unsigned __int64 v56; // [rsp+90h] [rbp-70h]
void *v57; // [rsp+98h] [rbp-68h] BYREF
void *v58; // [rsp+A0h] [rbp-60h] BYREF
__m128i v59; // [rsp+A8h] [rbp-58h]
unsigned __int64 v60; // [rsp+B8h] [rbp-48h]
__int64 v61; // [rsp+C0h] [rbp-40h] BYREF
void *v62; // [rsp+C8h] [rbp-38h] BYREF
_BYTE v63[24]; // [rsp+D0h] [rbp-30h]
__int64 v64; // [rsp+E8h] [rbp-18h] BYREF
_BYTE *v65; // [rsp+F0h] [rbp-10h] BYREF
__int128 v66; // [rsp+F8h] [rbp-8h]
unsigned __int64 v67; // [rsp+108h] [rbp+8h]
__int64 v68; // [rsp+110h] [rbp+10h] BYREF
void *v69[2]; // [rsp+118h] [rbp+18h] BYREF
__m128i v70; // [rsp+128h] [rbp+28h]
char v71[8]; // [rsp+138h] [rbp+38h] BYREF
void *v72[3]; // [rsp+140h] [rbp+40h] BYREF
unsigned __int64 v73; // [rsp+158h] [rbp+58h]
v48 = 0;
v1 = 0;
if ( a1 >= 0 )
{
if ( (unsigned int)(a1 - 2) <= 97 ) // 0 - 99
{
LOBYTE(Block) = 0;
si128 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
sub_180006D10(
&Block,
"1399072626417208846352501054493274635311312275165004973073110020948852453223868050494068786439822163264935277024"
"1468943993009079475334584417852835617853909482524738983614292847460710826226708785021132264080613569807620798681"
"8086837911361480181444157057782599277473843153161174504240064610043962720953514451563",
0x135ui64);
sub_180001530(v71, &Block);
LOBYTE(Block) = 0;
si128 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
sub_180006D10(
&Block,
"7998185649085699985067170036073312083199999558942120746049018587653186051852759776790516809918289134512387896640"
"3548022646956365158864209467614850251731806682037300712511185681164865174187586907707195428804234739667769742078"
"793162639867922056194688917569369338005327309973680573581158754297630654105882382426",
0x134ui64);
sub_180001530(&v61, &Block);
v15 = sub_18000A9D0(&Block);
sub_180001530(&v68, v15);
LOBYTE(Block) = v71[0];
sub_180006C40(&v45, v72);
LOBYTE(v57) = v68;
sub_180006C40(&v58, v69);
LOBYTE(v49) = v61;
sub_180006C40(&v50, &v62);
sub_180006250(&v64, &v49, &v57, &Block);
LOBYTE(v49) = v64;
sub_180006C40(&v50, &v65);
sub_18000AAB0(
(unsigned int)&v54,
(unsigned int)&v49,
v16,
v17,
(_DWORD)Block,
(_DWORD)v45,
si128.m128i_i32[0],
si128.m128i_i32[2],
v47,
v48,
v49,
v50,
v51,
v52,
v53,
(_DWORD)v54,
Buf1[0],
Buf1[1],
v56);
LOBYTE(Block) = 0;
si128 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
sub_180006D10(&Block, "flag", 4ui64);
v18 = sub_180006C40(&v57, &v54);
if ( (unsigned __int8)sub_18000AFA0(v18, &Block) )
{
v19 = sub_18000A7C0(std::cout, "You win! flag is ");
std::ostream::operator<<(v19, sub_18000A990);
v20 = (__int64 *)&v54;
if ( v56 >= 0x10 )
v20 = v54;
v21 = sub_180007570(std::cout, v20, Buf1[1]);
}
else
{
v21 = sub_18000A7C0(std::cout, "Try again");
}
std::ostream::operator<<(v21, sub_18000A990);
if ( v56 >= 0x10 )
{
v22 = v54;
if ( v56 + 1 >= 0x1000 )
{
v22 = (__int64 *)*(v54 - 1);
if ( (unsigned __int64)((char *)v54 - (char *)v22 - 8) > 0x1F )
goto LABEL_50;
}
j_j_free(v22);
}
Buf1[1] = 0i64;
v56 = 15i64;
LOBYTE(v54) = 0;
if ( v67 >= 0x10 )
{
v23 = v65;
if ( v67 + 1 >= 0x1000 )
{
v23 = (_BYTE *)*((_QWORD *)v65 - 1);
if ( (unsigned __int64)(v65 - v23 - 8) > 0x1F )
goto LABEL_50;
}
j_j_free(v23);
}
if ( v70.m128i_i64[1] >= 0x10ui64 )
{
v24 = v69[0];
if ( (unsigned __int64)(v70.m128i_i64[1] + 1) >= 0x1000 )
{
v24 = (void *)*((_QWORD *)v69[0] - 1);
if ( (unsigned __int64)(v69[0] - v24 - 8) > 0x1F )
goto LABEL_50;
}
j_j_free(v24);
}
LOBYTE(v69[0]) = 0;
v70 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
if ( *(_QWORD *)&v63[16] < 0x10ui64 )
goto LABEL_47;
v25 = v62;
if ( (unsigned __int64)(*(_QWORD *)&v63[16] + 1i64) < 0x1000
|| (v25 = (void *)*((_QWORD *)v62 - 1), (unsigned __int64)((_BYTE *)v62 - (_BYTE *)v25 - 8) <= 0x1F) )
{
j_j_free(v25);
LABEL_47:
LOBYTE(v62) = 0;
*(__m128i *)&v63[8] = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
if ( v73 >= 0x10 )
{
v26 = v72[0];
if ( v73 + 1 >= 0x1000 )
{
v26 = (void *)*((_QWORD *)v72[0] - 1);
if ( (unsigned __int64)(v72[0] - v26 - 8) > 0x1F )
goto LABEL_50;
}
j_j_free(v26);
}
return 7i64;
}
LABEL_50:
invalid_parameter_noinfo_noreturn();
}
if ( (unsigned int)(a1 - 101) > 0x62 )
return 996i64;
v68 = 0i64;
v69[0] = 0i64;
v69[1] = 0i64;
v70.m128i_i64[0] = 0i64;
v59 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
LOBYTE(v57) = 0;
sub_180006D10(
&v57,
"139907262641720884635250105449327463531131227516500497307311002094885245322386805049406878643982216326493527702414"
"689439930090794753345844178528356178539094825247389836142928474607108262267087850211322640806135698076207986818086"
"837911361480181444157057782599277473843153161174504240064610043962720953514451563",
0x135ui64);
sub_1800078F0(&v68, &v57);
if ( v59.m128i_i64[1] >= 0x10ui64 )
{
v27 = v57;
if ( (unsigned __int64)(v59.m128i_i64[1] + 1) >= 0x1000 )
{
v27 = (_BYTE *)*((_QWORD *)v57 - 1);
if ( (unsigned __int64)((_BYTE *)v57 - v27 - 8) > 0x1F )
goto LABEL_99;
}
j_j_free(v27);
}
v61 = 0i64;
v62 = 0i64;
*(_OWORD *)v63 = 0ui64;
v59 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
LOBYTE(v57) = 0;
sub_180006D10(
&v57,
"122107611316850260321590575768393047216806481837919054910332579385088745494833866045797079936947058335743437609060"
"618364037361749600119005166359303873659401522100249312696661209787316369738806133852177861917757996075304470648951"
"037632182891401322685617735478597953000103146149534977902885706852338811895661809",
0x135ui64);
sub_1800078F0(&v61, &v57);
if ( v59.m128i_i64[1] >= 0x10ui64 )
{
v28 = v57;
if ( (unsigned __int64)(v59.m128i_i64[1] + 1) >= 0x1000 )
{
v28 = (_BYTE *)*((_QWORD *)v57 - 1);
if ( (unsigned __int64)((_BYTE *)v57 - v28 - 8) > 0x1F )
goto LABEL_99;
}
j_j_free(v28);
}
v64 = 0i64;
v65 = 0i64;
v66 = 0ui64;
v29 = sub_18000A9D0(&Block);
sub_1800078F0(&v64, v29);
if ( si128.m128i_i64[1] >= 0x10ui64 )
{
v30 = Block;
if ( (unsigned __int64)(si128.m128i_i64[1] + 1) >= 0x1000 )
{
v30 = (_BYTE *)*((_QWORD *)Block - 1);
if ( (unsigned __int64)((_BYTE *)Block - v30 - 8) > 0x1F )
invalid_parameter_noinfo_noreturn();
}
j_j_free(v30);
}
v54 = 0i64;
Buf1[0] = 0i64;
Buf1[1] = 0i64;
v56 = 0i64;
sub_180009B40(&v61, &v54, &v64, &v68);
LOBYTE(v57) = 0;
v59 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
sub_180006D10(&v57, "7777777", 7ui64);
v31 = sub_1800078F0(&Block, &v57);
v33 = 0;
if ( (_BYTE)v54 == *(_BYTE *)v31 )
{
v32 = *(const void **)(v31 + 8);
if ( (((Buf1[1] - Buf1[0]) ^ (*(_QWORD *)(v31 + 16) - (_QWORD)v32)) & 0xFFFFFFFFFFFFFFFCui64) == 0
&& !memcmp(Buf1[0], v32, Buf1[1] - Buf1[0]) )
{
v33 = 1;
}
}
v34 = v45;
if ( v45 )
{
if ( ((si128.m128i_i64[1] - (_QWORD)v45) & 0xFFFFFFFFFFFFFFFCui64) >= 0x1000 )
{
v34 = (_BYTE *)*((_QWORD *)v45 - 1);
if ( (unsigned __int64)(v45 - v34 - 8) > 0x1F )
LABEL_79:
invalid_parameter_noinfo_noreturn();
}
j_j_free(v34);
v45 = 0i64;
si128 = 0i64;
}
if ( v59.m128i_i64[1] >= 0x10ui64 )
{
v35 = v57;
if ( (unsigned __int64)(v59.m128i_i64[1] + 1) >= 0x1000 )
{
v35 = (_BYTE *)*((_QWORD *)v57 - 1);
if ( (unsigned __int64)((_BYTE *)v57 - v35 - 8) > 0x1F )
goto LABEL_79;
}
j_j_free(v35);
}
if ( v33 )
{
v36 = sub_18000A7C0(std::cout, "EDG fight for S10");
std::ostream::operator<<(v36, sub_18000A990);
v37 = "You fight for the next snake";
}
else
{
v38 = sub_18000A7C0(std::cout, "EDG failed to fight for their S9");
std::ostream::operator<<(v38, sub_18000A990);
v37 = "But you can fight for next snake";
}
v39 = sub_18000A7C0(std::cout, v37);
std::ostream::operator<<(v39, sub_18000A990);
v40 = Buf1[0];
if ( Buf1[0] )
{
if ( ((v56 - (unsigned __int64)Buf1[0]) & 0xFFFFFFFFFFFFFFFCui64) >= 0x1000 )
{
v40 = (void *)*((_QWORD *)Buf1[0] - 1);
if ( (unsigned __int64)(Buf1[0] - v40 - 8) > 0x1F )
goto LABEL_99;
}
j_j_free(v40);
v56 = 0i64;
*(_OWORD *)Buf1 = 0i64;
}
v41 = v65;
if ( v65 )
{
if ( ((*((_QWORD *)&v66 + 1) - (_QWORD)v65) & 0xFFFFFFFFFFFFFFFCui64) >= 0x1000 )
{
v41 = (_BYTE *)*((_QWORD *)v65 - 1);
if ( (unsigned __int64)(v65 - v41 - 8) > 0x1F )
goto LABEL_99;
}
j_j_free(v41);
v65 = 0i64;
v66 = 0i64;
}
v42 = v62;
if ( !v62 )
goto LABEL_96;
if ( ((*(_QWORD *)&v63[8] - (_QWORD)v62) & 0xFFFFFFFFFFFFFFFCui64) < 0x1000
|| (v42 = (void *)*((_QWORD *)v62 - 1), (unsigned __int64)((_BYTE *)v62 - (_BYTE *)v42 - 8) <= 0x1F) )
{
j_j_free(v42);
v62 = 0i64;
*(_OWORD *)v63 = 0i64;
LABEL_96:
v43 = v69[0];
if ( v69[0] )
{
if ( ((v70.m128i_i64[0] - (unsigned __int64)v69[0]) & 0xFFFFFFFFFFFFFFFCui64) >= 0x1000 )
{
v43 = (void *)*((_QWORD *)v69[0] - 1);
if ( (unsigned __int64)(v69[0] - v43 - 8) > 0x1F )
goto LABEL_99;
}
j_j_free(v43);
}
return 996i64;
}
LABEL_99:
invalid_parameter_noinfo_noreturn();
}
LOBYTE(Block) = 0;
si128 = _mm_load_si128((const __m128i *)&xmmword_18000EB70);
sub_180006D10(&Block, "35297982045181952350813323813224883208572049226586980", 0x35ui64);
sub_180001530(&v57, &Block);
v2 = &qword_180012038;
v3 = &qword_180012038;
if ( *((_QWORD *)&xmmword_180012048 + 1) >= 0x10ui64 )
v3 = (__int64 *)qword_180012038;
if ( (_QWORD)xmmword_180012048 == 4i64 && *(_DWORD *)v3 == *(_DWORD *)"null" )
{
v71[0] = (char)v57;
sub_180006C40(v72, &v58);
v6 = sub_18000AAB0(
(unsigned int)&Block,
(unsigned int)v71,
v4,
v5,
(_DWORD)Block,
(_DWORD)v45,
si128.m128i_i32[0],
si128.m128i_i32[2],
v47,
v48,
v49,
v50,
v51,
v52,
v53,
(_DWORD)v54,
Buf1[0],
Buf1[1],
v56);
v2 = (__int64 *)sub_180006A70(&qword_180012038, v6);
v1 = 1;
}
sub_180006C40(&v54, v2);
if ( (v1 & 1) != 0 && si128.m128i_i64[1] >= 0x10ui64 )
{
v7 = Block;
if ( (unsigned __int64)(si128.m128i_i64[1] + 1) >= 0x1000 )
{
v7 = (_BYTE *)*((_QWORD *)Block - 1);
if ( (unsigned __int64)((_BYTE *)Block - v7 - 8) > 0x1F )
invalid_parameter_noinfo_noreturn();
}
j_j_free(v7);
}
v8 = sub_18000A7C0(std::cout, "If SKT win S9 champion");
v9 = sub_18000A7C0(v8, "this is real flag");
std::ostream::operator<<(v9, sub_18000A990);
v10 = (__int64 *)&v54;
if ( v56 >= 0x10 )
v10 = v54;
v11 = sub_180007570(std::cout, v10, Buf1[1]);
std::ostream::operator<<(v11, sub_18000A990);
if ( v56 >= 0x10 )
{
v12 = v54;
if ( v56 + 1 >= 0x1000 )
{
v12 = (__int64 *)*(v54 - 1);
if ( (unsigned __int64)((char *)v54 - (char *)v12 - 8) > 0x1F )
LABEL_22:
invalid_parameter_noinfo_noreturn();
}
j_j_free(v12);
}
Buf1[1] = 0i64;
v56 = 15i64;
LOBYTE(v54) = 0;
if ( v60 >= 0x10 )
{
v13 = v58;
if ( v60 + 1 >= 0x1000 )
{
v13 = (_BYTE *)*((_QWORD *)v58 - 1);
if ( (unsigned __int64)((_BYTE *)v58 - v13 - 8) > 0x1F )
goto LABEL_22;
}
j_j_free(v13);
}
return 0xFFFFFFFFi64;
}
发现输入值为0-99某个数时, 会输出flag, 输入空间比较小, 可以写个dll调用程序进行爆破(但时间还是比较长, 不过可以接受, 不然就硬逆算法)
#include "stdafx.h"
#include <stdio.h>
#include <stdlib.h>
#include <iostream>
#include <Windows.h>
using namespace std;
typedef signed __int64(*Dllfunc)(int);
int _tmain(int argc, _TCHAR* argv[])
{
HMODULE module = LoadLibrary(TEXT("D:\\BUUCTF\\REVERSE\\71-90\\[2019redhat]Snake\\Snake\\Snake_Data\\Plugins\\Interface.dll"));
//HMODULE module = LoadLibrary(TEXT("Interface.dll"));
if (module == NULL)
{
printf("load dll library error\n");
return 1;
}
Dllfunc dllfunc = (Dllfunc)GetProcAddress(module, "GameObject");
if (dllfunc == NULL)
{
cout << "get dll function error\n";
return 2;
}
// brute force the gameobject
for (int i = 0; i <= 99; ++i) {
signed __int64 res = dllfunc(i);
cout << i << " " << res << endl;
}
getchar();
// free dll object
FreeLibrary(module);
return 0;
}
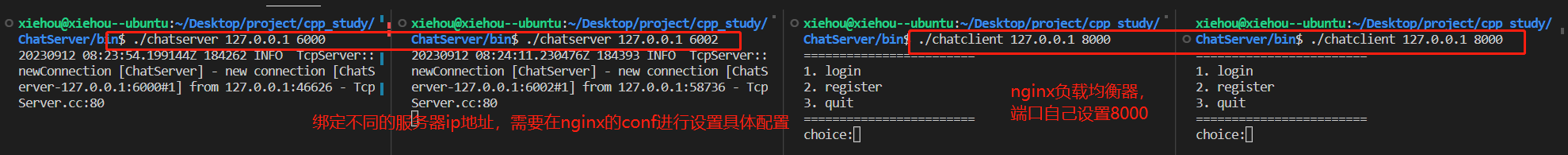
[SCTF2019]Strange apk
APK逆向, JEB打开定位到入口点
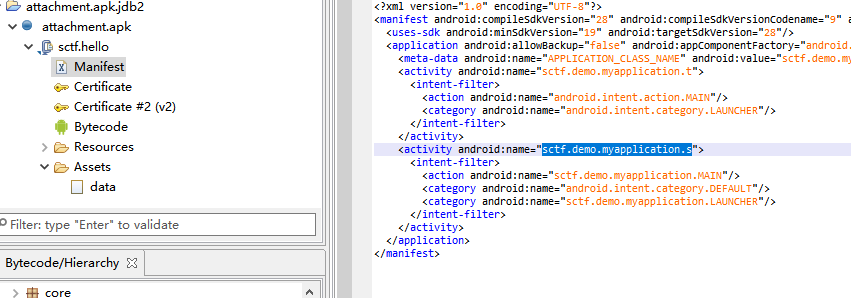
关键函数应该是sctf.demo.myapplication.s但是找不到, 怀疑是动态释放文件, 用反射大师提取dex文件

这里用模拟器提取失败了, 尝试别的路径, 静态分析sctf.hello.c发现解密操作, data文件与syclover进行xor
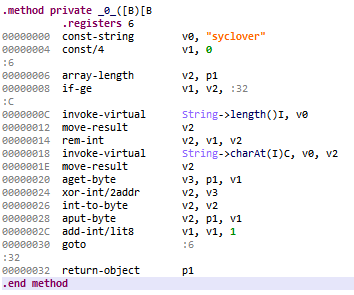
人工SMC
from tqdm import tqdm
def get_byte(v):
return v.to_bytes(1, byteorder='little')
key = "syclover"
with open("./data", "rb") as f:
file_data = f.read()
with open('./smcdata.apk', 'wb') as f:
for i in tqdm(range(len(file_data))):
decode = get_byte(file_data[i] ^ ord(key[i % 8]))
f.write(decode)
print('----- new apk saved -----')
JEB打开新的apk包, 定位到t和c方法
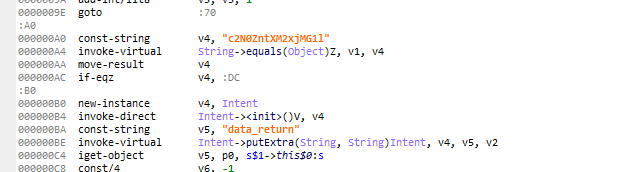
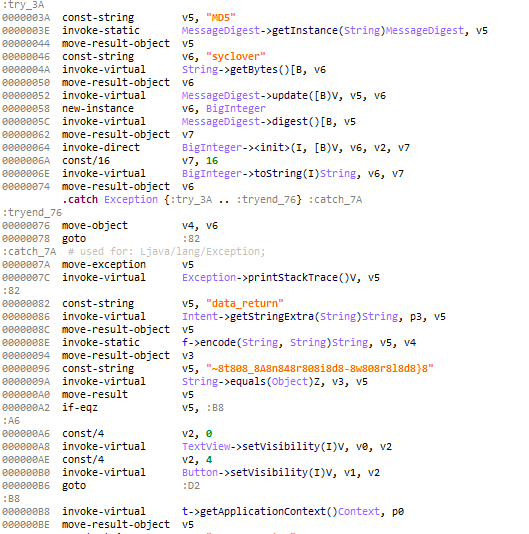
前段flag是base64编码, 后段是取偶数位
整理一下就是flag的前后两段
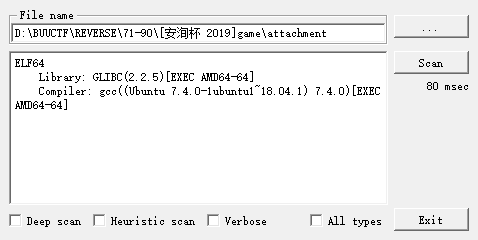
[安洵杯 2019]game
int __cdecl main(int argc, const char **argv, const char **envp)
{
int v3; // eax
__int64 v4; // rsi
int i; // [rsp+2Ch] [rbp-54h]
unsigned int v7; // [rsp+38h] [rbp-48h]
char input[56]; // [rsp+40h] [rbp-40h] BYREF
int v9; // [rsp+78h] [rbp-8h]
int v10; // [rsp+7Ch] [rbp-4h]
v9 = 0;
printf("input your flag:");
gets(input, argv);
v10 = general_inspection((int (*)[9])sudoku);
for ( i = -1804515313; ; i = -303742386 )
{
while ( 1 )
{
while ( i == -2071121728 )
{
v7 = blank_num((int (*)[9])sudoku);
v4 = mem_alloc(v7);
trace(sudoku, v4, v7);
check((int (*)[9])sudoku);
process(input);
valid_check(input);
v9 = 0;
i = -303742386;
}
if ( i != -1804515313 )
break;
v3 = -2071121728;
if ( v10 )
v3 = 664169471;
i = v3;
}
if ( i == -303742386 )
break;
printf("error");
check((int (*)[9])sudoku);
v9 = 0;
}
return v9;
}
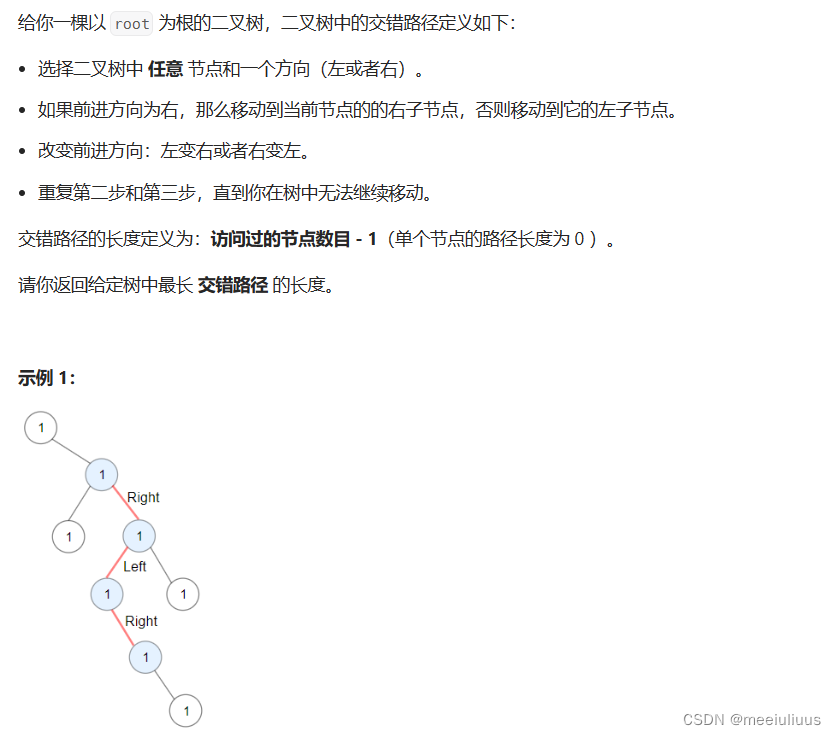
程序对sudoku(数独)进行处理, 然后对input进行处理, 最后是验证, 多个函数都应用了控制流平坦化, 需要deflat(不过逻辑也比较清晰, 主要就是解数独, 可以不用费劲去混淆, 找一个程序自动解或者手动解数独问题就行)
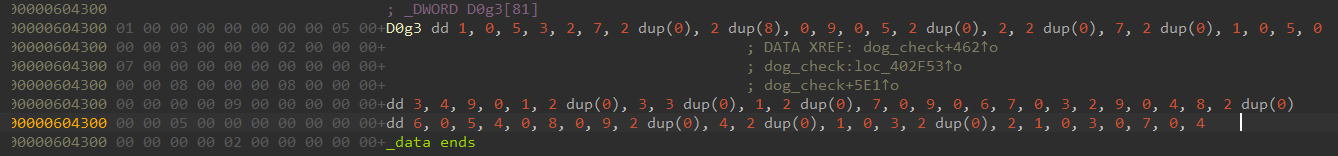
导出数据, 解数独
#include "stdafx.h"
#include <stdio.h>
#include <iostream>
#include <vector>
using namespace std;
std::vector<std::vector<char>> Base = {
{ 1, 0, 5, 3, 2, 7, 0, 0, 8 },
{ 8, 0, 9, 0, 5, 0, 0, 2, 0 },
{ 0, 7, 0, 0, 1, 0, 5, 0, 3 },
{ 4, 9, 0, 1, 0, 0, 3, 0, 0 },
{ 0, 1, 0, 0, 7, 0, 9, 0, 6 },
{ 7, 0, 3, 2, 9, 0, 4, 8, 0 },
{ 0, 6, 0, 5, 4, 0, 8, 0, 9 },
{ 0, 0, 4, 0, 0, 1, 0, 3, 0 },
{ 0, 2, 1, 0, 3, 0, 7, 0, 4 }
};
class Solution {
public:
int row[9][9];
int col[9][9];
int block[9][9];
bool solveSudoku(vector<vector<char>>& board) {
memset(row, 0, sizeof(int) * 81);
memset(col, 0, sizeof(int) * 81);
memset(block, 0, sizeof(int) * 81);
for (int i = 0; i < 9; ++i){//初始化行列以及block,方便后续查询
for (int j = 0; j < 9; ++j){
if (board[i][j] == 0) continue;
int num = board[i][j] - 1;
row[i][num] = col[j][num] = block[i / 3 * 3 + j / 3][num] = 1;
}
}
return dfs(board, 0, 0);
}
bool dfs(vector<vector<char>>& board, int r, int c){
if (r > 8) {
for (int i = 0; i <= 8; ++i) {
for (int j = 0; j <= 8; ++j) {
cout << (int)board[i][j];
}
cout << endl;
}
return true;
}
if (board[r][c] == 0){
for (int i = 0; i < 9; ++i){//枚举可以填入的数字
if (row[r][i] || col[c][i] || block[r / 3 * 3 + c / 3][i])
continue;//不符合要求,该数字已存在
board[r][c] = i + 1;
row[r][i] = col[c][i] = block[r / 3 * 3 + c / 3][i] = 1;
//先判断第一行的9列,然后再判断第二行的9列,一直到最后一行,即r>8
//r+(c+1)/9, (c+1)%9的使用非常巧妙
if (dfs(board, r + (c + 1) / 9, (c + 1) % 9)) return true;
board[r][c] = 0;
row[r][i] = col[c][i] = block[r / 3 * 3 + c / 3][i] = 0;
}
}
else return dfs(board, r + (c + 1) / 9, (c + 1) % 9);
return false;//无解
}
};
int main() {
Solution S;
std::vector<std::vector<char>> matrix = {
{ 1, 0, 5, 3, 2, 7, 0, 0, 8 },
{ 8, 0, 9, 0, 5, 0, 0, 2, 0 },
{ 0, 7, 0, 0, 1, 0, 5, 0, 3 },
{ 4, 9, 0, 1, 0, 0, 3, 0, 0 },
{ 0, 1, 0, 0, 7, 0, 9, 0, 6 },
{ 7, 0, 3, 2, 9, 0, 4, 8, 0 },
{ 0, 6, 0, 5, 4, 0, 8, 0, 9 },
{ 0, 0, 4, 0, 0, 1, 0, 3, 0 },
{ 0, 2, 1, 0, 3, 0, 7, 0, 4 }
};
cout << S.solveSudoku(matrix) << endl;
for (int i = 0; i < 9; ++i) {
for (int j = 0; j < 9; ++j) {
if (Base[i][j] == 0)
cout << (int)matrix[i][j];
}
}
cout << endl;
getchar();
}
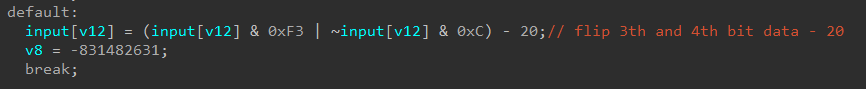
process 做了三步处理
交换奇偶位
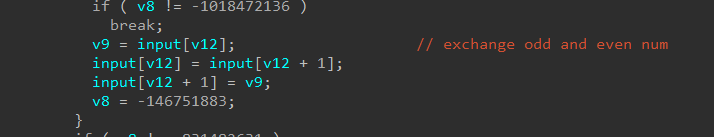
交换前半和后半数据
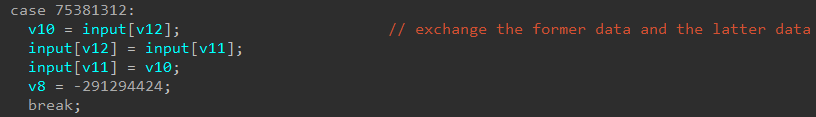
反转第3,4位数据并-20
逆
s = '4693641762894685722843556137219876255986'
flag = ''
tmp = [0 for _ in range(len(s))]
for i in range(len(s)):
tmp[i] = (ord(s[i]) + 20) ^ 0x0C & 0xFF
idx1 = 0
idx2 = len(s) // 2
while idx2 < len(s):
tmp[idx1], tmp[idx2] = tmp[idx2], tmp[idx1]
idx2 += 1
idx1 += 1
for i in range(0, len(s), 2):
tmp[i], tmp[i + 1] = tmp[i + 1], tmp[i]
for i in range(len(tmp)):
flag += chr(tmp[i])
print('flag{{{}}}'.format(flag))